Final up to date: December 17, 2025
Initially printed: December 18, 2017
Amazon Information Firehose helps Splunk Enterprise and Splunk Cloud as a supply vacation spot. This native integration between Splunk Enterprise, Splunk Cloud, and Amazon Information Firehose is designed to make AWS information ingestion setup seamless, whereas providing a safe and fault-tolerant supply mechanism. We need to allow prospects to observe and analyze machine information from any supply and use it to ship operational intelligence and optimize IT, safety, and enterprise efficiency.
With Amazon Information Firehose, prospects can use a completely managed, dependable, and scalable information streaming resolution to Splunk. On this publish, we inform you a bit extra in regards to the Amazon Information Firehose and Splunk integration. We additionally present you the way to ingest giant quantities of information into Splunk utilizing Amazon Information Firehose.
Push vs. Pull information ingestion
Presently, prospects use a mixture of two ingestion patterns, based on information supply and quantity, along with current firm infrastructure and experience:
- Pull-based strategy: Utilizing devoted pollers operating the favored Splunk Add-on for AWS to drag information from varied AWS companies akin to Amazon CloudWatch or Amazon S3.
- Push-based strategy: Streaming information immediately from AWS to Splunk HTTP Occasion Collector (HEC) by utilizing Amazon Information Firehose. Examples of relevant information sources embody CloudWatch Logs and Amazon Kinesis Information Streams.
The pull-based strategy affords information supply ensures akin to retries and checkpointing out of the field. Nevertheless, it requires extra ops to handle and orchestrate the devoted pollers, that are generally operating on Amazon EC2 situations. With this setup, you pay for the infrastructure even when it’s idle.
However, the push-based strategy affords a low-latency scalable information pipeline made up of serverless assets like Amazon Information Firehose sending on to Splunk indexers (by utilizing Splunk HEC). This strategy interprets into decrease operational complexity and price. Nevertheless, should you want assured information supply then you must design your resolution to deal with points akin to a Splunk connection failure or Lambda execution failure. To take action, you would possibly use, for instance, AWS Lambda Lifeless Letter Queues.
How about getting the very best of each worlds?
Let’s go over the brand new integration’s end-to-end resolution and study how Amazon Information Firehose and Splunk collectively develop the push-based strategy right into a native AWS resolution for relevant information sources.
By utilizing a managed service like Amazon Information Firehose for information ingestion into Splunk, we offer out-of-the-box reliability and scalability. One of many ache factors of the outdated strategy was the overhead of managing the info assortment nodes (Splunk heavy forwarders). With the brand new Amazon Information Firehose to Splunk integration, there are not any forwarders to handle or arrange. Information producers (1) are configured via the AWS Administration Console to drop information into Amazon Information Firehose.
It’s also possible to create your individual information producers. For instance, you may drop information right into a Firehose supply stream by utilizing Amazon Kinesis Agent, or by utilizing the Firehose API (PutRecord(), PutRecordBatch()), or by writing to a Kinesis Information Stream configured to be the info supply of a Firehose supply stream. For extra particulars, seek advice from Sending Information to an Amazon Information Firehose Supply Stream.
You would possibly want to remodel the info earlier than it goes into Splunk for evaluation. For instance, you would possibly need to enrich it or filter or anonymize delicate information. You are able to do so utilizing AWS Lambda and enabling information transformation in Amazon Information Firehose. On this situation, Amazon Information Firehose is used to decompress the Amazon CloudWatch logs by enabling the function.
Programs fail on a regular basis. Let’s see how this integration handles outdoors failures to ensure information sturdiness. In instances when Amazon Information Firehose can’t ship information to the Splunk Cluster, information is mechanically backed as much as an S3 bucket. You may configure this function whereas creating the Firehose supply stream (2). You may select to again up all information or solely the info that’s failed throughout supply to Splunk.
Along with utilizing S3 for information backup, this Firehose integration with Splunk helps Splunk Indexer Acknowledgments to ensure occasion supply. This function is configured on Splunk’s HTTP Occasion Collector (HEC) (3). It ensures that HEC returns an acknowledgment to Amazon Information Firehose solely after information has been listed and is offered within the Splunk cluster (4).
Now let’s take a look at a hands-on train that exhibits the way to ahead VPC circulation logs to Splunk.
How-to information
To course of VPC circulation logs, we implement the next structure.
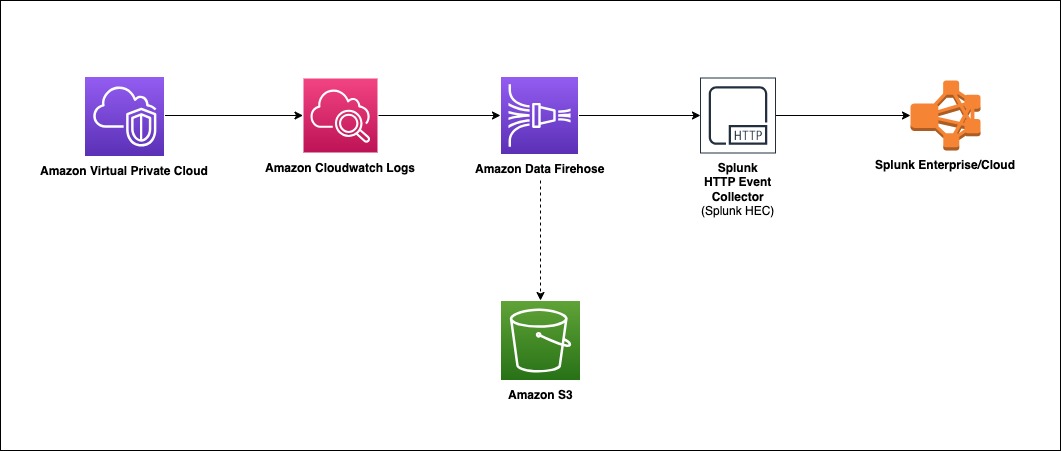
Amazon Digital Personal Cloud (Amazon VPC) delivers circulation log recordsdata into an Amazon CloudWatch Logs group. Utilizing a CloudWatch Logs subscription filter, we arrange real-time supply of CloudWatch Logs to an Amazon Information Firehose stream.
Information coming from CloudWatch Logs is compressed with gzip compression. To work with this compression, we’ll allow decompression for the Firehose stream. Firehose then delivers the uncooked logs to the Splunk Http Occasion Collector (HEC).
If supply to the Splunk HEC fails, Firehose deposits the logs into an Amazon S3 bucket. You may then ingest the occasions from S3 utilizing an alternate mechanism akin to a Lambda operate.
When information reaches Splunk (Enterprise or Cloud), Splunk parsing configurations (packaged within the Splunk Add-on for Amazon Information Firehose) extract and parse all fields. They make information prepared for querying and visualization utilizing Splunk Enterprise and Splunk Cloud.
Walkthrough
Set up the Splunk Add-on for Amazon Information Firehose
The Splunk Add-on for Amazon Information Firehose permits Splunk (be it Splunk Enterprise, Splunk App for AWS, or Splunk Enterprise Safety) to make use of information ingested from Amazon Information Firehose. Set up the Add-on on all of the indexers with an HTTP Occasion Collector (HEC). The Add-on is offered for obtain from Splunkbase. For troubleshooting help, please seek advice from: AWS Information Firehose troubleshooting documentation & Splunk’s official troubleshooting information
HTTP Occasion Collector (HEC)
Earlier than you need to use Amazon Information Firehose to ship information to Splunk, arrange the Splunk HEC to obtain the info. From Splunk net, go to the Setting menu, select Information Inputs, and select HTTP Occasion Collector. Select World Settings, guarantee All tokens is enabled, after which select Save. Then select New Token to create a brand new HEC endpoint and token. Whenever you create a brand new token, be sure that Allow indexer acknowledgment is checked.
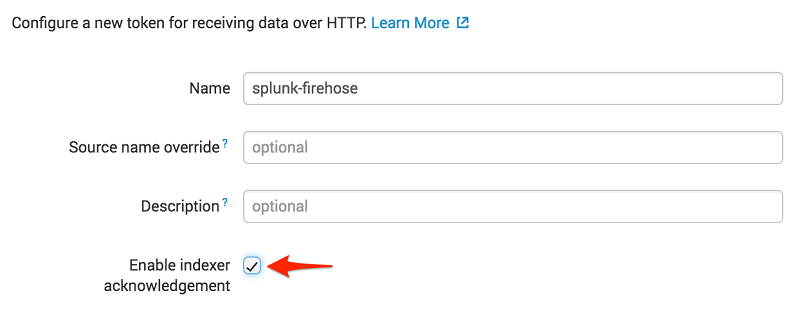
When prompted to pick out a supply sort, choose aws:cloudwatchlogs:vpcflow

Create an S3 backsplash bucket
To offer for conditions during which Amazon Information Firehose can’t ship information to the Splunk Cluster, we use an S3 bucket to again up the info. You may configure this function to again up all information or solely the info that’s failed throughout supply to Splunk.
Be aware: Bucket names are distinctive.
Create an Amazon Information Firehose supply stream
On the AWS console, open the Amazon Information Firehose console, and select Create Firehose Stream.
Choose DirectPUT because the supply and Splunk because the vacation spot.

If you’re utilizing Firehose to ship CloudWatch Logs and need to ship decompressed information to your Firehose stream vacation spot, use Firehose Information Format Conversion (Parquet, ORC) or Dynamic partitioning. You need to allow decompression on your Firehose stream, take a look at Ship decompressed Amazon CloudWatch Logs to Amazon S3 and Splunk utilizing Amazon Information Firehose

Enter your Splunk HTTP Occasion Collector (HEC) info in vacation spot settings

Be aware: Amazon Information Firehose requires the Splunk HTTP Occasion Collector (HEC) endpoint to be terminated with a legitimate CA-signed certificates matching the DNS hostname used to hook up with your HEC endpoint. You obtain supply errors in case you are utilizing a self-signed certificates.
On this instance, we solely again up logs that fail throughout supply.

To observe your Firehose supply stream, allow error logging. Doing this implies you could monitor document supply errors. Create an IAM position for the Firehose stream by selecting Create new, or Select current IAM position.

You now get an opportunity to evaluation and alter the Firehose stream settings. If you find yourself glad, select Create Firehose Stream.
Create a VPC Move Log
To ship occasions from Amazon VPC, you might want to arrange a VPC circulation log. If you have already got a VPC circulation log you need to use, you may skip to the “Publish CloudWatch to Amazon Information Firehose” part.
On the AWS console, open the Amazon VPC service. Then select VPC, and select the VPC you need to ship circulation logs from. Select Move Logs, after which select Create Move Log. Should you don’t have an IAM position that enables your VPC to publish logs to CloudWatch, select Create and use a brand new service position.

As soon as lively, your VPC circulation log ought to seem like the next.

Publish CloudWatch to Amazon Information Firehose
Whenever you generate site visitors to or out of your VPC, the log group is created in Amazon CloudWatch. We create an IAM position to permit Cloudwatch to publish logs to the Amazon Information Firehose Stream.
To permit CloudWatch to publish to your Firehose stream, you might want to give it permissions.
Right here is the content material for TrustPolicyForCWLToFireHose.json.
Connect the coverage to the newly created position.
Right here is the content material for PermissionPolicyForCWLToFireHose.json.
The brand new log group has no subscription filter, so arrange a subscription filter. Setting this up establishes a real-time information feed from the log group to your Firehose supply stream. Choose the VPC circulation log and select Actions. Then select Subscription filters adopted by Create Amazon Information Firehose subscription filter.


Whenever you run the AWS CLI command previous, you don’t get any acknowledgment. To validate that your CloudWatch Log Group is subscribed to your Firehose stream, test the CloudWatch console.
As quickly because the subscription filter is created, the real-time log information from the log group goes into your Firehose supply stream. Your stream then delivers it to your Splunk Enterprise or Splunk Cloud surroundings for querying and visualization. The screenshot following is from Splunk Enterprise.
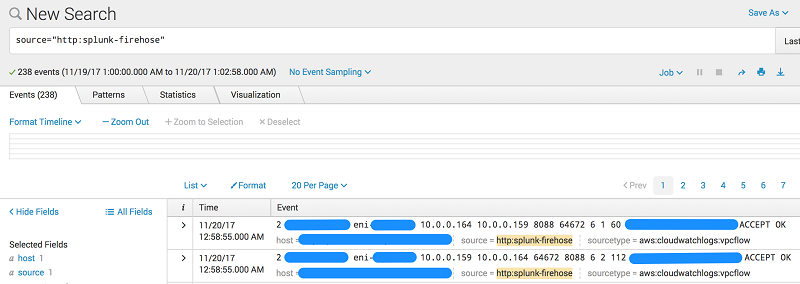
As well as, you may monitor and examine metrics related together with your supply stream utilizing the AWS console.

Conclusion
Though our walkthrough makes use of VPC Move Logs, the sample can be utilized in lots of different eventualities. These embody ingesting information from AWS IoT, different CloudWatch logs and occasions, Kinesis Streams or different information sources utilizing the Kinesis Agent or Kinesis Producer Library. It’s possible you’ll use a Lambda blueprint or disable document transformation completely relying in your use case. For an extra use case utilizing Amazon Information Firehose, take a look at That is My Structure Video, which discusses the way to securely centralize cross-account information analytics utilizing Kinesis and Splunk.
Should you discovered this publish helpful, make sure to take a look at Integrating Splunk with Amazon Kinesis Streams.
In regards to the Authors

