A brand new hacking group has leaked the configuration information, IP addresses, and VPN credentials for over 15,000 FortiGate units at no cost on the darkish net, exposing a substantial amount of delicate technical info to different cybercriminals.
The info was leaked by the “Belsen Group,” a brand new hacking group first showing on social media and cybercrime boards this month. To advertise themselves, the Belsen Group has created a Tor web site the place they launched the FortiGate information dump at no cost for use by different risk actors.
“In the beginning of the 12 months, and as a optimistic begin for us, and with a view to solidify the title of our group in your reminiscence, we’re proud to announce our first official operation: Shall be printed of delicate information from over 15,000 targets worldwide (each governmental and personal sectors) which were hacked and their information extracted,” reads a hacking discussion board publish.
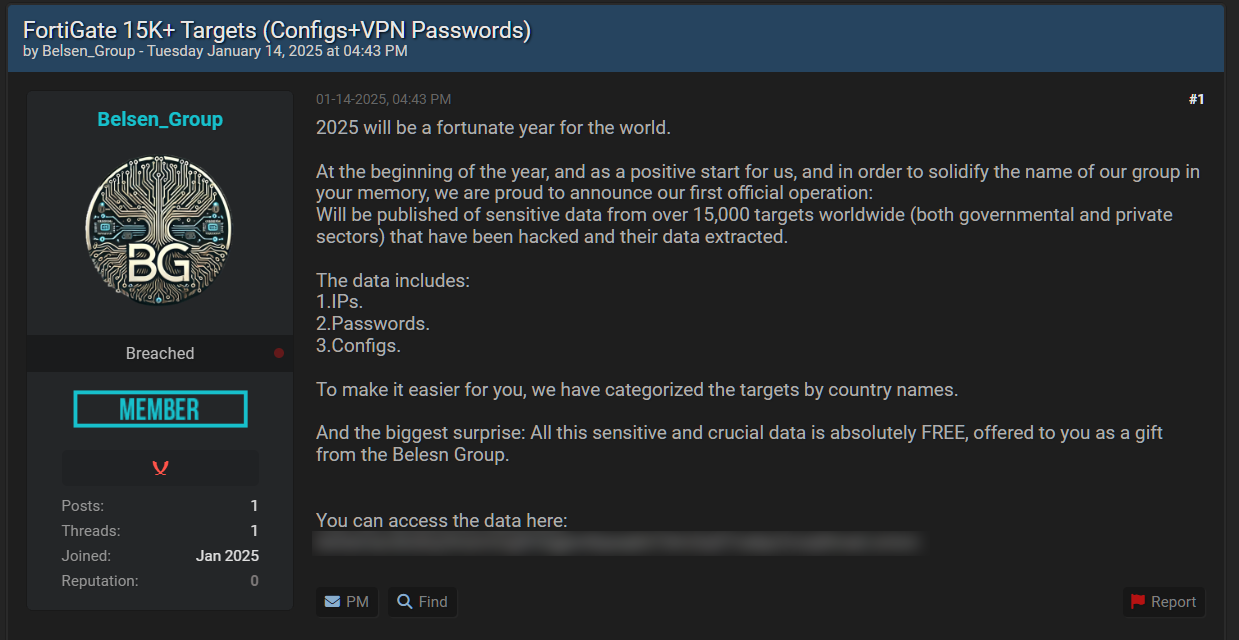
Supply: BleepingComputer
The FortiGate leak consists of a 1.6 GB archive containing folders ordered by nation. Every folder incorporates additional subfolders for every FortiGate’s IP deal with in that nation.
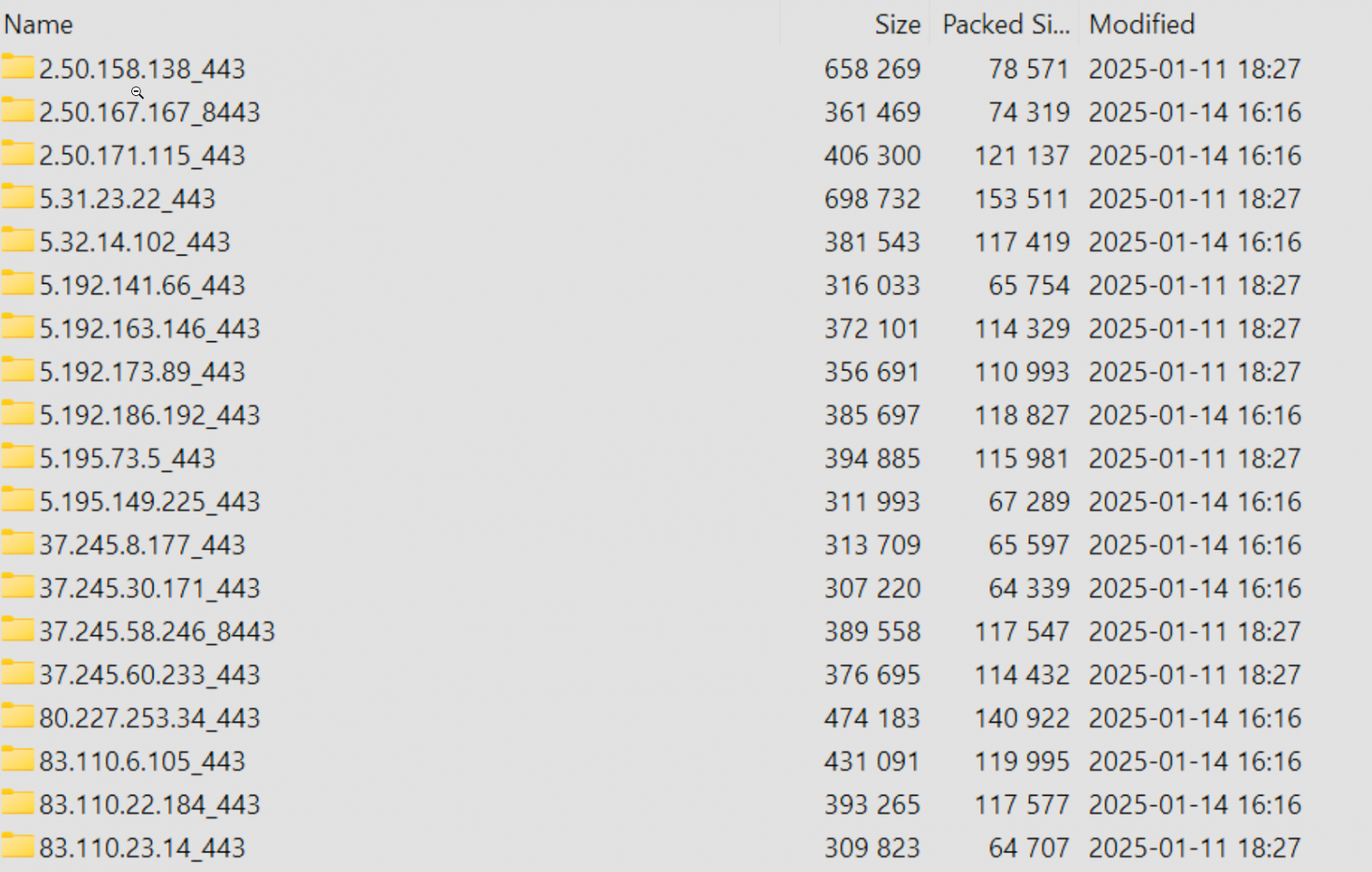
Supply: Beaumont
In line with cybersecurity knowledgeable Kevin Beaumont, every IP deal with has a configuration.conf (Fortigate config dump) and a vpn-passwords.txt file, with a few of the passwords in plain textual content. The configs additionally comprise delicate info, comparable to personal keys and firewall guidelines.
In a weblog publish concerning the FortiGate leak, Beaumont says that the leak is believed to be linked to a 2022 zero-day tracked as CVE-2022–40684 that was exploited in assaults earlier than a repair was launched.
“I’ve completed incident response on one gadget at a sufferer org, and exploitation was certainly through CVE-2022–40684 primarily based on artefacts on the gadget. I’ve additionally been in a position to confirm the usernames and password seen within the dump matches the main points on the gadget,” explains Beaumont.
“The info seems to have been assembled in October 2022, as a zero day vuln. For some purpose, the information dump of config has been launched at present, simply over 2 years later.”
In 2022, Fortinet warned that risk actors have been exploiting a zero-day tracked as CVE-2022–40684 to obtain config information from focused FortiGate units after which add a malicious super_admin account referred to as ‘fortigate-tech-support’.
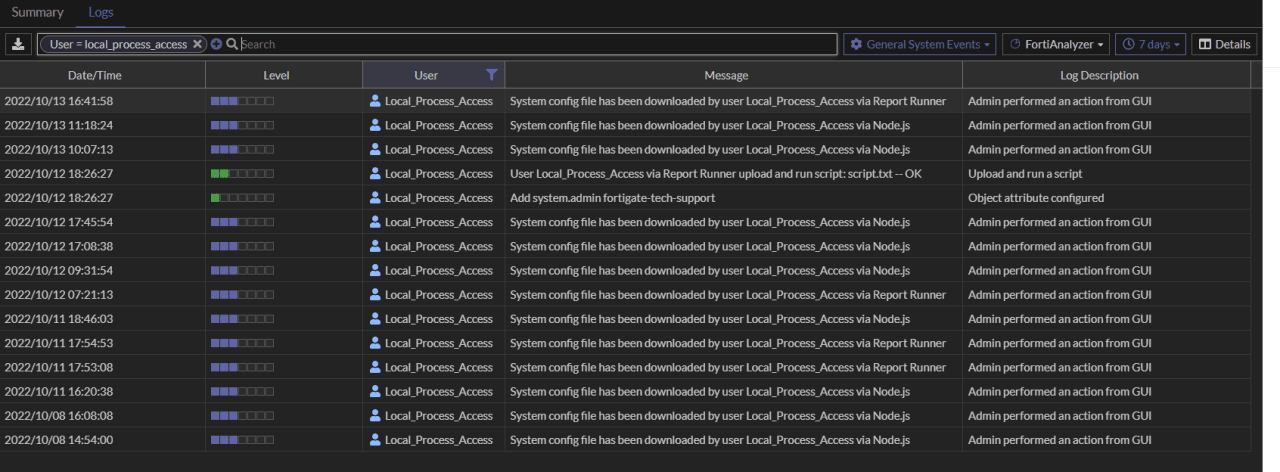
Supply: Fortinet
German information web site Heise analyzed the information leak and in addition mentioned that it was gathered in 2022, with all units using FortiOS firmware 7.0.0-7.0.6 or 7.2.0-7.2.2.
“All units have been outfitted with FortiOS 7.0.0-7.0.6 or 7.2.0-7.2.2, most with model 7.2.0. We didn’t discover any FortiOS model within the information trove that was newer than model 7.2.2, launched on October 3, 2022,” Heise reported.
Nevertheless, FortiOS 7.2.2 fastened the CVE-2022–40684 flaw, so it might be unclear how units working that model could possibly be exploited with this vulnerability.
Regardless that these configuration information have been collected in 2022, Beaumont warns that they nonetheless expose plenty of delicate details about a community’s defenses.
This consists of firewall guidelines and credentials that, if not modified on the time, ought to be modified instantly now that the information has been launched to a broader pool of risk actors.
Beaumont says that he plans to launch a listing of the IP addresses within the leak so FortiGate admins can know if the leak impacted them.
BleepingComputer additionally reached out to each the risk actors and Fortinet with questions concerning the leak and can replace the story if we obtain a response.

