A hacking group dubbed ‘Elusive Comet’ targets cryptocurrency customers in social engineering assaults that exploit Zoom’s distant management characteristic to trick customers into granting them entry to their machines.
Zoom’s distant management characteristic permits assembly members to take management of one other participant’s pc.
In accordance with cybersecurity agency Path of Bits, which encountered this social engineering marketing campaign, the perpetrators mirror strategies utilized by the Lazarus hacking group within the large $1.5 billion Bybit crypto heist.
“The ELUSIVE COMET methodology mirrors the strategies behind the current $1.5 billion Bybit hack in February, the place attackers manipulated legit workflows slightly than exploiting code vulnerabilities,” explains the Path of Bits report.
Zoom-based interview scheme
Path of Bits realized of this new marketing campaign after the risk actors tried to conduct the social engineering assault on its CEO through X direct messages.
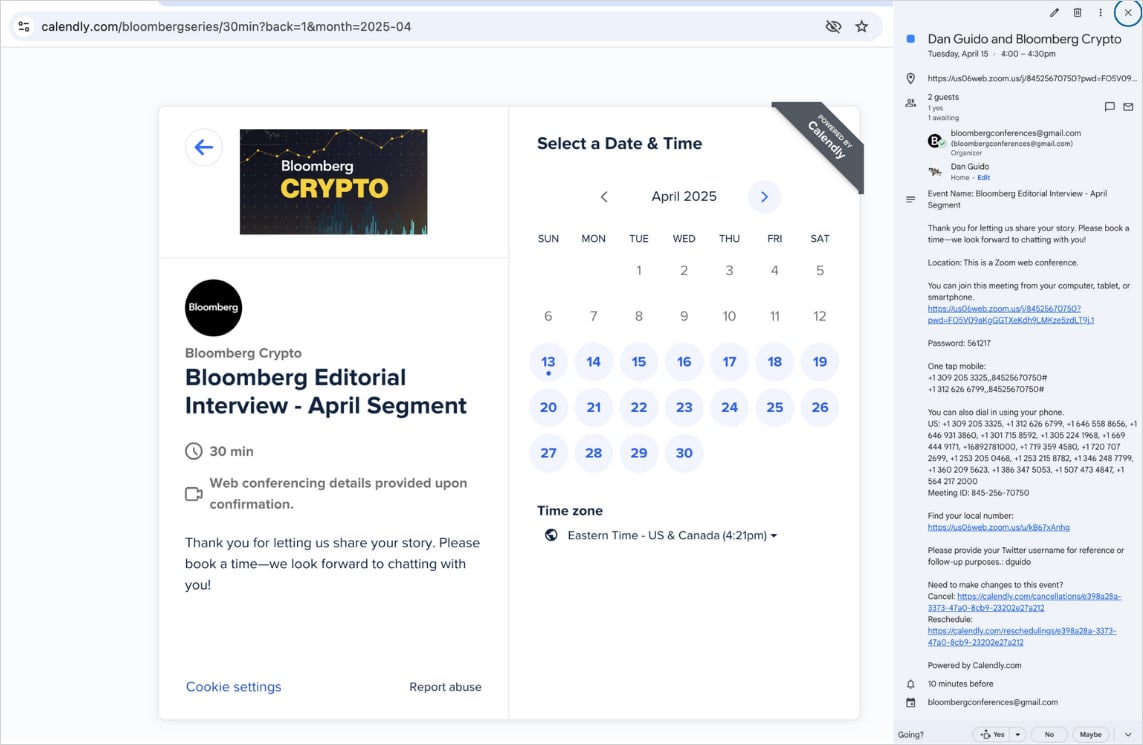
The assault begins with an invite to a “Bloomberg Crypto” interview through Zoom, despatched to high-value targets through sock-puppet accounts on X, or through e-mail (bloombergconferences[@]gmail.com).
The pretend accounts impersonate crypto-focused journalists or Bloomberg retailers and attain out to the targets through direct messages on social media platforms.

Supply: Path of Bits
The invites are despatched via Calendly hyperlinks to schedule a Zoom assembly. Since each Calendly and Zoom invitations/hyperlinks are genuine, they work as anticipated and decrease the goal’s suspicions.
Supply: Path of Bits
Through the Zoom name, the attacker initiates a screen-sharing session and sends a distant management request to the goal.
The trick employed on this stage is that the attackers rename their Zoom show identify to “Zoom,” so the immediate the sufferer sees reads “Zoom is requesting distant management of your display,” making it seem as a legit request from the app.
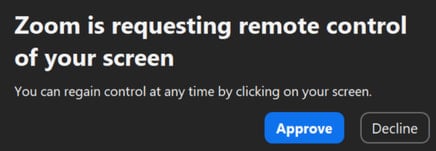
Supply: Path of Bits
Nevertheless, approving the request provides the attackers full distant enter management over the sufferer’s system, permitting them to steal delicate information, set up malware, entry recordsdata, or provoke crypto transactions.
The attacker might act shortly to ascertain persistent entry by implanting a stealthy backdoor for later exploitation and disconnect, leaving victims with little likelihood to comprehend the compromise.
“What makes this assault notably harmful is the permission dialog’s similarity to different innocent Zoom notifications,” says Path of Bits.
“Customers habituated to clicking “Approve” on Zoom prompts might grant full management of their pc with out realizing the implications.”
To defend towards this risk, Path of Bits suggests the implementation of system-wide Privateness Preferences Coverage Management (PPPC) profiles that stop accessibility entry, which is feasible by utilizing this assortment of instruments.
The agency recommends eradicating Zoom completely from all techniques for security-critical environments and organizations that deal with invaluable digital belongings.
“For organizations dealing with notably delicate information or cryptocurrency transactions, the chance discount from eliminating the Zoom shopper completely typically outweighs the minor inconvenience of utilizing browser-based options,” explains Path of Bits.

