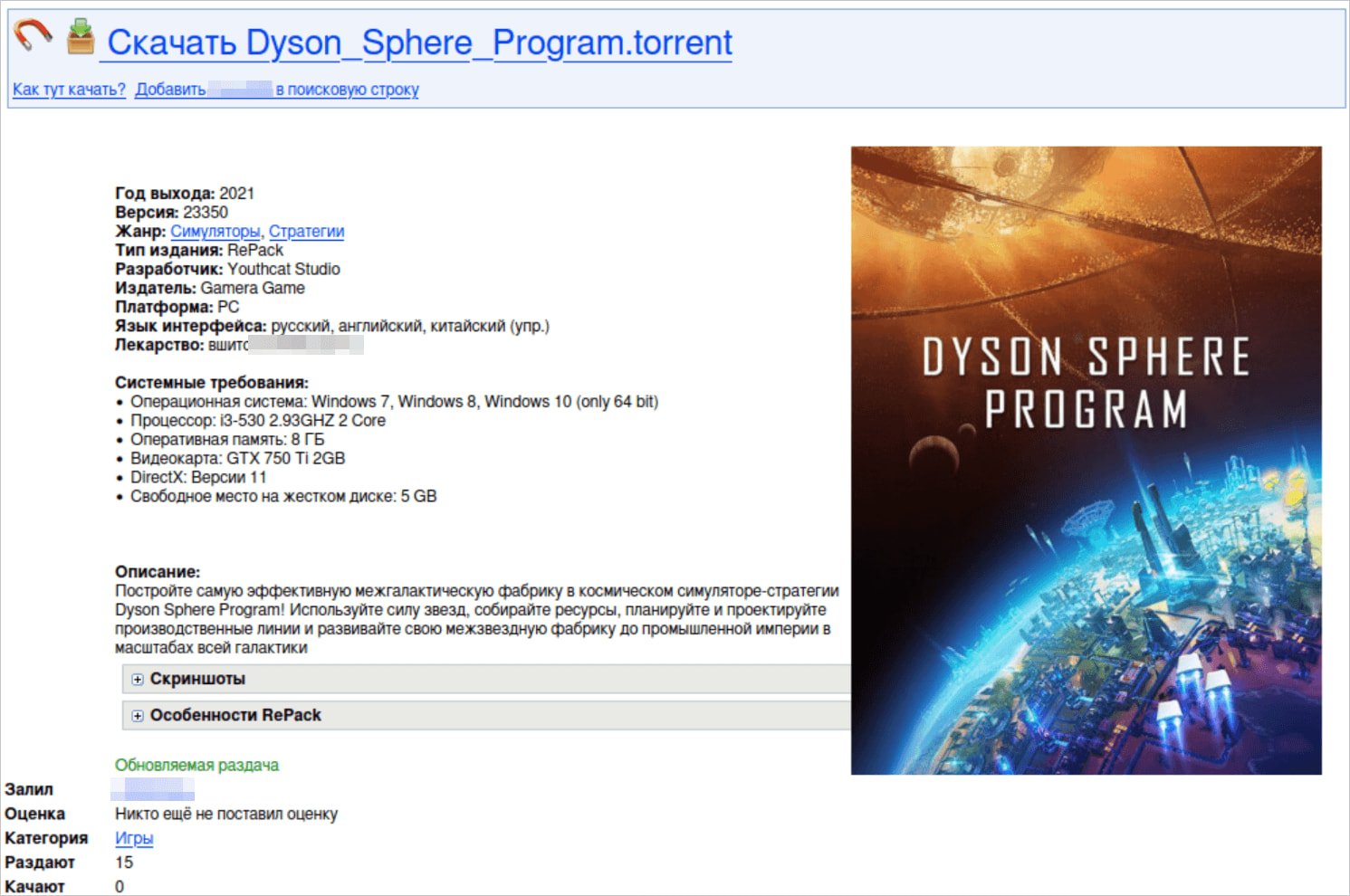
A big-scale malware marketing campaign dubbed “StaryDobry” has been focusing on avid gamers worldwide with trojanized variations of cracked video games reminiscent of Garry’s Mod, BeamNG.drive, and Dyson Sphere Program.
These titles are top-rated video games with a whole lot of hundreds of ‘overwhelmingly optimistic’ critiques on Steam, making them good targets for malicious exercise.
It is price noting {that a} laced Beamng mod was reportedly used because the preliminary entry vector for a hack at Disney in June 2024.
In line with Kaspersky, the StaryDobry marketing campaign began in late December 2024 and ended on January 27, 2025. It largely impacted customers from Germany, Russia, Brazil, Belarus, and Kazakhstan.
The risk actors uploaded contaminated recreation installers onto torrent websites in September 2024, months upfront, and triggered the payloads throughout the video games through the holidays, making detection much less probably.
.jpg)
Supply: Kaspersky
StaryDobry an infection chain
The StaryDobry marketing campaign used a multi-stage an infection chain culminating with an XMRig cryptominer an infection.
Customers downloaded the trojanized recreation installers from torrent websites, which appeared regular, together with the precise recreation they have been promised, plus malicious code.
Supply: Kaspersky
In the course of the recreation’s set up, the malware dropper (unrar.dll) is unpacked and launched within the background, and it checks if it is working on a digital machine, sandbox, or debugger earlier than continuing.
The malware demonstrates extremely evasive habits, terminating instantly if it detects any safety instruments, presumably to keep away from harming the torrent’s fame.
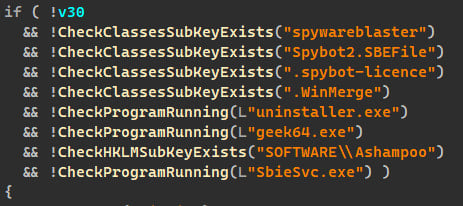
Supply: Kaspersky
Subsequent, the malware registers itself utilizing ‘regsvr32.exe’ for persistence and collects detailed system info, together with OS model, nation, CPU, RAM, and GPU particulars, and sends it to the command and management (C2) server at pinokino[.]enjoyable.
Ultimately, the dropper decrypts and installs the malware loader (MTX64.exe) in a system listing.
The loader poses as a Home windows system file, engages in useful resource spoofing to seem legit, and creates a scheduled activity to persist between reboots. If the host machine has a minimum of eight CPU cores, it downloads and runs an XMRig miner.
The XMRig miner utilized in StaryDobry is a modified model of the Monero miner that constructs its configuration internally earlier than execution and doesn’t entry arguments.
The miner maintains a separate thread always, monitoring for safety instruments working on the contaminated machine, and if any course of monitoring instruments are detected, it shuts itself down.
The XMRig utilized in these assaults connects to non-public mining servers as a substitute of public swimming pools, making the proceeds more durable to hint.
Kaspersky has not been in a position to attribute the assaults to any identified risk teams however notes that it probably originates from a Russian-speaking actor.
“StaryDobry tends to be a one-shot marketing campaign. To ship the miner implant, the actors applied a complicated execution chain that exploited customers searching for free video games,” concluded Kaspersky.
“This strategy helped the risk actors take advantage of out of the miner implant by focusing on highly effective gaming machines able to sustaining mining exercise.”

