Not less than 11 state-backed hacking teams from North Korea, Iran, Russia, and China have been exploiting a brand new Home windows vulnerability in knowledge theft and cyber espionage zero-day assaults since 2017.
Nevertheless, as safety researchers Peter Girnus and Aliakbar Zahravi with Development Micro’s Zero Day Initiative (ZDI) reported at the moment, Microsoft tagged it as “not assembly the bar servicing” in late September and stated it would not launch safety updates to deal with it.
“We found almost a thousand Shell Hyperlink (.lnk) samples that exploit ZDI-CAN-25373; nevertheless, it’s possible that the whole variety of exploitation makes an attempt are a lot greater,” they stated. “Subsequently, we submitted a proof-of-concept exploit by way of Development ZDI’s bug bounty program to Microsoft, who declined to deal with this vulnerability with a safety patch.”
A Microsoft spokesperson was not instantly accessible for remark when contacted by BleepingComputer earlier at the moment.
Whereas Microsoft has but to assign a CVE-ID to this vulnerability, Development Micro is monitoring it internally as ZDI-CAN-25373 and stated it allows attackers to execute arbitrary code on affected Home windows methods.
Because the researchers discovered whereas investigating in-the-wild ZDI-CAN-25373 exploitation, the safety flaw has been exploited in widespread assaults by many state-sponsored menace teams and cybercrime gangs, together with Evil Corp, APT43 (Kimsuky), Bitter, APT37, Mustang Panda, SideWinder, RedHotel, Konni, and others.
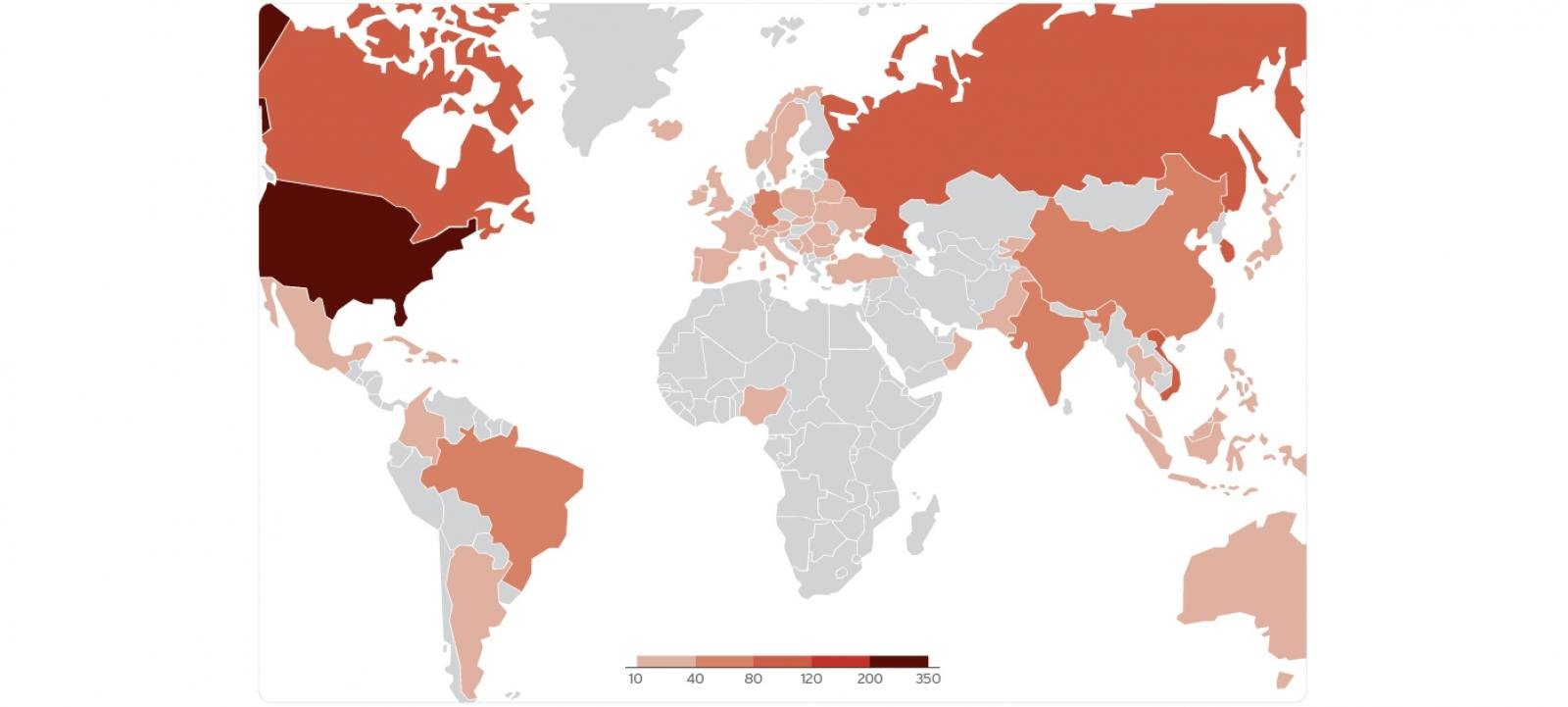
Though the campaigns have focused victims worldwide, they have been primarily targeted on North America, South America, Europe, East Asia, and Australia. Out of all of the assaults analyzed, almost 70% had been linked to espionage and data theft, whereas monetary achieve was the main target of solely 20%.
”Numerous malware payloads and loaders like Ursnif, Gh0st RAT, and Trickbot have been tracked in these campaigns, with malware-as-a-service (MaaS) platforms complicating the menace panorama,” Development Micro added.
The ZDI-CAN-25373 Home windows zero-day
The Home windows zero-day, tracked as ZDI-CAN-25373, is brought on by a Consumer Interface (UI) Misrepresentation of Crucial Data (CWE-451) weak point, which permits attackers to take advantage of how Home windows shows shortcut (.lnk) information to evade detection and execute code on weak gadgets with out the consumer’s data.
Menace actors exploit ZDI-CAN-25373 by hiding malicious command-line arguments inside .LNK shortcut information utilizing padded whitespaces added to the COMMAND_LINE_ARGUMENTS construction.
The researchers say these whitespaces may be within the type of hex codes for Area (x20), Horizontal Tab (x09), Linefeed (x0A), Vertical Tab (x0B), Kind Feed (x0C), and Carriage Return (x0D) that can be utilized as padding.
If a Home windows consumer inspects such a .lnk file, the malicious arguments will not be displayed within the Home windows consumer interface due to the added whitespaces. Consequently, the command line arguments added by the attackers stay hidden from the consumer’s view.
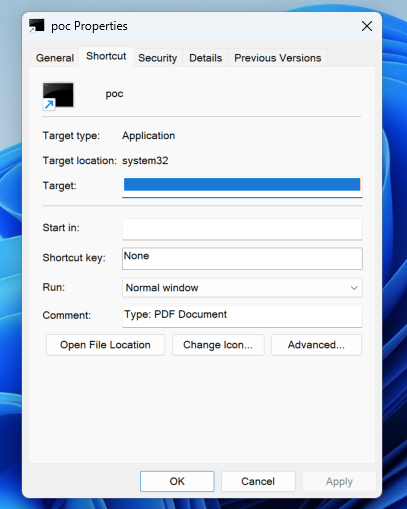
“Consumer interplay is required to take advantage of this vulnerability in that the goal should go to a malicious web page or open a malicious file,” a Development Micro advisory issued at the moment explains.
“Crafted knowledge in an .LNK file may cause hazardous content material within the file to be invisible to a consumer who inspects the file through the Home windows-provided consumer interface. An attacker can leverage this vulnerability to execute code within the context of the present consumer.”
This vulnerability is just like one other flaw tracked as CVE-2024-43461 that enabled menace actors to make use of 26 encoded braille whitespace characters (%E2percentA0percent80) to camouflage HTA information that may obtain malicious payloads as PDFs. CVE-2024-43461 was discovered by Peter Girnus, a Senior Menace Researcher at Development Micro’s Zero Day, and patched by Microsoft through the September 2024 Patch Tuesday.
The Void Banshee APT hacking group exploited CVE-2024-43461 in zero-day assaults to deploy information-stealing malware in campaigns towards organizations throughout North America, Europe, and Southeast Asia.


