A beforehand undocumented ransomware payload named NailaoLocker has been noticed in assaults concentrating on European healthcare organizations between June and October 2024.
The assaults exploited CVE-2024-24919, a Examine Level Safety Gateway vulnerability, to realize entry to focused networks and deploy the ShadowPad and PlugX malware, two households tightly related to Chinese language state-sponsored menace teams.
Orange Cyberdefense CERT hyperlinks the assaults to Chinese language cyber-espionage ways, although there’s not sufficient proof to attribute them to particular teams.
NailaoLocker particulars
Orange’s researchers report that NailaoLocker is a comparatively unsophisticated ransomware pressure in comparison with essentially the most distinguished households within the house.
The rationale why Orange sees NailaoLocker as a moderately primary ransomware is that, it doesn’t terminate safety processes or working providers, it lacks anti-debugging and sandbox evasion mechanisms, and doesn’t scan community shares.
“Written in C++, NailaoLocker is comparatively unsophisticated and poorly designed, seemingly not meant to ensure full encryption,” mentions Orange.
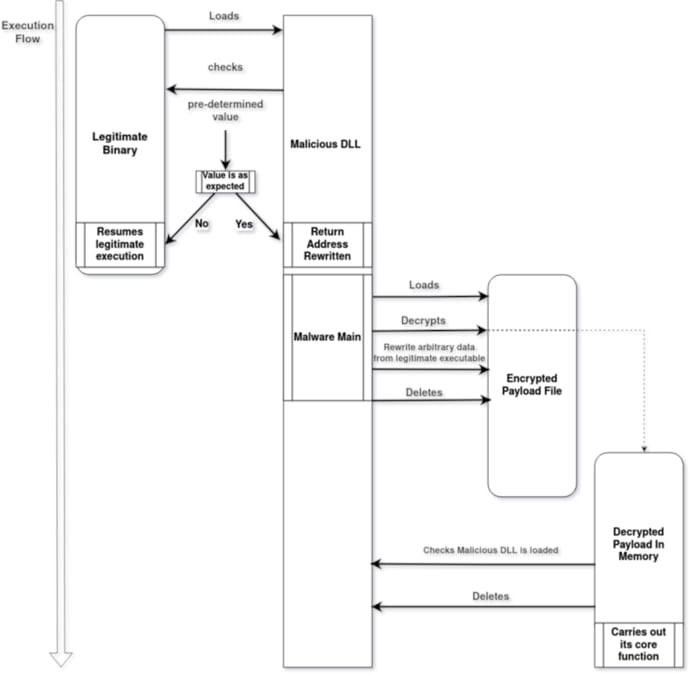
The malware is deployed heading in the right direction programs by way of DLL sideloading (sensapi.dll) involving a professional and signed executable (usysdiag.exe).
The malware loader (NailaoLoader) verifies the setting by performing reminiscence tackle checks after which decrypts the primary payload (usysdiag.exe.dat) and masses it into reminiscence.
Supply: Orange CERT
Subsequent, the NailaoLocker prompts and begins encrypting recordsdata utilizing an AES-256-CTR scheme, appending the “.locked” extension to encrypted recordsdata.
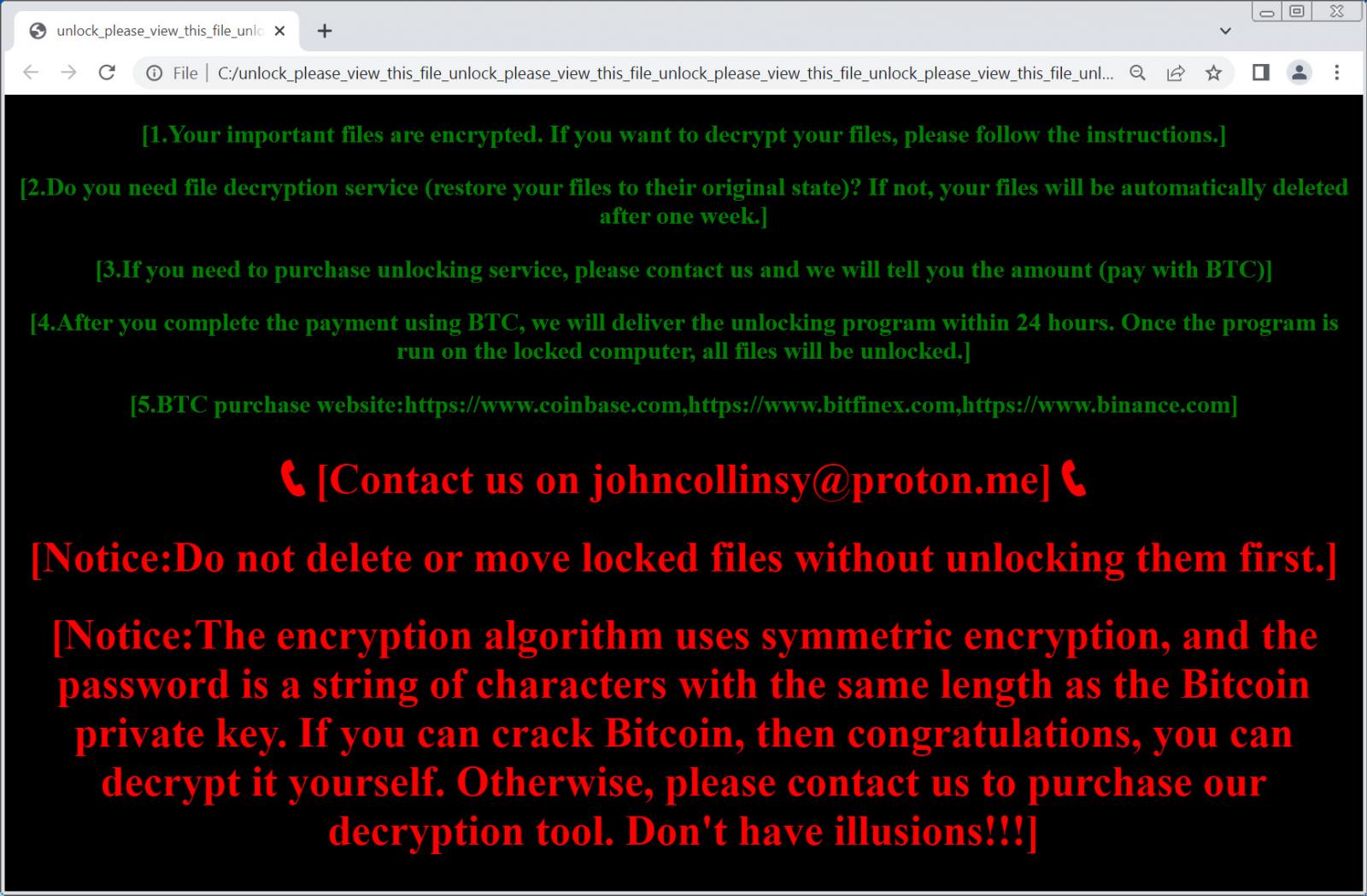
After the encryption is completed, the ransomware drops an HTML ransom observe with the very unusually lengthy filename of “unlock_please_view_this_file_unlock_please_view_this_file_unlock_please_view_this_file_unlock_please_view_this_file_unlock_please_view_this_file_unlock_please_view_this_file_unlock_please.html.”
Supply: Orange CERT
This ransom observe instructs the victims to contact them at a disposable ProtonMail tackle, which, in just a few instances seen by BleepingComputer, was johncollinsy@proton[.]me.
The ransom observe doesn’t point out that knowledge was stolen, which is odd for many fashionable ransomware operations.
Espionage and ransomware mixed
Investigating deeper, Orange says they discovered some overlap between the content material of the ransom observe and a ransomware instrument bought by a cybercrime group named Kodex Softwares (previously Evil Extractor). Nonetheless, there have been no direct code overlaps, making the connection blurry.
Orange has shared a number of hypotheses for the assaults, together with false flag operations meant to distract, strategic knowledge theft operations doubled with income technology, and, extra seemingly, a Chinese language cyberespionage group “moonlighting” on the aspect to earn some cash.
Solely final week, Symantec reported about suspected Emperor Dragonfly (a.ok.a. Bronze Starlight) operatives deploying RA World ransomware towards Asian software program corporations and demanding a ransom of $2 million.
In comparison with North Korean actors who’re identified to pursue a number of objectives in parallel, together with monetary beneficial properties by way of ransomware assaults, Chinese language state-backed actors have not adopted this method, so the shift in ways is regarding.

