Software safety posture administration firm Apiiro at present has launched two open-source instruments to assist organizations defend in opposition to malicious code of their functions. The motion comes on the heels of Apiiro’s safety analysis that exhibits hundreds of malicious code cases in repositories and packages.
In keeping with the corporate, its focus within the analysis was deep code evaluation and analyzing malicious samples for patterns to search out methods to defend in opposition to malicious code. “Malicious code is among the most accessible and easy-to-execute assault vectors,” the corporate wrote in a weblog concerning the analysis. “The safety of dependency managers and supply code internet hosting platforms continues to be evolving, with massive gaps in areas like human-to-digital identification verification, supply and launch validation, and extra. Main safety gaps additionally exist in construct techniques, artifact managers, and pipeline instruments.”
Malicious code is launched through anti-patterns, the analysis discovered, and obfuscated code is a key anti-pattern. A second anti-pattern is naive code execution, underneath which the code is acquired as information and executed on the fly, with none alternative to scan it previous to supply.
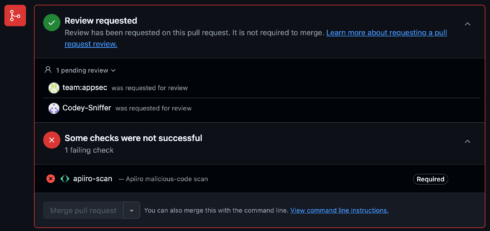
The analysis discovered that the introduction of malicious code could be detected a majority of the time utilizing the brand new open-source instruments the corporate is releasing at present. The primary is PRevent, which the corporate described as “an open-source app for scanning pull requests occasions, notifying you of suspicious code, and providing seamless integration, excessive configurability, and important orchestration options.”
The second open-source instrument launched at present is a malicious code detection ruleset to run on Semgrep, which has been forked by Opengrep after the previous determined to maneuver its engine onto a proprietary license as that firm seems to be to monetize components of the undertaking.
Apiiro means that the very best place to stop malicious code from getting into the codebase is thru use of a pre-merge hook, which it defined is “triggered by pull request occasions through webjooks and managed by strictly permissioned entities.” PRevent can kick off code evaluations and even block merges till a scan passes or a reviewer grants approval.
Extra on Opengrep
The Semgrep undertaking has been round since 2017, and is extensively used within the trade. Its two components are the pattern-matching OSS Engine and OSS Guidelines, a shared repository of guidelines created by Semgrep and open for contributions from the neighborhood.
In December 2024, Semgrep introduced adjustments to the OSS Engine license, taking it behind a business license, in impact eradicating that important piece from the open supply neighborhood. You will need to word that the license of Semgrep Group Version didn’t change; it has been and stays LGPL 2.1.
One of many issues Semgrep did was to remove JSON and Serif, a format for outputting outcomes from the OSS Engine, in keeping with Varun Badhwar, founder and CEO at Endor Labs, which is certainly one of greater than 10 firms which have created the Opengrep fork. “The writing was on the wall to vary the title from open supply to Group Version,” he mentioned. “We expect the Semgrep OSS Engine is all too essential for it to be now within the palms of 1 firm to find out the longer term.”
Organizations that create open supply after which change their licenses – for any variety of causes – it’s normally for monetary causes. Ann Schlemmer, CEO at open supply database firm Percona, mentioned that “By doing so, they’re breaking the neighborhood’s belief and undermining what open supply is supposed to be.”
“What I’d moderately see is individuals being as clear as they’ll,” she added. “For those who imagine in your undertaking that you just’ve performed, and also you additionally wish to proceed so as to add worth, then be unapologetic about going open core, or deciding what you will give to the neighborhood underneath that open supply license, after which what you will maintain again. Your IP is your IP, however when you put one thing out underneath an open supply license, it’s very nicely outlined. It’s sort of all people’s IP at that time.”
Badhwar famous that the businesses behind the Opengrep fork are solely momentary stewards of the undertaking. “We have now very clearly dedicated publicly that we’re simply as an interim [group] organizing this long run. We wish to hand this over to a basis to run.” He mentioned the businesses haven’t but decided which basis could be most acceptable, however added, “We have now already collectively come collectively and invested in hiring full-time engineers to work on this engine. Our purpose is to convey again, on the very least, all the pieces that Semgrep took away in December’s announcement, however extra importantly, put in much more funding on efficiency, on compatibility with Home windows, for instance, with eradicating a number of the restrictions on multi-file evaluation that it has within the open supply version.”
Schlemmer thinks this transfer to place open-source initiatives into foundations goes to be a pattern. “If firms have a very talked-about open supply undertaking that’s extensively used, after which they resolve they wish to change their license — once more, financial causes, no apologies for someone getting cash off of what they’ve put out – working to the foundations, I believe, is a technique to ensure that we keep belief in open supply, and now have a sustainability of a very common undertaking.”

