Scammers are impersonating the BianLian ransomware gang in faux ransom notes despatched to US corporations through snail mail via the US Postal Service.
The faux ransom notes had been first reported by Guidepoint Safety in the present day, with BleepingComputer later being despatched a scan of the be aware from a CEO who obtained the identical letter.
The envelopes for these ransom notes declare to be from the “BIANLIAN Group” and have a return deal with situated in an workplace constructing in Boston, Massachusets:
BIANLIAN GROUP
24 FEDERAL ST, SUITE 100
BOSTON, MA 02110
Within the letter shared with BleepingComputer, the envelope exhibits it was mailed on February twenty fifth, 2025. This mailing date is similar because the one seen by Arctic Wolf, who additionally reported on the rip-off in the present day.
The letters are being mailed to the CEO of the businesses at their company mailing deal with and present that they had been processed via a postal facility in Boston, with the envelope marked, “Time Delicate Learn Instantly.”
Supply: BleepingComputer
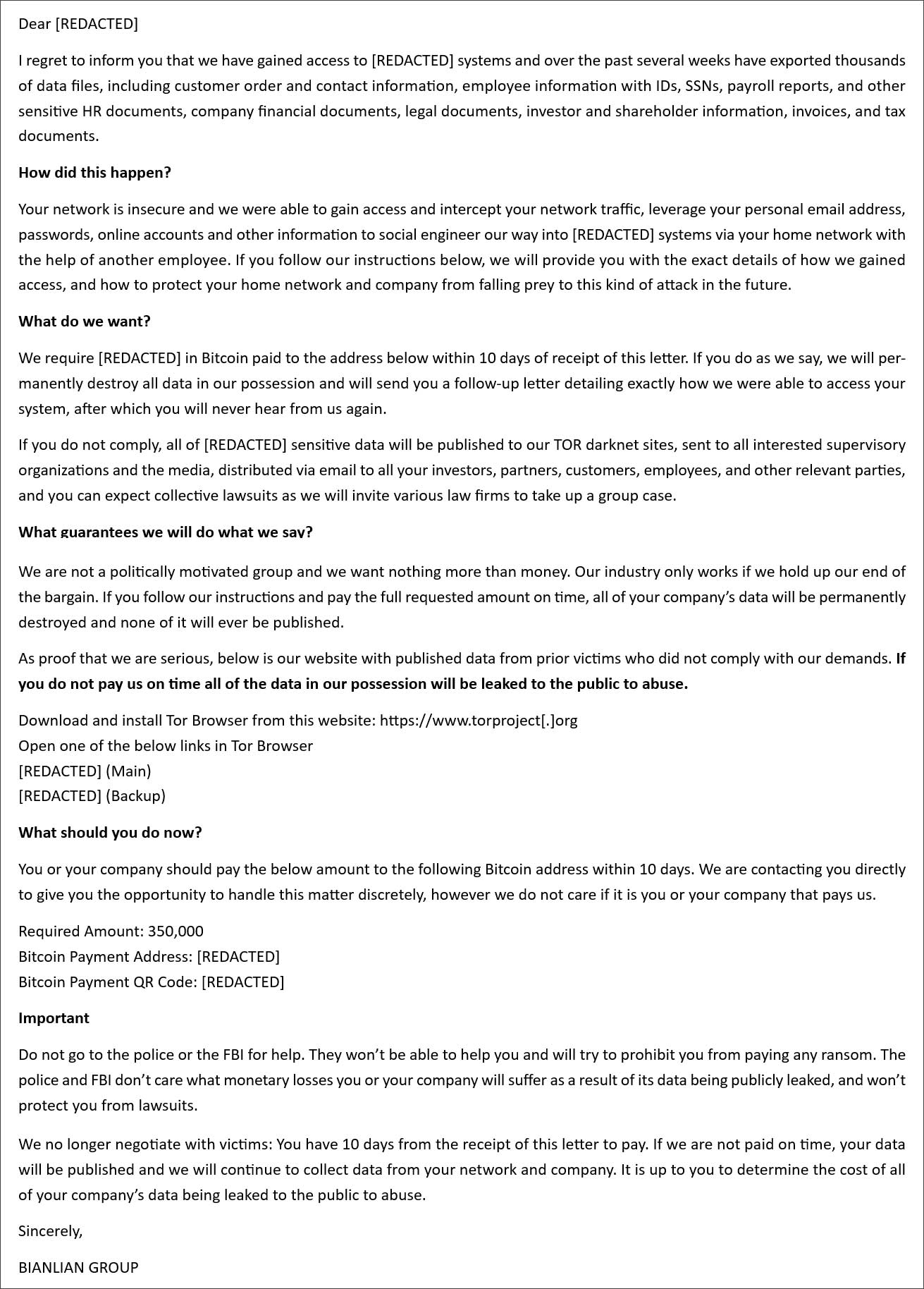
The envelopes comprise a ransom be aware addressed to the corporate’s CEO or one other govt, claiming to be from the BianLian ransomware operation. In response to notes reviewed by BleepingComputer, they’re tailor-made to the corporate’s business, with various kinds of allegedly stolen information comparable to the corporate’s actions.
For instance, faux BianLian ransom notes despatched to healthcare corporations declare that affected person and worker data was stolen, whereas these focusing on product-based companies allege the publicity of buyer orders and worker information.
“I remorse to tell you that we now have gained entry to [REDACTED] methods and over the previous a number of weeks have exported 1000’s of knowledge recordsdata, together with buyer order and get in touch with data, worker data with IDs, SSNs, payroll stories, and different delicate HR paperwork, firm monetary paperwork, authorized paperwork, investor and shareholder data, invoices, and tax paperwork,” reads a faux BianLian ransom be aware.
Supply: GuidePoint Safety
The mailed ransom notes are very totally different from BianLian’s, however the scammers try and make them look convincing by together with the actual Tor information leak websites for the ransomware operation within the notes.
Nevertheless, not like typical ransomware calls for, these faux notes state that BianLian is now not negotiating with victims. As a substitute, the sufferer has 10 days to make a Bitcoin cost to stop information from being leaked.
Every ransom be aware features a ransom demand ranging between $250,000 and $500,000, a freshly generated Bitcoin deal with to ship cost, and a QR code for the Bitcoin deal with.
Arctic Wolf stated that each one healthcare organizations had their ransom demand set to $350,000, which is similar because the one shared by a healthcare firm with BleepingComputer, as proven beneath.
Supply: BleepingComputer
Moreover, Arctic Wolf states that two ransom notes the researchers noticed included authentic compromised passwords so as to add legitimacy to the demand.
“In at the very least two letters, the menace actor included a compromised password throughout the How did this occur? part, nearly definitely in an try so as to add legitimacy to their declare.” defined Arctic Wolf.
The consensus within the stories is that these ransom notes are faux and are solely designed to scare executives into paying a ransom, as there aren’t any indicators of an precise breach.
“Whereas GRIT can not verify the identification of the letter’s authors presently, we assess with a excessive stage of confidence that the extortion calls for contained inside are illegitimate and don’t originate from the BianLian ransomware group,” explains GuidePoint Safety researcher Grayson North.
Nevertheless, this doesn’t imply the emails must be ignored. As a result of widespread mailing of those notes, all IT and safety admins ought to notify executives in regards to the rip-off in order that they’re conscious and don’t waste time and sources worrying about them.
These faux ransom notes are an evolution of the electronic mail extortion scams which have turn into so widespread since 2018. Nevertheless, as an alternative of focusing on private emails, they’re now focusing on the CEOs of companies.
BleepingComputer contacted the BianLian ransomware operation to see in the event that they had been concerned with these mailings, however a reply was not instantly out there.

