Menace actors claiming to characterize the Medusa ransomware gang tempted a BBC correspondent to turn out to be an insider risk by providing a big amount of cash.
Cybersecurity correspondent Joe Tidy revealed in a story on the BBC that the hackers wished to make use of his laptop computer to breach the British public-service broadcaster’s community after which ask for a ransom.
As soon as they bought entry to the BBC’s inside programs, the risk actor deliberate to steal useful information and maintain the group to ransom. Not less than 15% of the paid ransom would go to Tidy for offering preliminary entry.
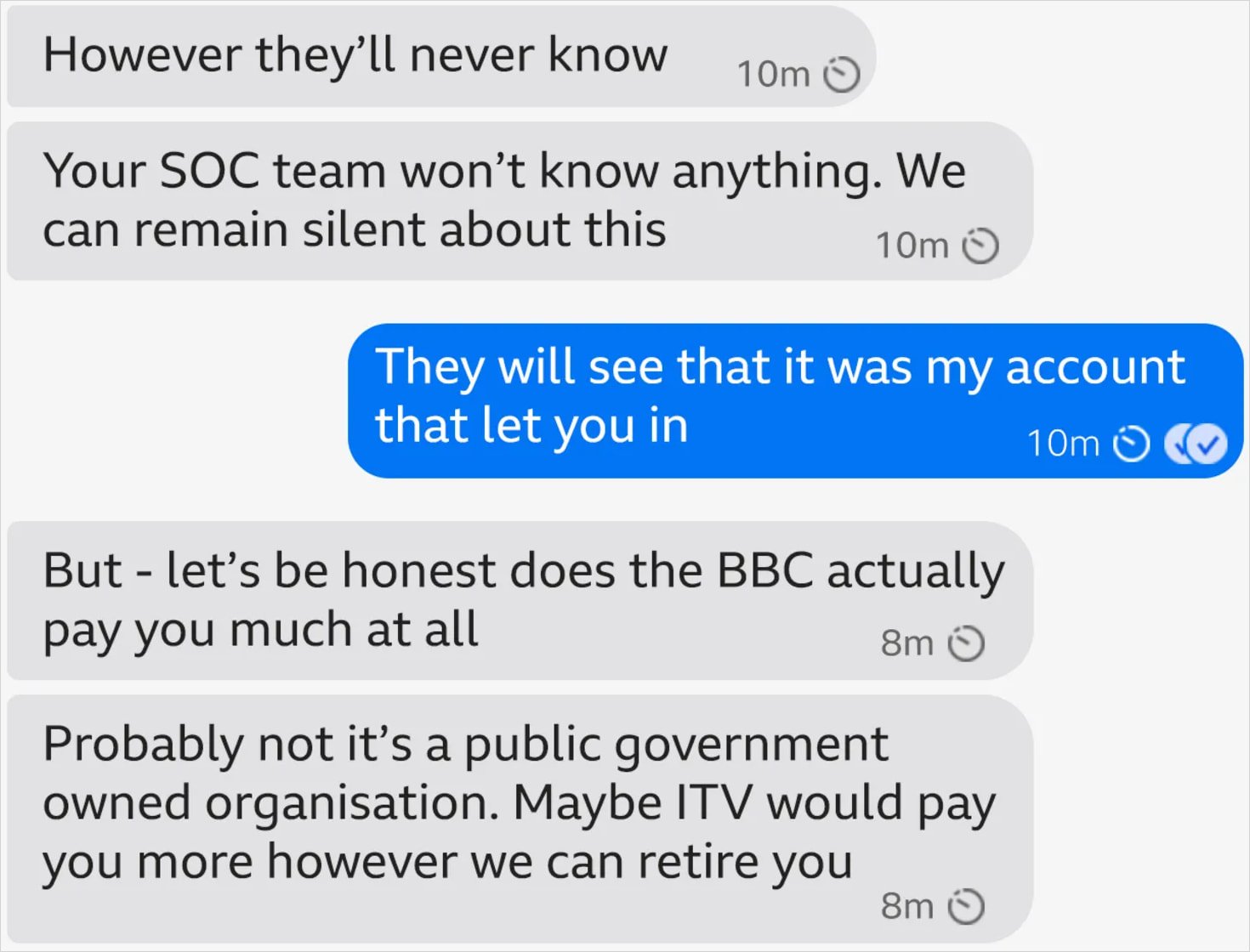
Tidy says he was contacted in July over Sign by a cybercriminal named “Syndicate” (“Syn”), who initially supplied him 15% of the paid ransom if he offered Medusa entry to BBC programs.
Syn later tried to sweeten the supply with a further 10%, saying that “their crew might demand a ransom within the tens of tens of millions in the event that they efficiently infiltrated the company.”
In continued makes an attempt to lure Tidy to their aspect, Syn mentioned “that their crew might demand a ransom within the tens of tens of millions in the event that they efficiently infiltrated the company,” which might imply that the journalist might by no means work once more, residing off the ransom minimize.
Supply: BBC
Medusa ransomware is an operation that emerged in January 2021 and gained a repute with double-extortion assaults and the launch of an extortion portal in 2023.
In March, CISA printed a report on Medusa, attributing to the gang greater than 300 assaults on essential infrastructure organizations in the USA.
In keeping with the company, Medusa’s core operators recruit preliminary entry brokers in cybercrime boards and darknet marketplaces, they usually deal with the post-compromise part.
Tidy stories that the alleged ransomware group’s consultant promised anonymity if he helped, citing a number of previous instances that made headlines, which they claimed concerned a rogue insider giving Medusa easy accessibility to the goal’s networks.
Underpaid, disgruntled, or just unethical employees have precipitated tens of millions in damages in alternate for a few hundred USD, and a few risk actors depend on that.
Ransomware gangs like LockBit have been exploring the potential of rogue staff prepared to promote their entry for a number of years now.
Syn even tried to influence the journalist by providing 0.5 BTC (at the moment a little bit over $55,000) in escrow on a hacker discussion board earlier than the hack even began.
“We aren’t bluffing or joking – we do not have a goal media sensible we’re just for cash and cash solely and certainly one of our primary managers wished me to achieve out to you,” Syn instructed Tidy over Sign.
Tidy, who covers cybersecurity information, believes the risk actors possible mistook him for a cybersecurity worker on the BBC with excessive privilege entry.
Syn pressed the journalist to execute a script, however when Tidy stalled, the journalist’s cellphone was flooded with two-factor authentication requests.
This can be a tactic referred to as MFA bombing, MFA fatigue, or MFA spam, the place hackers automate log in makes an attempt with the sufferer’s credentials to generate a barrage of authentication requests till the goal provides up and permits the login.
Tidy did not hand over, although. He contacted BBC’s data safety crew and, as a precaution, was disconnected fully from the group’s infrastructure.
In a later message, the alleged Medusa consultant apologized for the login requests and mentioned that their supply was nonetheless accessible for a number of days. Nevertheless, when the journalist did not reply for a number of days, the risk actor deleted their Sign account.


