Microsoft warns {that a} menace actor tracked as Storm-0501 has advanced its operations, shifting away from encrypting units with ransomware to specializing in cloud-based encryption, information theft, and extortion.
The hackers now abuse native cloud options to exfiltrate information, wipe backups, and destroy storage accounts, thereby making use of stress and extorting victims with out deploying conventional ransomware encryption instruments.
Storm-0501 is a menace actor who has been lively since not less than 2021, deploying the Sabbath ransomware in assaults in opposition to organizations worldwide. Over time, the menace actor joined varied ransomware-as-a-service (RaaS) platforms, the place they used encryptors from Hive, BlackCat (ALPHV), Hunters Worldwide, LockBit, and, extra not too long ago, Embargo ransomware.
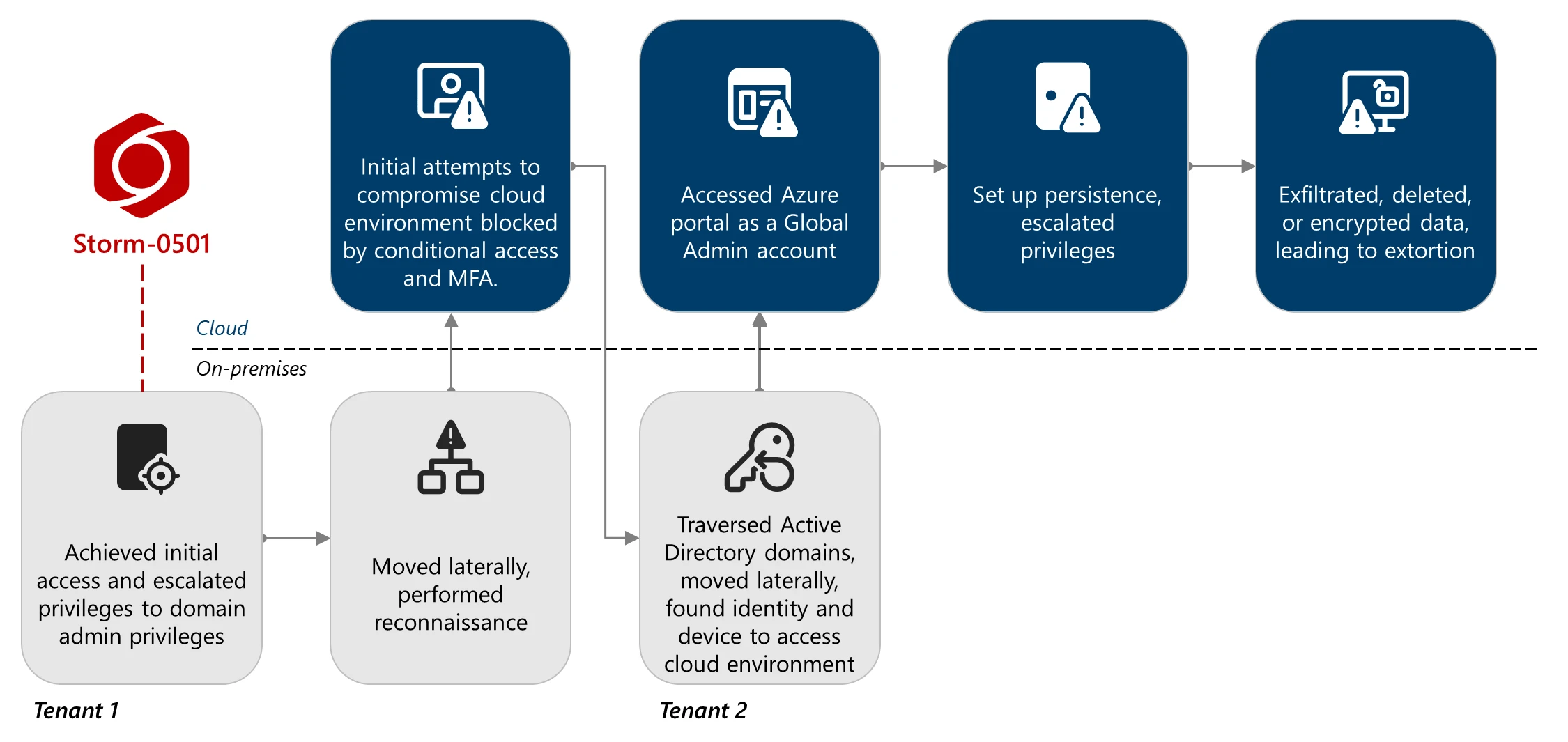
In September 2024, Microsoft detailed how Storm-0501 prolonged its operations into hybrid cloud environments, pivoting from compromising Energetic Listing to Entra ID tenants. Throughout these assaults, the menace actors both created persistent backdoors by malicious federated domains or encrypted on-premises units utilizing ransomware, akin to Embargo.
A brand new report by Microsoft at this time outlines a shift in techniques, with Storm-0501 not counting on on-premises encryption and as a substitute conducting assaults purely within the cloud.
“In contrast to conventional on-premises ransomware, the place the menace actor usually deploys malware to encrypt important information throughout endpoints throughout the compromised community after which negotiates for a decryption key, cloud-based ransomware introduces a elementary shift,” reads the report by Microsoft Risk Intelligence.
“Leveraging cloud-native capabilities, Storm-0501 quickly exfiltrates massive volumes of information, destroys information and backups throughout the sufferer atmosphere, and calls for ransom—all with out counting on conventional malware deployment.”
Cloud-based ransomware assaults
In current assaults noticed by Microsoft, the hackers compromised a number of Energetic Listing domains and Entra tenants by exploiting gaps in Microsoft Defender deployments.
Storm-0501 then used stolen Listing Synchronization Accounts (DSAs) to enumerate customers, roles, and Azure sources with instruments akin to AzureHound. The attackers finally found a International Administrator account that lacked multifactor authentication, permitting them to reset its password and achieve full administrative management.
With these privileges, they established persistence by including malicious federated domains beneath their management, enabling them to impersonate virtually any consumer and bypass MFA protections within the area.
Microsoft says they escalated their entry additional into Azure by abusing the Microsoft.Authorization/elevateAccess/motion, which allowed them to finally assign themselves to Proprietor roles, successfully taking on the sufferer’s complete Azure atmosphere.
Supply: Microsoft
As soon as answerable for the cloud atmosphere, Storm-0501 started disabling defenses and stealing delicate information from Azure Storage accounts. The menace actors additionally tried to destroy storage snapshots, restore factors, Restoration Companies vaults, and storage accounts to forestall the goal from recovering information free of charge.
When the menace actor could not delete information from restoration companies, they utilized cloud-based encryption by creating new Key Vaults and customer-managed keys, successfully encrypting the info with new keys and making it inaccessible to the corporate except they pay a ransom.
After stealing information, destroying backups, or encrypting cloud information, Storm-0501 moved to the extortion section, contacting victims by Microsoft Groups utilizing compromised accounts to ship ransom calls for.
Microsoft’s report shares safety recommendation, Microsoft Defender XDR detections, and looking queries that may assist discover and detect the techniques utilized by this menace actor.
As ransomware encryptors are more and more blocked earlier than they will encrypt units, we might even see different menace actors shift away from on-premise encryption to cloud-based information theft and encryption, which can be more durable to detect and block.


