Overview:
Knowledge exfiltration is among the most severe safety dangers organizations face in the present day. It may expose delicate buyer or enterprise info, resulting in reputational harm and regulatory penalties underneath legal guidelines like GDPR. The issue is that exfiltration can occur in some ways—via exterior attackers, insider errors, or malicious insiders and is usually laborious to detect till the harm is finished.
Safety and cloud groups should defend towards these dangers whereas enabling staff to make use of SaaS instruments and cloud providers to do their work. With lots of of providers in play, analyzing each potential exfiltration path can really feel overwhelming.
On this weblog, we introduce a unified method to defending towards knowledge exfiltration on Databricks throughout AWS, Azure, and GCP. We begin with three core safety necessities that type a framework for assessing threat. We then map these necessities to nineteen sensible controls, organized by precedence, you can apply whether or not you’re constructing your first Databricks safety technique or strengthening an current one.
A Framework for Categorizing Knowledge Exfiltration Safety Controls:
We’ll begin by defining the three core enterprise necessities that may type a complete framework for mapping related knowledge exfiltration safety controls:
- All consumer/shopper entry is from trusted areas and strongly authenticated:
- All entry have to be authenticated and originate from trusted areas, guaranteeing customers and shoppers can solely attain programs from accepted networks via verified id controls.
- No entry to untrusted storage areas, public, or non-public endpoints:
- Compute engines should solely entry administrator-approved storage and endpoints, stopping knowledge exfiltration to unauthorized locations whereas defending towards malicious providers.
- All knowledge entry is from trusted workloads:
- Storage programs should solely settle for entry from accepted compute sources, making a last verification layer even when credentials are compromised on untrusted programs.
General, these three necessities working collectively deal with consumer behaviors that would facilitate unauthorized knowledge motion outdoors the group’s safety perimeter. Nevertheless, it’s important that we consider every of those three necessities as an entire. If there’s a hole in controls in one of many necessities, it hampers the safety posture of all the structure.
Within the following sections, we’ll study particular controls mapped to every particular person requirement.
Knowledge Exfiltration Safety Methods for Databricks:
For readability and ease, every management underneath the related requirement is organized by: structure element, threat state of affairs, corresponding mitigation, implementation precedence, and cloud-specific documentation.
The legend for the prioritization to implement is as follows:
- HIGH – Implement instantly. These controls are important for all Databricks deployments no matter atmosphere or use case.
- MEDIUM – Assess based mostly in your group’s threat tolerance and particular Databricks utilization patterns.
- LOW – Consider based mostly on workspace atmosphere (growth, QA, manufacturing) and organizational safety necessities.
NOTE: Earlier than implementing controls, make sure you’re on the proper platform tier for that characteristic. Required tiers are famous within the related documentation hyperlinks.
All Person and Shopper Entry is From Trusted Areas and Strongly Authenticated:
Abstract:
Customers should authenticate via accepted strategies and entry Databricks solely from approved networks. This establishes the muse for mitigating unauthorized entry.
Structure parts coated on this part embody: Identification Supplier, Account Console, and Workspace.
Why Is This Requirement Necessary?
Making certain that every one customers and shoppers join from trusted areas and are strongly authenticated is the primary line of protection for mitigating knowledge exfiltration. If an information platform can not affirm that entry requests originate from accepted networks or that customers are validated via a number of layers of authentication (reminiscent of MFA), then each subsequent management is weakened, leaving the atmosphere weak.
| Structure Element: | Threat: | Management: | Precedence to Implement: | Documentation: |
|---|---|---|---|---|
| Identification Supplier and Account Console | Customers could try and bypass company id controls by utilizing private accounts or non-single-sign-on (SSO) login strategies to entry Databricks workspaces. | Implement Unified Login to use single-sign on (SSO) safety throughout all, or chosen, workspaces within the Databricks account.
NOTE: We suggest enabling multi-factor authentication (MFA) inside your Identification Supplier. When you can not use SSO, you could configure MFA instantly in Databricks. |
HIGH | AWS, Azure, GCP |
| Identification Supplier | Former customers could try and log in to the workspace following a departure from the corporate. | Implement SCIM or Computerized Identification Administration to deal with the automated de-provisioning of customers. | HIGH | AWS, Azure, GCP |
| Account Console | Customers could try and entry the account console from unauthorized networks. | Implement account console IP entry management lists (ACLs) | HIGH | AWS, Azure, GCP |
| Workspace | Customers could try and entry the workspace from unauthorized networks. | Implement community entry controls utilizing one of many following approaches: – Personal Connectivity – IP ACLs |
HIGH | Personal Connectivity: AWS, Azure, GCP |
No Entry to Untrusted Storage Areas, Public, or Personal Endpoints:
Abstract:
Compute sources should solely entry pre-approved storage areas and endpoints. This mitigates knowledge exfiltration to unauthorized locations and protects towards malicious exterior providers.
Structure parts coated on this part embody: Traditional Compute, Serverless Compute, and Unity Catalog.
Why Is This Requirement Necessary?
The requirement for compute to entry solely trusted storage areas and endpoints is foundational to preserving a company’s safety perimeter. Historically, firewalls served as the first safeguard towards knowledge exfiltration, however as cloud providers and SaaS integration factors develop, organizations should account for all potential vectors that may very well be exploited to maneuver knowledge to untrusted locations.
| Structure Element: | Threat: | Management: | Precedence to Implement: | Documentation: |
|---|---|---|---|---|
| Traditional Compute | Customers could execute code that interacts with malicious or unapproved public endpoints. | Implement an egress firewall in your cloud supplier community to filter outbound visitors to solely accepted domains and IP addresses. In any other case, for sure cloud suppliers, take away all outbound entry to the web. | HIGH | AWS, Azure, GCP |
| Traditional Compute | Customers could execute code that exfiltrates knowledge to unmonitored cloud sources by leveraging non-public community connectivity to entry storage accounts or providers outdoors their meant scope. | Implement coverage pushed entry (e.g., VPC endpoint insurance policies, service endpoint insurance policies, and many others.) and community segmentation to limit cluster entry to solely pre-approved cloud sources and storage accounts. | HIGH | AWS, Azure, GCP |
| Serverless Compute | Customers could execute code that exfiltrates knowledge to unauthorized exterior providers or malicious endpoints over public web connections. | Implement serverless egress controls to limit outbound visitors to solely pre-approved storage accounts and verified public endpoints. | HIGH | AWS, Azure, GCP |
| Unity Catalog | Customers could try and entry untrusted storage accounts to exfiltrate knowledge outdoors the group’s accepted knowledge perimeter. | Solely permit admins to create storage credentials and exterior areas. Give customers permissions to make use of accepted Unity Catalog securables.
Observe the precept of least privilege for cloud entry insurance policies (e.g. IAM) for storage credentials. |
HIGH | AWS, Azure, GCP |
| Unity Catalog | Customers could try and entry untrusted databases to learn and write unauthorized knowledge. | Solely permit admins to create database connections utilizing Lakehouse Federation. Give customers permissions to make use of accepted connections. | MEDIUM | AWS, Azure, GCP |
| Unity Catalog | Customers could try and entry untrusted non-storage cloud sources (e.g., managed streaming providers) utilizing unauthorized credentials. | Solely permit admins to create service credentials for exterior cloud providers. Give customers permissions to make use of accepted service credentials.
Observe the precept of least privilege for cloud entry insurance policies (e.g. IAM) for service credentials. |
MEDIUM | AWS, Azure, GCP |
All Knowledge Entry is From Trusted Workloads:
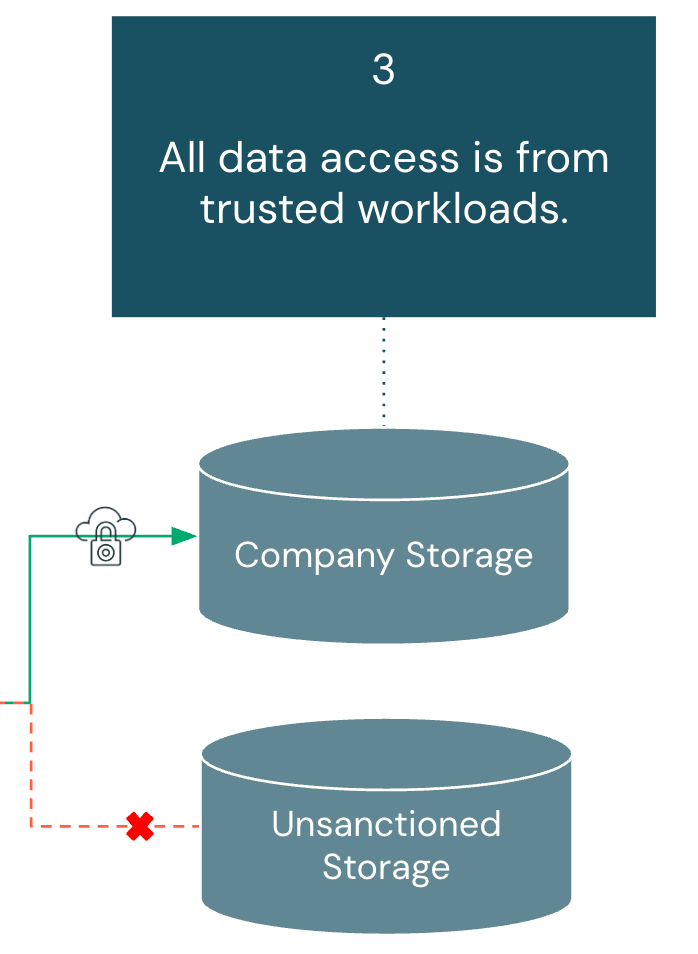
Abstract:
Knowledge storage should solely settle for entry from accepted Databricks workloads and trusted compute sources. This mitigates unauthorized entry to each buyer knowledge and workspace artifacts like notebooks and question outcomes. Structure parts coated on this part embody: Storage Account, Serverless Compute, Unity Catalog, and Workspace Settings.
Why Is This Requirement Necessary?
As organizations undertake extra SaaS instruments, knowledge requests more and more originate outdoors conventional cloud networks. These requests could contain cloud object shops, databases, or streaming platforms, every creating potential avenues for exfiltration. To scale back this threat, entry have to be constantly enforced via accepted governance layers and restricted to sanctioned knowledge tooling, guaranteeing knowledge is used inside managed environments.
| Structure Element: | Threat: | Management: | Precedence to Implement: | Documentation: |
|---|---|---|---|---|
| Storage Account | Customers could try and entry cloud supplier storage accounts via non-Unity Catalog ruled compute. | Implement firewalls or bucket insurance policies on storage accounts to solely settle for visitors from accepted supply locations. | HIGH | AWS, Azure, GCP |
| Unity Catalog | Customers could try and learn and write knowledge from totally different environments (e.g., growth workspace studying manufacturing knowledge) | Implement workspace bindings for catalogs. | HIGH | AWS, Azure, GCP |
| Serverless Compute | Customers could require entry to cloud sources via serverless compute, forcing directors to reveal inside providers to broader community entry than meant. | Implement non-public endpoints guidelines within the Community Connectivity Configuration object [AWS, Azure, GCP [Not currently available] | MEDIUM | AWS, Azure, GCP [Not currently available] |
| Workspace Settings | Customers could try and obtain pocket book outcomes to their native machine. | Disable Pocket book outcomes obtain within the Workspace admin safety setting. | LOW | AWS, Azure, GCP |
| Workspace Settings | Customers could try and obtain quantity recordsdata to their native machine. | Disable Quantity Information Obtain within the Workspace admin safety setting. | LOW | Documentation not obtainable. Toggle to disable discovered inside workspace admin safety settings underneath egress and ingress. |
| Workspace Settings | Customers could try and export notebooks or recordsdata from the workspace to their native machine. | Disable Pocket book and File exporting within the Workspace admin safety setting. | LOW | AWS, Azure, GCP |
| Workspace Settings | Customers could try and obtain SQL outcomes to their native machine. | Disable SQL outcomes obtain within the Workspace admin safety setting. | LOW | AWS, Azure, GCP |
| Workspace Settings | Customers could try and obtain MLflow run artifacts to their native machine. | Disable MLflow run artifact obtain within the Workspace admin safety setting. | LOW | Documentation not obtainable. Toggle to disable discovered inside workspace admin safety settings underneath egress and ingress. |
| Workspace Settings | Customers could try to repeat tabular knowledge to their clipboard via the UI. | Disable Outcomes desk clipboard characteristic within the Workspace admin safety setting. | LOW | AWS, Azure, GCP |
Proactive Knowledge Exfiltration Monitoring:
Whereas the three core enterprise necessities allow us to set up the preventive controls essential to safe your Databricks Knowledge Intelligence Platform, monitoring offers the detection capabilities wanted to validate these controls are functioning as meant. Even with sturdy authentication, restricted compute entry, and secured storage, you will want visibility into consumer behaviors that would point out makes an attempt to avoid your established controls.
Databricks gives complete system tables for entry management monitoring [AWS, Azure, GCP]. Utilizing these system tables, prospects can arrange alerts based mostly on doubtlessly suspicious actions to enhance current controls on the workspace.
For out-of-the-box queries that may drive actionable insights, go to this weblog submit: Enhance Lakehouse Safety Monitoring utilizing System Tables in Databricks Unity Catalog. Cloud-specific logs [AWS, Azure, GCP] may be ingested and analyzed to enhance the information from Databricks system tables.
Conclusion:
Now that we have coated the dangers and controls related to every safety requirement that make up this framework, we have now a unified method to mitigate knowledge exfiltration in your Databricks deployment.
Whereas stopping the unauthorized motion of information is an on a regular basis job, this can present your customers with a basis to develop and innovate whereas defending one among your organization’s most essential property: your knowledge.
To proceed the journey of securing your Knowledge Intelligence Platform, we extremely suggest visiting the Safety and Belief Heart for a holistic view of Safety Greatest Practices on Databricks.
- The Greatest Observe guides present an in depth overview of the principle safety controls we suggest for typical and extremely safe environments.
- The Safety Reference Structure – Terraform Templates make it simple to routinely create Databricks environments that comply with the perfect practices outlined on this weblog.
- The Safety Evaluation Software constantly screens the safety posture of your Databricks Knowledge Intelligence Platform in accordance with greatest practices.

