An ongoing phishing marketing campaign impersonates common manufacturers, akin to Unilever, Disney, MasterCard, LVMH, and Uber, in Calendly-themed lures to steal Google Workspace and Fb enterprise account credentials.
Though menace actors focusing on enterprise advert supervisor accounts is not new, the marketing campaign found by Push Safety is very focused, with professionally crafted lures that create situations for prime success charges.
Entry to advertising accounts provides menace actors a springboard to launch malvertising campaigns for AiTM phishing, malware distribution, and ClickFix assaults.
Additionally, advert platforms enable geo-targeting, area filtering, and device-specific focusing on, enabling “watering-hole” styled assaults.
Finally, compromised advertising accounts will be resold to cybercriminals, so direct monetization is all the time a legitimate possibility.
Google Workspace accounts additionally usually lengthen to enterprise environments and enterprise information, particularly by way of SSO and permissive IdP configurations.
Calendly phishing
Calendly is a legit on-line scheduling platform the place the organizer of a gathering sends a hyperlink to the opposite celebration, permitting recipients to choose an out there time slot.
The service has been abused prior to now for phishing assaults, however using well-known manufacturers to take advantage of belief and familiarity is what elevated this marketing campaign.
The assault begins with the menace actor impersonating a recruiter for a well known model after which sending a faux assembly invitation to the goal. The recruiters are legit workers who’re additionally impersonated on the phishing touchdown pages.
The phishing emails are believed to have been crafted utilizing AI instruments and to impersonate over 75 manufacturers, together with LVMH, Lego, Mastercard, and Uber.
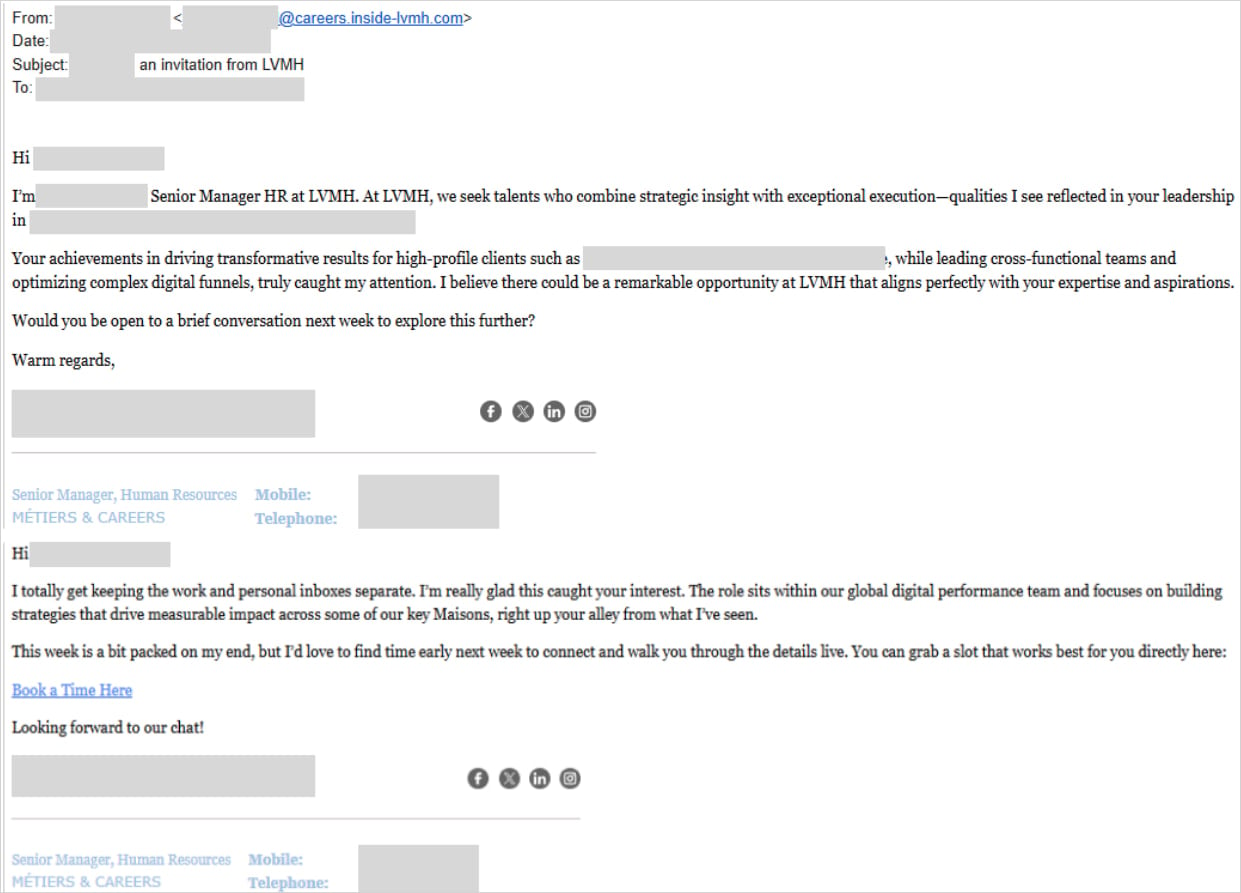
Supply: Push Safety
As soon as the sufferer clicks the hyperlink, they’re taken to a faux Calendly touchdown web page that presents a CAPTCHA, adopted by an AiTM phishing web page that makes an attempt to steal guests’ Google Workspace login periods.
Push Safety advised BleepingComputer that they confirmed the marketing campaign targets Google MCC advert supervisor accounts after talking to one of many organizations impacted by the phishing assault.
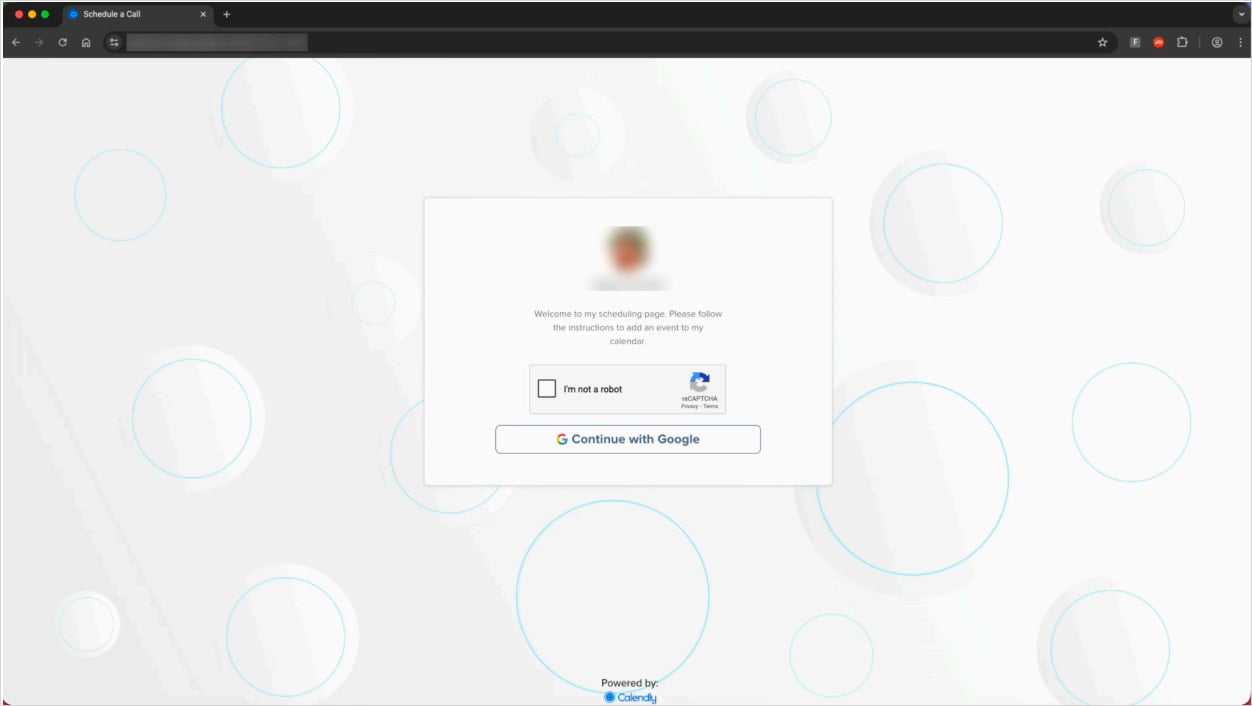
Supply: Push Safety
Push Safety discovered 31 distinctive URLs supporting this marketing campaign, however upon additional investigation, the researchers uncovered extra variants.
One variant impersonated Unilever, Disney, Lego, and Artisan to focus on Fb Enterprise credentials.
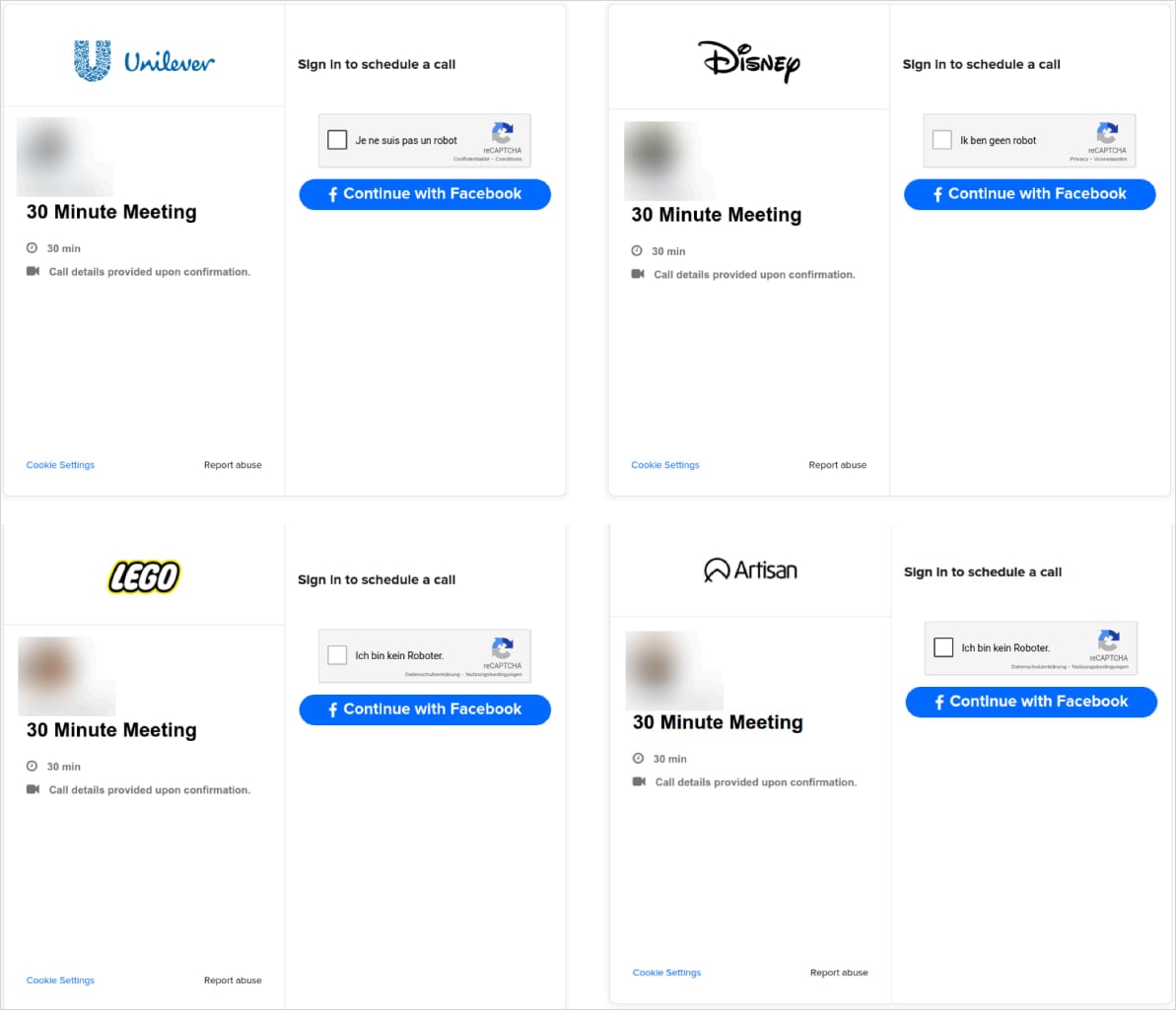
Supply: Push Safety
A newer variant targets each Google and Fb credentials utilizing Browser-in-the-Browser (BitB) assaults that show faux pop-up home windows that includes legit URLs to steal account credentials.
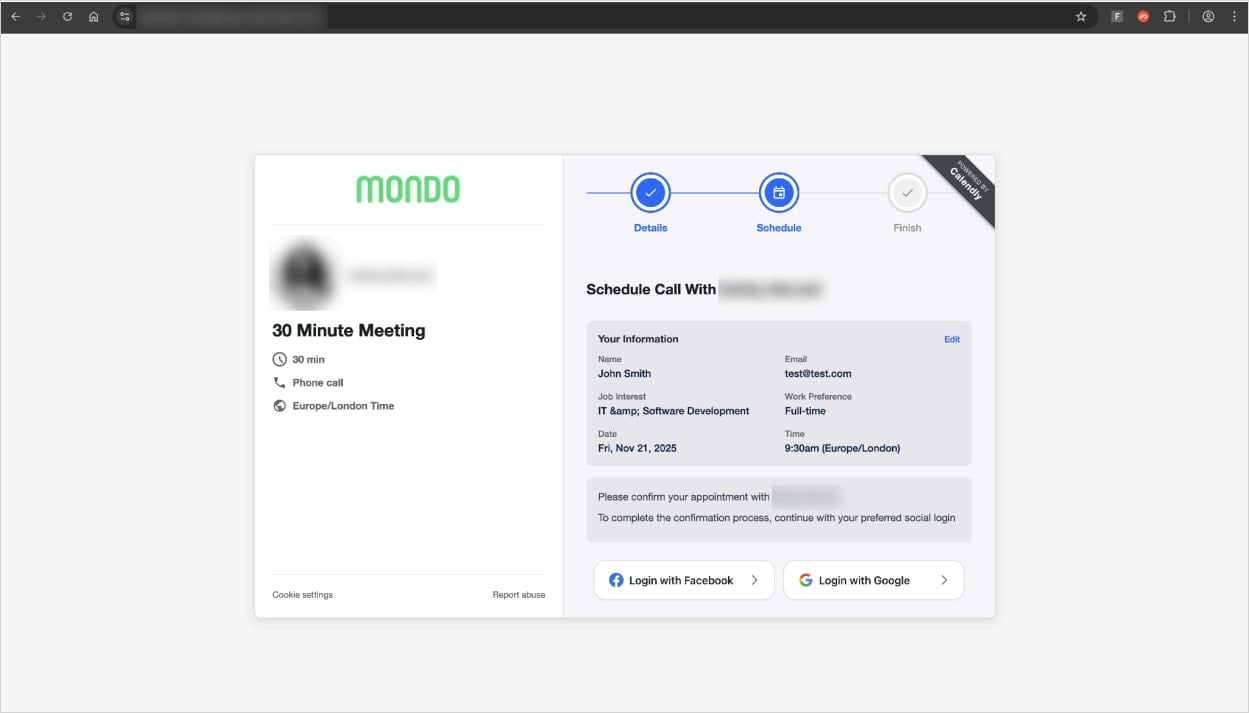
Supply: Push Safety
The phishing pages function anti-analysis mechanisms, akin to blocking VPN and proxy site visitors and stopping the customer from opening developer instruments whereas on the web page.
Concurrently, Push Safety noticed one other malvertising marketing campaign focusing on Google Adverts Supervisor accounts, through which customers who looked for “Google Adverts” on Google Search ended up clicking a malicious sponsored advert.
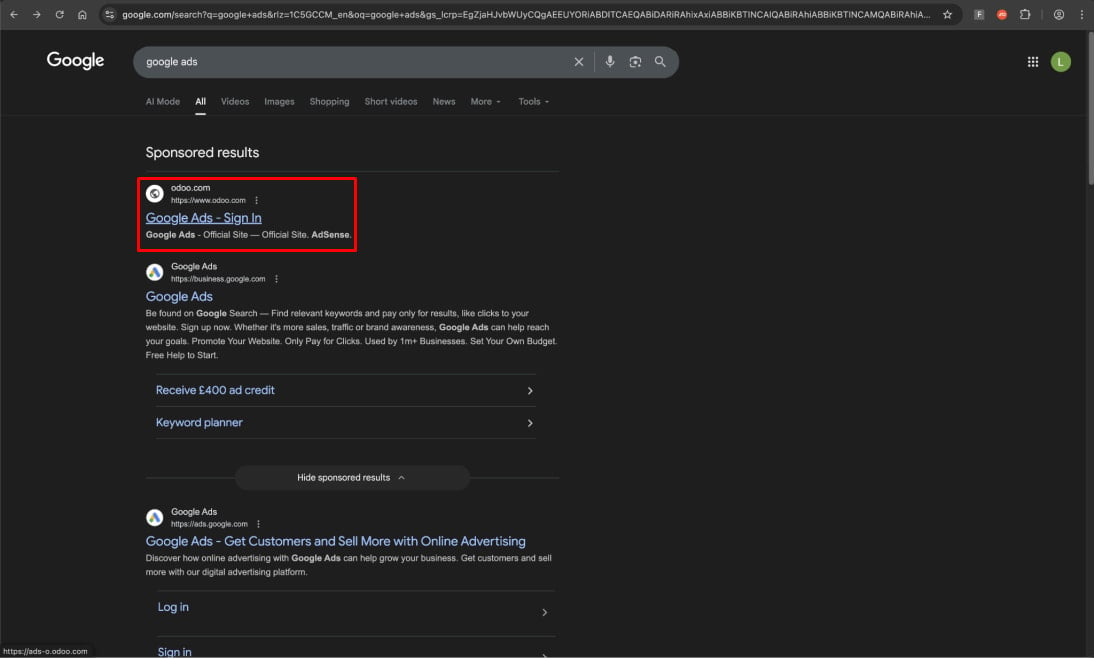
Supply: Push Safety
These outcomes direct victims to a Google Adverts-themed phishing web page, which then redirects them to an AiTM phishing web page impersonating Google’s login display screen.
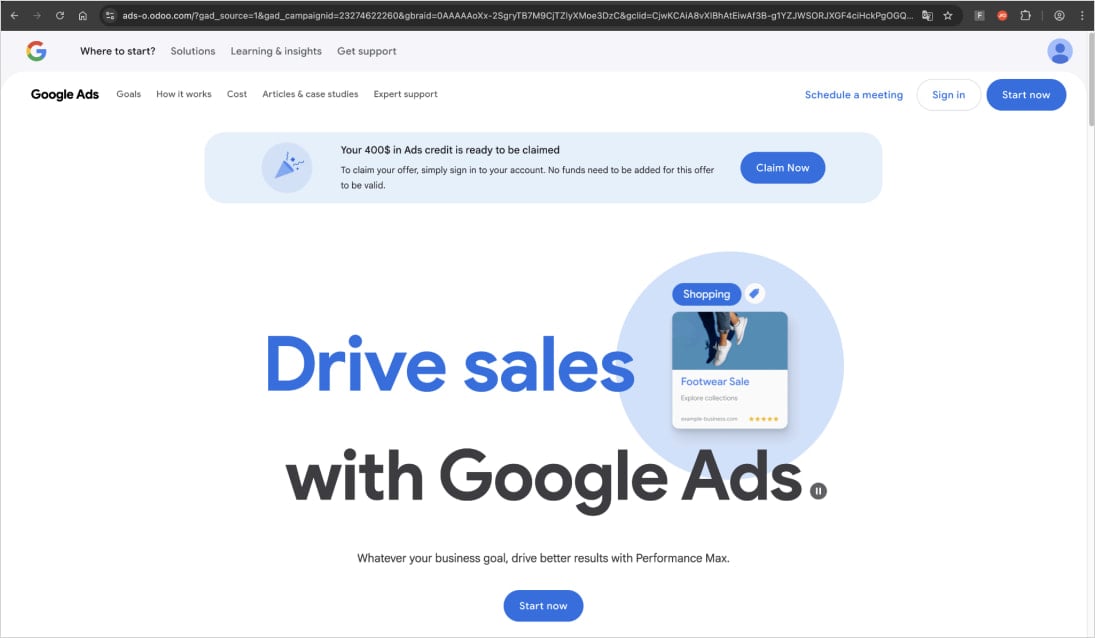
Supply: Push Safety
Push Safety found a number of cases of this marketing campaign, hosted on Odoo, and generally routed by way of Kartra.
Comparable campaigns focusing on advert supervisor accounts have been documented earlier than, however they continue to be profitable for menace actors.
As AiTM methods enable attackers to bypass two-factor authentication (2FA) protections, it is suggested that house owners of useful accounts use {hardware} safety keys, confirm URLs earlier than coming into their credentials, and drag login pop-ups to the sting of the browser window to confirm their legitimacy.
Damaged IAM is not simply an IT drawback – the affect ripples throughout your entire enterprise.
This sensible information covers why conventional IAM practices fail to maintain up with trendy calls for, examples of what “good” IAM seems to be like, and a easy guidelines for constructing a scalable technique.


