Microsoft has fastened a recognized difficulty stopping Linux from booting on dual-boot methods with Safe Boot enabled after putting in the August 2024 Home windows safety updates.
The record of affected methods consists of these operating consumer (Home windows 10 and Home windows 11) and server (Home windows Server 2012 and later) OS variations.
This difficulty is triggered by a Safe Boot Superior Concentrating on (SBAT) replace that blocks UEFI shim bootloaders weak to exploits focusing on the CVE-2022-2601 GRUB2 Safe Boot bypass.
Whereas Microsoft mentioned within the CVE-2022-2601 advisory that this SBAT replace would not be delivered to gadgets the place twin booting is detected, it additionally acknowledged that the dual-boot detection did not detect some custom-made strategies of dual-booting and utilized the replace anyway.
As revealed by many Linux customers (operating a variety of distros, together with however not restricted to Ubuntu, Zorin OS, Linux Mint, and Pet Linux), their methods stopped booting after putting in the August 2024 Home windows updates, and the SBAT replace was incorrectly utilized.
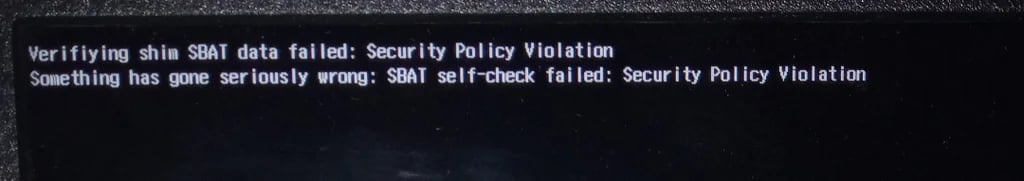
Microsoft confirmed the recognized difficulty following widespread studies, saying that affected customers noticed “One thing has gone significantly flawed: SBAT self-check failed: Safety Coverage Violation” errors on methods rendered unbootable.
Mounted after 9 months
This week, 9 months after confirming the difficulty, Microsoft introduced that the Might 2025 Patch Tuesday safety updates ought to repair the boot issues for all affected customers.
“This difficulty was resolved by Home windows updates launched Might 13, 2025 [..], and later,” Redmond famous in a Home windows launch well being replace. “We advocate you put in the newest replace on your system because it incorporates vital enhancements and difficulty resolutions, together with this one.”
The repair comes after the corporate shared a short lived workaround in late August, weeks after the primary person studies surfaced, to assist revive impacted dual-boot methods, requiring them to delete the SBAT replace and making certain that future SBAT updates would now not be put in.
On September 19, it additionally stopped making use of the problematic SBAT replace to the firmware mechanically, advising those that wish to forestall future SBAT updates in Home windows to run the next command:
reg add HKEY_LOCAL_MACHINESYSTEMCurrentControlSetControlSecureBootSBAT /v OptOut /d 1 /t REG_DWORD
“This recognized difficulty solely happens with the set up of the August 2024 safety and preview updates. The September 2024 safety replace and later updates don’t comprise the settings that brought on this difficulty,” Microsoft added.


