The ShinyHunters extortion gang claims it’s behind a wave of ongoing voice phishing assaults focusing on single sign-on (SSO) accounts at Okta, Microsoft, and Google, enabling menace actors to breach company SaaS platforms and steal firm information for extortion.
In these assaults, menace actors impersonate IT help and name staff, tricking them into coming into their credentials and multi-factor authentication (MFA) codes on phishing websites that impersonate firm login portals.
As soon as compromised, the attackers achieve entry to the sufferer’s SSO account, which might present entry to different linked enterprise purposes and companies.
SSO companies from Okta, Microsoft Entra, and Google allow corporations to hyperlink third-party purposes right into a single authentication move, giving staff entry to cloud companies, inside instruments, and enterprise platforms with a single login.
These SSO dashboards sometimes record all linked companies, making a compromised account a gateway into company methods and information.
Platforms generally linked via SSO embrace Salesforce, Microsoft 365, Google Workspace, Dropbox, Adobe, SAP, Slack, Zendesk, Atlassian, and lots of others.
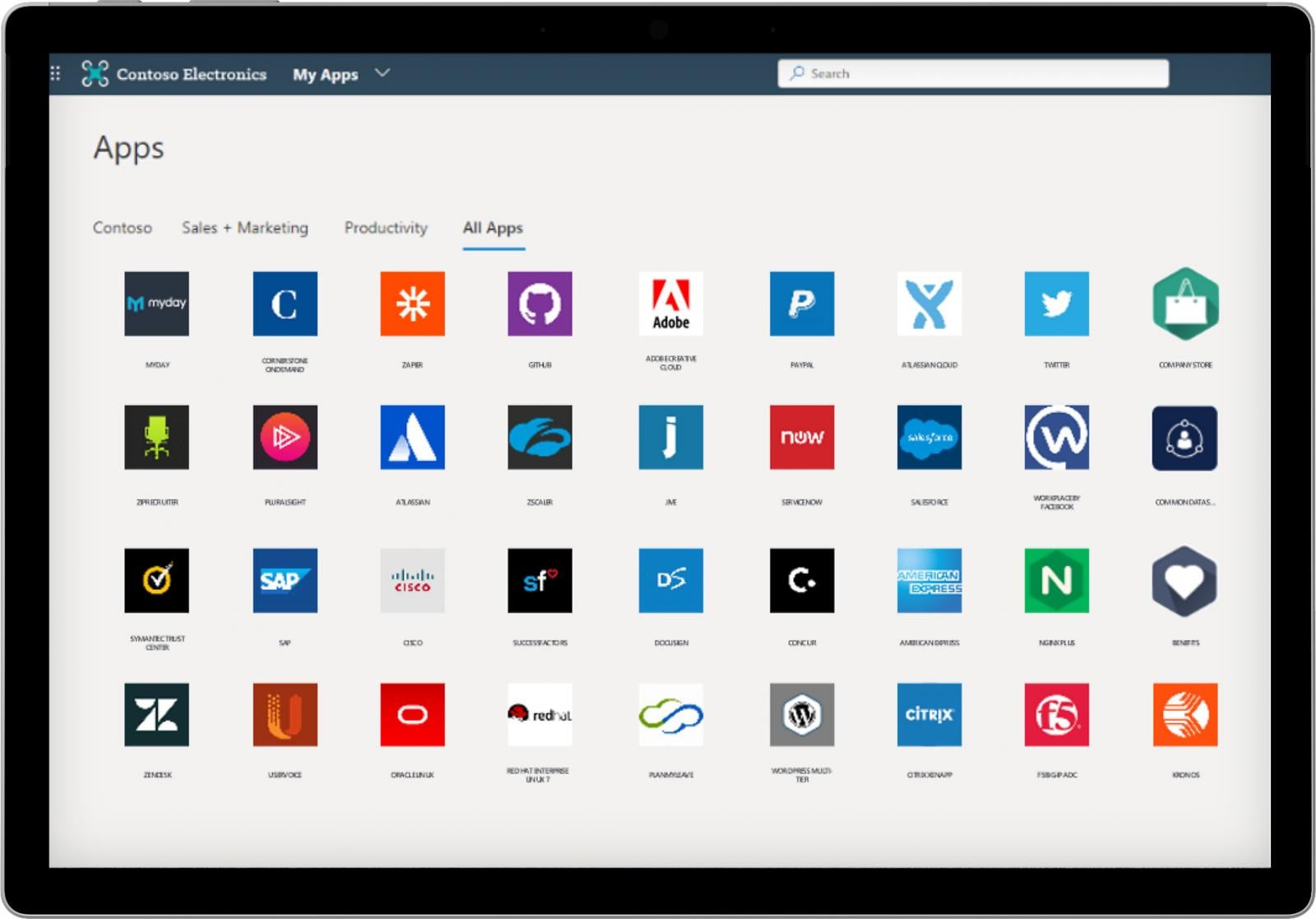
Supply: Microsoft
Vishing assaults used for information theft
As first reported by BleepingComputer, menace actors have been finishing up these assaults by calling staff and posing as IT workers, utilizing social engineering to persuade them to log into phishing pages and full MFA challenges in actual time.
After having access to a sufferer’s SSO account, the attackers browse the record of linked purposes and start harvesting information from the platforms obtainable to that consumer.
BleepingComputer is conscious of a number of corporations focused in these assaults which have since obtained extortion calls for signed by ShinyHunters, indicating that the group was behind the intrusions.
BleepingComputer contacted Okta earlier this week concerning the breaches, however the firm declined to touch upon the information theft assaults.
Nonetheless, Okta launched a report yesterday describing the phishing kits utilized in these voice-based assaults, which match what BleepingComputer has been advised.
Based on Okta, the phishing kits embrace a web-based management panel that enables attackers to dynamically change what a sufferer sees on a phishing website whereas talking to them on the telephone. This permits menace actors to information victims via every step of the login and MFA authentication course of.
If the attackers enter stolen credentials into the actual service and are prompted for MFA, they’ll show new dialog packing containers on the phishing website in actual time to instruct a sufferer to approve a push notification, enter a TOTP code, or carry out different authentication steps.
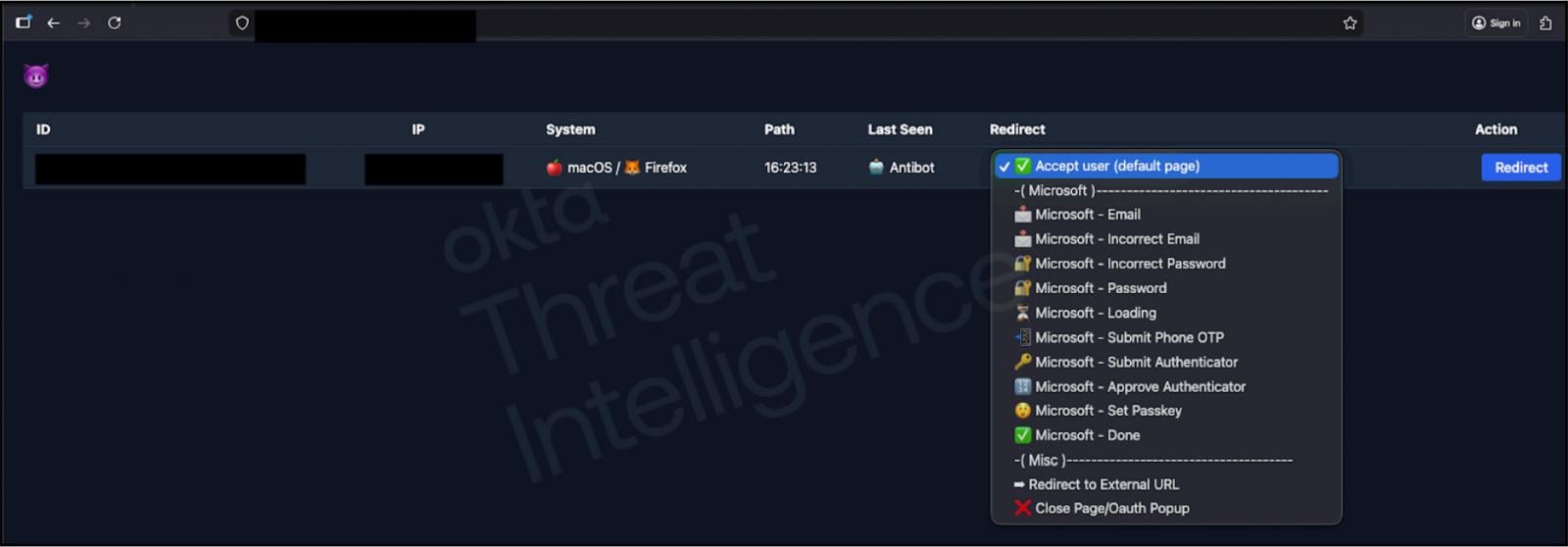
Supply: Okta
ShinyHunters declare accountability
Whereas ShinyHunters declined to touch upon the assaults final night time, the group confirmed to BleepingComputer this morning that it’s accountable for among the social engineering assaults.
“We affirm we’re behind the assaults,” ShinyHunters advised BleepingComputer. “We’re unable to share additional particulars presently, in addition to the truth that Salesforce stays our major curiosity and goal, the remaining are benefactors.”
The group additionally confirmed different features of BleepingComputer’s reporting, together with particulars concerning the phishing infrastructure and domains used within the marketing campaign. Nonetheless, it disputed {that a} screenshot of a phishing equipment command-and-control server shared by Okta was for its platform, claiming as an alternative that theirs was constructed in-house.
ShinyHunters claimed it’s focusing on not solely Okta but additionally Microsoft Entra and Google SSO platforms.
Microsoft stated it has nothing to share presently, and Google stated it had no proof its merchandise had been being abused within the marketing campaign.
“Presently, now we have no indication that Google itself or its merchandise are affected by this marketing campaign,” a Google spokesperson advised BleepingComputer.
ShinyHunters claims to be utilizing information stolen in earlier breaches, such because the widespread Salesforce information theft assaults, to determine and make contact with staff. This information consists of telephone numbers, job titles, names, and different particulars used to make the social-engineering calls extra convincing.
Final night time, the group relaunched its Tor information leak website, which presently lists breaches at SoundCloud, Betterment, and Crunchbase.
SoundCloud beforehand disclosed an information breach in December 2025, whereas Betterment confirmed this month that its electronic mail platform had been abused to ship cryptocurrency scams and that information was stolen.
Crunchbase, which had not beforehand disclosed a breach, confirmed at this time that information was stolen from its company community.
“Crunchbase detected a cybersecurity incident the place a menace actor exfiltrated sure paperwork from our company community,” an organization spokesperson advised BleepingComputer. “No enterprise operations have been disrupted by this incident. We now have contained the incident and our methods are safe.”
“Upon detecting the incident we engaged cybersecurity consultants and contacted federal legislation enforcement. We’re reviewing the impacted data to find out if any notifications are required in step with relevant authorized necessities.”



