Microsoft introduced that it’s going to disable the 30-year-old NTLM authentication protocol by default in upcoming Home windows releases on account of safety vulnerabilities that expose organizations to cyberattacks.
NTLM (quick for New Expertise LAN Supervisor) is a challenge-response authentication protocol launched in 1993 with Home windows NT 3.1 and is the successor to the LAN Supervisor (LM) protocol.
Kerberos has outmoded NTLM and is now the present default protocol for domain-connected units operating Home windows 2000 or later. Whereas it was the default protocol in older Home windows variations, NTLM remains to be used in the present day as a fallback authentication methodology when Kerberos is unavailable, regardless that it makes use of weak cryptography and is susceptible to assaults.
Since its launch, NTLM has been extensively exploited in NTLM relay assaults (the place menace actors pressure compromised community units to authenticate towards attacker-controlled servers) to escalate privileges and take full management over the Home windows area. Regardless of this, NTLM remains to be used on Home windows servers, permitting attackers to use vulnerabilities reminiscent of PetitPotam, ShadowCoerce, DFSCoerce, and RemotePotato0 to bypass NTLM relay assault mitigations.
NTLM has additionally been focused by pass-the-hash assaults, during which cybercriminals exploit system vulnerabilities or deploy malicious software program to steal NTLM hashes (hashed passwords) from focused methods. These hashed passwords are used to authenticate because the compromised person, permitting the attackers to steal delicate knowledge and unfold laterally throughout the community.
“Blocked and not used robotically”
On Thursday, as a part of a broader push towards passwordless, phishing-resistant authentication strategies, Microsoft introduced that NTLM will lastly be disabled by default within the subsequent main Home windows Server launch and related Home windows consumer variations, marking a major shift away from the legacy protocol to safer Kerberos-based authentication.
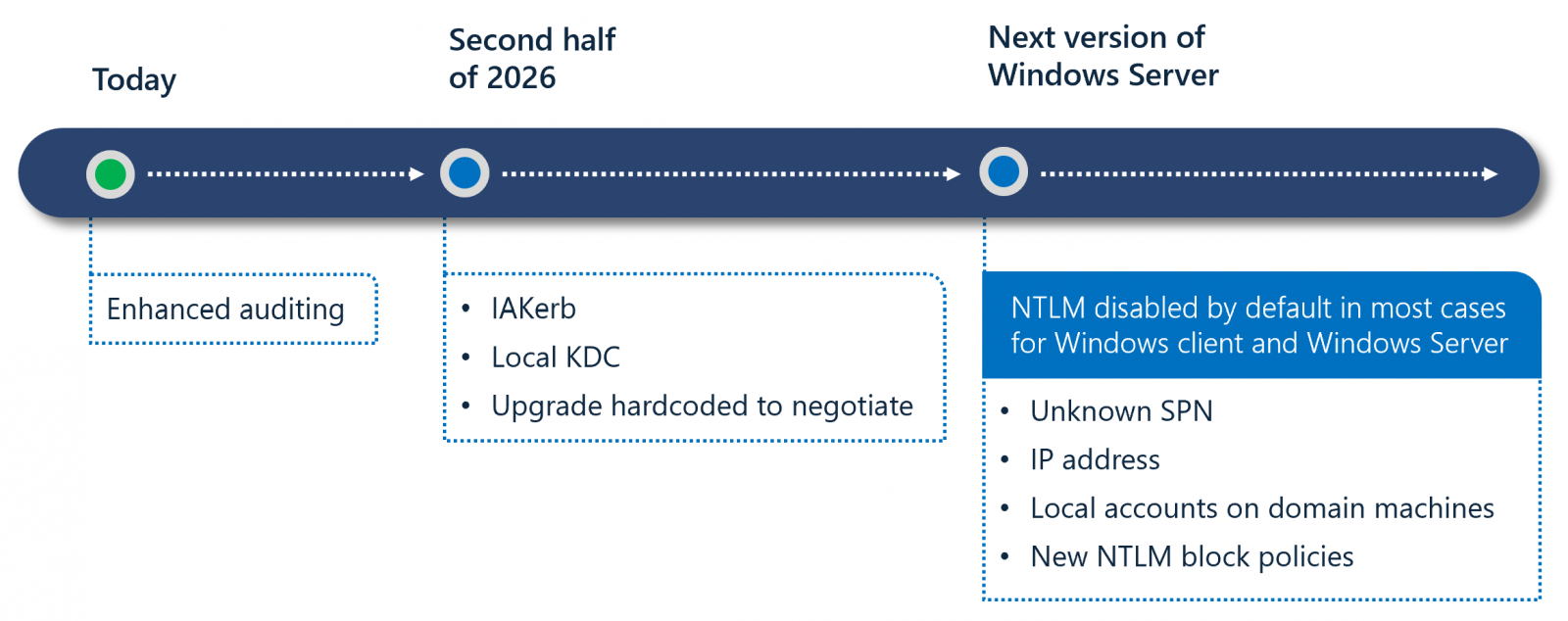
Microsoft additionally outlined a three-phase transition plan designed to mitigate NTLM-related dangers whereas minimizing disruption. In part one, admins will be capable to use enhanced auditing instruments accessible in Home windows 11 24H2 and Home windows Server 2025 to establish the place NTLM remains to be in use.
Part two, scheduled for the second half of 2026, will introduce new options, reminiscent of IAKerb and a Native Key Distribution Heart, to deal with widespread eventualities that set off NTLM fallback.
Part three will disable community NTLM by default in future releases, regardless that the protocol will stay current within the working system and could be explicitly re-enabled via coverage controls if wanted.
”Disabling NTLM by default doesn’t imply utterly eradicating NTLM from Home windows but. As an alternative, it signifies that Home windows will probably be delivered in a secure-by-default state the place community NTLM authentication is blocked and not used robotically,” Microsoft mentioned.
“The OS will favor trendy, safer Kerberos-based alternate options. On the identical time, widespread legacy eventualities will probably be addressed via new upcoming capabilities reminiscent of Native KDC and IAKerb (pre-release).”
Microsoft first introduced plans to retire the NTLM authentication protocol in October 2023, noting that it additionally wished to increase administration controls to provide directors higher flexibility in monitoring and proscribing NTLM utilization inside their environments.
It additionally formally deprecated NTLM authentication on Home windows and Home windows servers in July 2024, advising builders to transition to Kerberos or Negotiation authentication to forestall future points.
Microsoft has been warning builders to cease utilizing NTLM of their apps since 2010 and advising Home windows admins to both disable NTLM or configure their servers to dam NTLM relay assaults utilizing Lively Listing Certificates Companies (AD CS).



