Are you incurring vital cross Availability Zone visitors prices when working an Apache Kafka consumer in containerized environments on Amazon Elastic Kubernetes Service (Amazon EKS) that eat information from Amazon Managed Streaming for Apache Kafka (Amazon MSK) matters?
For those who’re not accustomed to Apache Kafka’s rack consciousness characteristic, we strongly advocate beginning with the weblog submit on how one can Cut back community visitors prices of your Amazon MSK customers with rack consciousness for an in-depth rationalization of the characteristic and the way Amazon MSK helps it.
Though the answer described in that submit makes use of an Amazon Elastic Compute Cloud (Amazon EC2) occasion deployed in a single Availability Zone to eat messages from an Amazon MSK matter, trendy cloud-native architectures demand extra dynamic and scalable approaches. Amazon EKS has emerged as a number one platform for deploying and managing distributed purposes. The dynamic nature of Kubernetes introduces distinctive implementation challenges in comparison with static consumer deployments. On this submit, we stroll you thru an answer for implementing rack consciousness in client purposes which are dynamically deployed throughout a number of Availability Zones utilizing Amazon EKS.
Right here’s a fast recap of some key Apache Kafka terminology from the referenced weblog. An Apache Kafka consumer client will register to learn towards a matter. A subject is the logical information construction that Apache Kafka organizes information into. A subject is segmented right into a single or many partitions. Partitions are the unit of parallelism in Apache Kafka. Amazon MSK offers excessive availability by replicating every partition of a subject throughout brokers in numerous Availability Zones. As a result of there are replicas of every partition that reside throughout the totally different brokers that make up your MSK cluster, Amazon MSK additionally tracks whether or not a duplicate partition is in sync with the latest information for that partition. This implies there’s one partition that Amazon MSK acknowledges as containing probably the most up-to-date information, and this is called the chief partition. The gathering of replicated partitions is named in-sync replicas. This record of in-sync replicas is used internally when the cluster must elect a brand new chief partition if the present chief had been to turn into unavailable.
When client purposes learn from a subject, the Apache Kafka protocol facilitates a community trade to find out which dealer at the moment has the chief partition that the buyer must learn from. Which means the buyer might be informed to learn from a dealer in a special Availability Zone than itself, resulting in cross-zone visitors cost in your AWS account. To assist optimize this price, Amazon MSK helps the rack consciousness characteristic, utilizing which shoppers can ask an Amazon MSK cluster to offer a duplicate partition to learn from, inside the identical Availability Zone because the consumer, even when it isn’t the present chief partition. The cluster accomplishes this by checking for an in-sync reproduction on a dealer inside the identical Availability Zone as the buyer.
The problem with Kafka shoppers on Amazon EKS
In Amazon EKS, the underlying models of computes are EC2 situations which are abstracted as Kubernetes nodes. The nodes are organized into node teams for ease of administration, scaling, and grouping of purposes on sure EC2 occasion varieties. As a greatest follow for resilience, the nodes in a node group are unfold throughout a number of Availability Zones. Amazon EKS makes use of the underlying Amazon EC2 metadata in regards to the Availability Zone that it’s positioned in, and it injects that info into the node’s metadata throughout node configuration. Particularly, the Availability Zone (AZ ID) is injected into the node metadata.
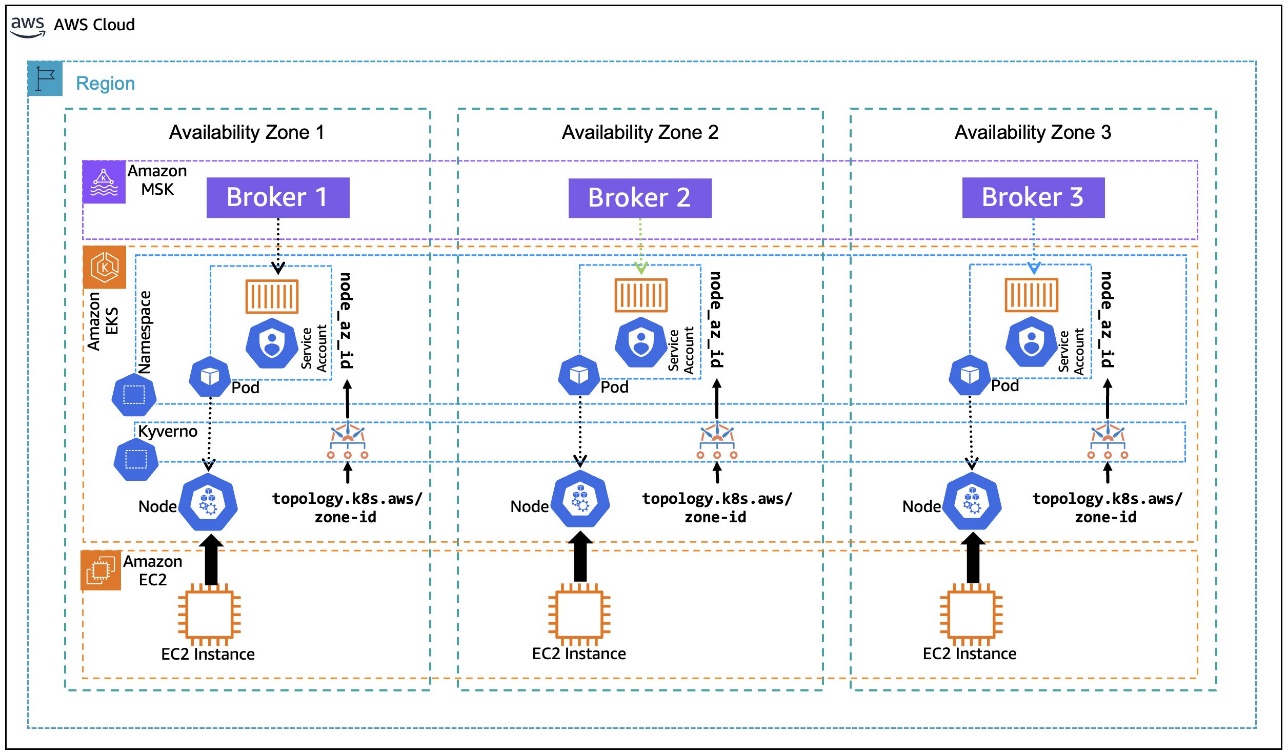
When an software is deployed in a Kubernetes Pod on Amazon EKS, it goes by a strategy of binding to a node that meets the pod’s necessities. As proven within the following diagram, once you deploy consumer purposes on Amazon EKS, the pod for the appliance may be sure to a node with accessible capability in any Availability Zone. Additionally, the pod doesn’t robotically inherit the Availability Zone info from the node that it’s sure to, a chunk of data obligatory for rack consciousness. The next structure diagram illustrates Kafka customers working on Amazon EKS with out rack consciousness.
To set the consumer configuration for rack consciousness, the pod must know what Availability Zone it’s positioned in, dynamically, as it’s sure to a node. Throughout its lifecycle, the identical pod may be evicted from the node it was sure to beforehand and moved to a node in a special Availability Zone, if the matching standards allow that. Making the pod conscious of its Availability Zone dynamically units the rack consciousness parameter consumer.rack through the initialization of the appliance container that’s encapsulated within the pod.
After rack consciousness is enabled on the MSK cluster, what occurs if the dealer in the identical Availability Zone because the consumer (hosted on Amazon EKS or elsewhere) turns into unavailable? The Apache Kafka protocol is designed to help a distributed information storage system. Assuming prospects observe the very best follow of implementing a replication issue > 1, Apache Kafka can dynamically reroute the buyer consumer to the following accessible in-sync reproduction on a special dealer. This resilience stays constant even after implementing nearest reproduction fetching, or rack consciousness. Enabling rack consciousness optimizes the networking trade to choose a partition inside the identical Availability Zone, however it doesn’t compromise the buyer’s potential to function if the closest reproduction is unavailable.
On this submit, we stroll you thru an instance of how one can use the Kubernetes metadata label, topology.k8s.aws/zone-id, assigned to every node by Amazon EKS, and use an open supply coverage engine, Kyverno, to deploy a coverage that mutates the pods which are within the binding state to dynamically inject the node’s AZ ID into the pod’s metadata as an annotation, as depicted within the following diagram. This annotation, in flip, is utilized by the container to create an atmosphere variable that’s assigned the pod’s annotated AZ ID info. The atmosphere variable is then used within the container postStart lifecycle hook to generate the Kafka consumer configuration file with rack consciousness setting. The next structure diagram illustrates Kafka customers working on Amazon EKS with rack consciousness.
Answer Walkthrough
Stipulations
For this walkthrough, we use AWS CloudShell to run the scripts which are offered inline as you progress. For a easy expertise, earlier than getting began, ensure to have kubectl and eksctl put in and configured within the AWS CloudShell atmosphere, following the set up directions for Linux (amd64). Helm can be required to be set up on AWS CloudShell, utilizing the directions for Linux.
Additionally, examine if the envsubst device is put in in your CloudShell atmosphere by invoking:
If the device isn’t put in, you may set up it utilizing the command:
We additionally assume you have already got an MSK cluster deployed in an Amazon Digital Personal Cloud (VPC) in three Availability Zones with the identify MSK-AZ-Conscious. On this walkthrough, we use AWS Identification and Entry Administration (IAM) authentication for consumer entry management to the MSK cluster. For those who’re utilizing a cluster in your account with a special identify, change the situations of MSK-AZ-Conscious within the directions.
We observe the identical MSK cluster configuration talked about within the Rack Consciousness weblog talked about beforehand, with some modifications. (Make sure you’ve set reproduction.selector.class = org.apache.kafka.frequent.reproduction.RackAwareReplicaSelector for the explanations mentioned there). In our configuration, we add one line: num.partitions = 6. Though not necessary, this ensures that matters which are robotically created could have a number of partitions to help clearer demonstrations in subsequent sections.
Lastly, we use the Amazon MSK Information Generator with the next configuration:
Operating the MSK Information Generator with this configuration will robotically create a six-partition matter named MSK-AZ-Conscious-Matter on our cluster for us, and it’ll push information to that matter. To observe together with the walkthrough, we advocate and assume that you just deploy the MSK Information Generator to create the subject and populate it with simulated information.
Create the EKS cluster
Step one is to put in an EKS cluster in the identical Amazon VPC subnets because the MSK cluster. You may modify the identify of the MSK cluster by altering that atmosphere variable MSK_CLUSTER_NAME in case your cluster is created with a special identify than urged. You can too change the Amazon EKS cluster identify by altering EKS_CLUSTER_NAME.
The atmosphere variables that we outline listed here are used all through the walkthrough.
The final step is to replace the kubeconfig with an entry for the EKS cluster:
Subsequent, it’s essential to create an IAM coverage, MSK-AZ-Conscious-Coverage, to permit entry from the Amazon EKS pods to the MSK cluster. Be aware right here that we’re utilizing MSK-AZ-Conscious because the cluster identify.
Create a file, msk-az-aware-policy.json, with the IAM coverage template:
To create the IAM coverage, use the next command. It first replaces the placeholders within the coverage file with values from related atmosphere variables, after which creates the IAM coverage:
Configure EKS Pod Identification
Amazon EKS Pod Identification provides a simplified expertise for acquiring IAM permissions for pods on Amazon EKS. This requires putting in an add-on Amazon EKS Pod Identification Agent to the EKS cluster:
Affirm that the add-on has been put in and its standing is ACTIVE and that the standing of all of the pods related to the add-on is Operating.
After you’ve put in the add-on, it’s essential to create a pod id affiliation between a Kubernetes service account and the IAM coverage created earlier:
Set up Kyverno
Kyverno is an open supply coverage engine for Kubernetes that permits for validation, mutation, and era of Kubernetes assets utilizing insurance policies written in YAML, thus simplifying the enforcement of safety and compliance necessities. It is advisable set up Kyverno to dynamically inject metadata into the Amazon EKS pods as they enter the binding state to tell them of Availability Zone ID.
In AWS CloudShell, create a file named kyverno-values.yaml. This file defines the Kubernetes RBAC permissions for Kyverno’s Admission Controller to learn Amazon EKS node metadata as a result of the default Kyverno (v. 1.13 onwards) settings don’t permit this:
After this file is created, you may set up Kyverno utilizing helm and offering the values file created within the earlier step:
Beginning with Kyverno v 1.13, the Admission Controller is configured to disregard the AdmissionReview requests for pods in binding state. This must be modified by modifying the Kyverno ConfigMap:
The kubectl edit command makes use of the default editor configured in your atmosphere (in our case Linux VIM).
This may open the ConfigMap in a textual content editor.
As highlighted within the following screenshot, [Pod/binding,*,*] must be faraway from the resourceFilters discipline for the Kyverno Admission Controller to course of AdmissionReview requests for pods in binding state.
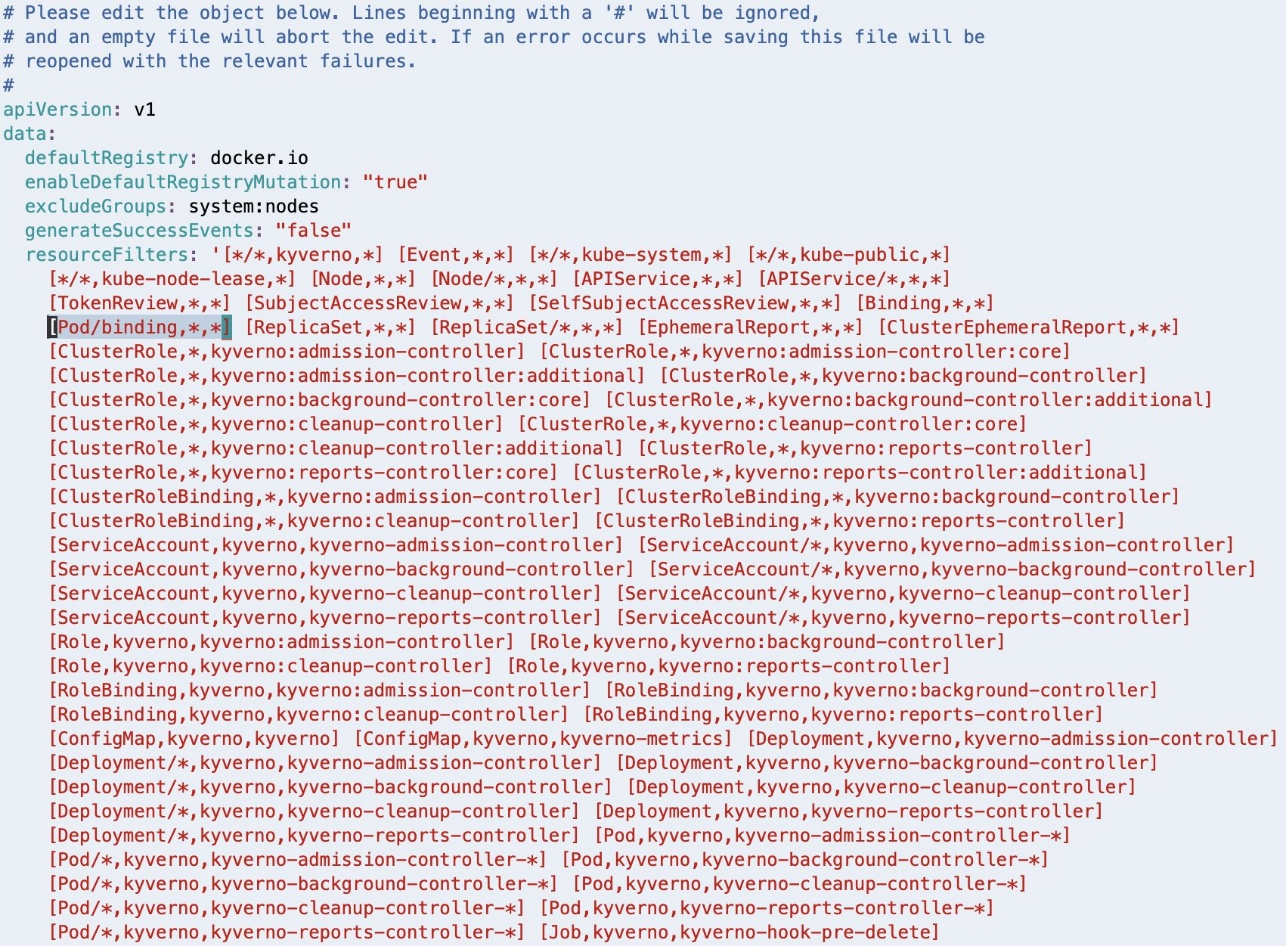
If Linux VIM is your default editor, you may delete the entry utilizing VIM command 18x, which means delete (or minimize) 18 characters from the present cursor place. Save the modified configuration utilizing the VIM command :wq, which means write (or save) the file and stop.
After deleting, the resourceFilters discipline ought to look much like the next screenshot.
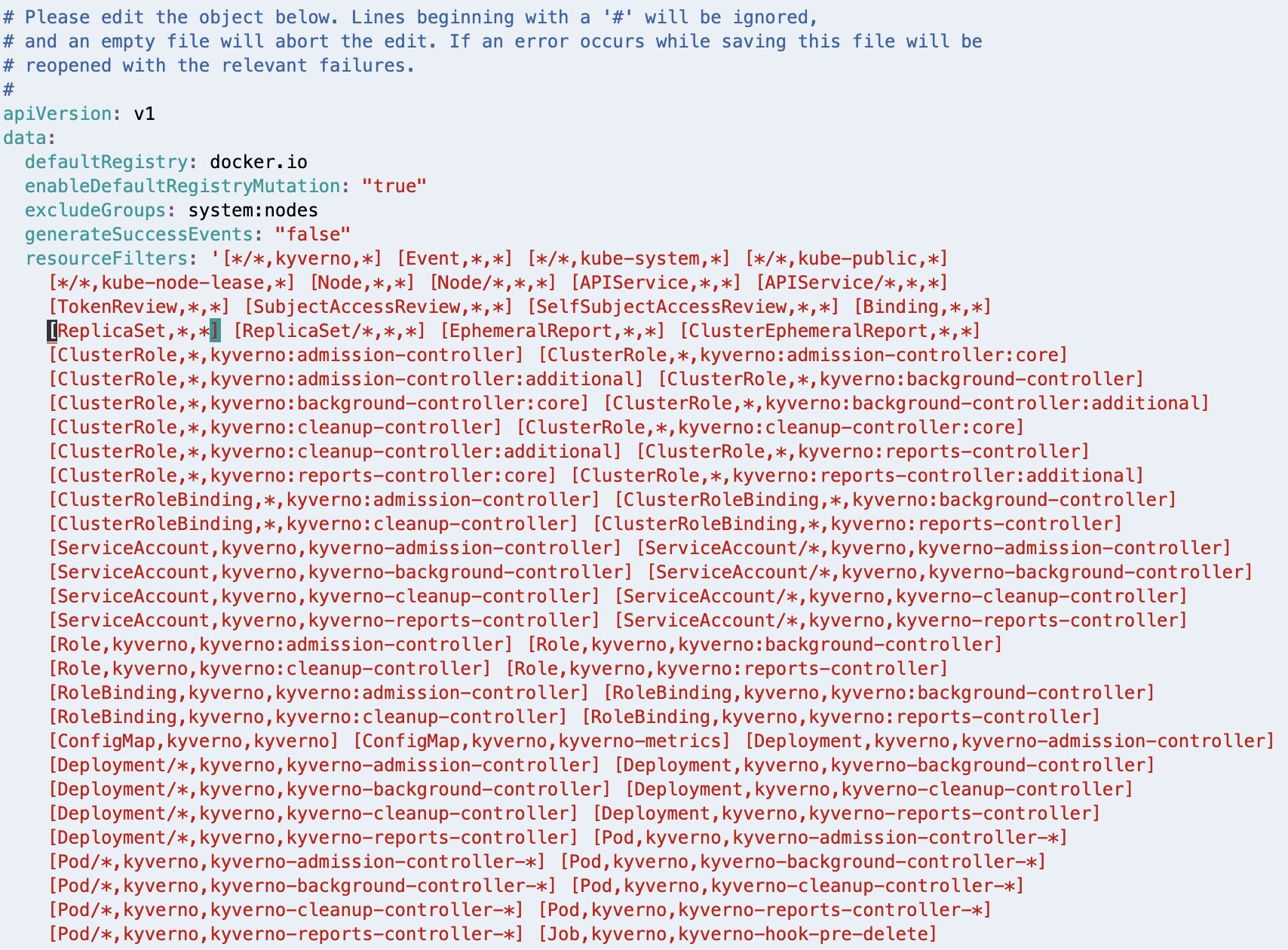
When you’ve got a special editor configured in your atmosphere, observe the suitable steps to realize the same end result.
Configure Kyverno coverage
It is advisable configure the coverage that can make the pods rack conscious. This coverage is customized from the urged method within the Kyverno weblog submit, Assigning Node Metadata to Pods. Create a brand new file with the identify kyverno-inject-node-az-id.yaml:
It instructs Kyverno to observe for pods in binding state. After Kyverno receives the AdmissionReview request for a pod, it units the variable node to the identify of the node to which the pod is being sure. It additionally units one other variable node_az_id to the Availability Zone ID by calling the Kubernetes API /api/v1/nodes/node to get the node metadata label topology.k8s.aws/zone-id. Lastly, it defines a mutate rule to inject the obtained AZ ID into the pod’s metadata as an annotation node_az_id.
After you’ve created the file, apply the coverage utilizing the next command:
Deploy a pod with out rack consciousness
Now let’s visualize the issue assertion. To do that, connect with one of many EKS pods and examine the way it interacts with the MSK cluster once you run a Kafka client from the pod.
First, get the bootstrap string of the MSK cluster. Lookup the Amazon Useful resource Names (ARNs) of the MSK cluster:
Utilizing the cluster ARN, you will get the bootstrap string with the next command:
Create a brand new file named kafka-no-az.yaml:
This pod manifest doesn’t make use of the Availability Zone ID injected into the metadata annotation and therefore doesn’t add consumer.rack to the consumer.properties configuration.
Deploy the pods utilizing the next command:
Run the next command to verify that the pods have been deployed and are within the Operating state:
Choose a pod id from the output of the earlier command, and connect with it utilizing:
Run the Kafka client:
This command will dump all of the ensuing logs into the file, non-rack-aware-consumer.log. There’s numerous info in these logs, and we encourage you to open them and take a deeper look. Subsequent, study the EKS pod in motion. To do that, run the next command to tail the file to view fetch request outcomes to the MSK cluster. You’ll discover a handful of significant logs to evaluation as the buyer entry numerous partitions of the Kafka matter:
Observe your log output, which ought to look much like the next:
You’ve now related to a selected pod within the EKS cluster and run a Kafka client to learn from the MSK matter with out rack consciousness. Keep in mind that this pod is working inside a single Availability Zone.
Reviewing the log output, you discover rack: values as use1-az2, use1-az4, and use1-az6 because the pod makes calls to totally different partitions of the subject. These rack values characterize the Availability Zone IDs that our brokers are working inside. Which means our EKS pod is creating networking connections to brokers throughout three totally different Availability Zones, which might be accruing networking fees in our account.
Additionally discover that you don’t have any solution to examine which node, and subsequently Availability Zone, this EKS pod is working in. You may observe within the logs that it’s calling to MSK brokers in numerous Availability Zones, however there isn’t a solution to know which dealer is in the identical Availability Zone because the EKS pod you’ve related to. Delete the deployment once you’re finished:
Deploy a pod with rack consciousness
Now that you’ve skilled the buyer conduct with out rack consciousness, it’s essential to inject the Availability Zone ID to make your pods rack-aware.
Create a brand new file named kafka-az-aware.yaml:
As you may observe, the pod manifest defines an atmosphere variable NODE_AZ_ID, assigning it the worth from the pod’s personal metadata annotation node_az_id that was injected by Kyverno. The manifest then makes use of the pod’s postStart lifecycle script so as to add consumer.rack into the consumer.properties configuration, setting it equal to the worth within the atmosphere variable NODE_AZ_ID.
Deploy the pods utilizing the next command:
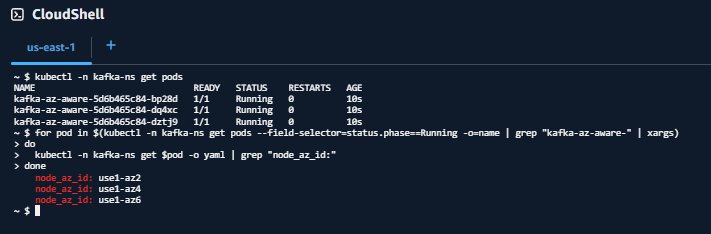
Run the next command to verify that the pods have been deployed and are within the Operating state:
Confirm that Availability Zone Ids have been injected into the pods
Your output ought to look much like:
Or:
Choose a pod id from the output of the get pods command and shell-in to it.
The output of the get $pod command matches the order of outcomes from the get pods command. This matching will make it easier to perceive what Availability Zone your pod is working in so you may evaluate it to log outputs later.
After you’ve related to your pod, run the Kafka client:
Much like earlier than, this command will dump all of the ensuing logs into the file, rack-aware-consumer.log. You create a brand new file so there’s no overlap between the Kafka customers you’ve run. There’s numerous info in these logs, and we encourage you to open them and take a deeper look. If you wish to see the rack consciousness of your EKS pod in motion, run the next command to tail the file to view fetch request outcomes to the MSK cluster. You may observe a handful of significant logs to evaluation right here as the buyer entry numerous partitions of the Kafka matter:
Observe your log output, which ought to look much like the next:
For every log line, now you can observe two rack: values. The primary rack: worth reveals the present chief, the second rack: reveals the rack that’s getting used to fetch messages.
For instance, take a look at MSK-AZ-Conscious-Matter-5. The chief is recognized as rack: use1-az4, however the fetch request is distributed to use1-az6 as indicated by to node b-2.mskazaware.hxrzlh.c6.kafka.us-east-1.amazonaws.com:9098 (id: 2 rack: use1-az6) (org.apache.kafka.shoppers.client.internals.AbstractFetch)
You’ll discover one thing comparable in all different log strains. The fetch is at all times to the dealer in use1-az6, which maps to our expectation, given the pod we related to was on this Availability Zone.
Congratulations! You’re consuming from the closest reproduction on Amazon EKS.
Clear Up
Delete the deployment when completed:
To delete the EKS Pod Identification affiliation:
To delete the IAM coverage:
To delete the EKS cluster:
For those who adopted together with this submit utilizing the Amazon MSK Information Generator, be sure you delete your deployment so it’s now not trying to generate and ship information after you delete the remainder of your assets.
Clear up will depend upon which deployment possibility you used. To learn extra in regards to the deployment choices and the assets created for the Amazon MSK Information Generator, consult with Getting Began within the GitHub repository.
Creating an MSK cluster was a prerequisite of this submit, and when you’d like to wash up the MSK cluster as properly, you should use the next command:
aws kafka delete-cluster --cluster-arn "${MSK_CLUSTER_ARN}"
There isn’t any extra price to utilizing AWS CloudShell, however when you’d prefer to delete your shell, consult with the Delete a shell session house listing within the AWS CloudShell Person Information.
Conclusion
Apache Kafka nearest reproduction fetching, or rack consciousness, is a strategic cost-optimization method. By implementing it for Amazon MSK customers on Amazon EKS, you may considerably scale back cross-zone visitors prices whereas sustaining strong, distributed streaming architectures. Open supply instruments corresponding to Kyverno can simplify complicated configuration challenges and drive significant financial savings.The answer we’ve demonstrated offers a robust, repeatable method to dynamically injecting Availability Zone info into Kubernetes pods, optimize Kafka client routing, and reduce scale back switch prices.
Extra assets
To study extra about rack consciousness with Amazon MSK, consult with Cut back community visitors prices of your Amazon MSK customers with rack consciousness.
Concerning the authors
 Austin Groeneveld is a Streaming Specialist Options Architect at Amazon Internet Companies (AWS), based mostly within the San Francisco Bay Space. On this function, Austin is enthusiastic about serving to prospects speed up insights from their information utilizing the AWS platform. He’s significantly fascinated by the rising function that information streaming performs in driving innovation within the information analytics house. Outdoors of his work at AWS, Austin enjoys watching and taking part in soccer, touring, and spending high quality time together with his household.
Austin Groeneveld is a Streaming Specialist Options Architect at Amazon Internet Companies (AWS), based mostly within the San Francisco Bay Space. On this function, Austin is enthusiastic about serving to prospects speed up insights from their information utilizing the AWS platform. He’s significantly fascinated by the rising function that information streaming performs in driving innovation within the information analytics house. Outdoors of his work at AWS, Austin enjoys watching and taking part in soccer, touring, and spending high quality time together with his household.
 Farooq Ashraf is a Senior Options Architect at AWS, specializing in SaaS, Generative AI, and MLOps. He’s enthusiastic about mixing multi-tenant SaaS ideas with Cloud providers to innovate scalable options for the digital enterprise, and has a number of weblog posts, and workshops to his credit score.
Farooq Ashraf is a Senior Options Architect at AWS, specializing in SaaS, Generative AI, and MLOps. He’s enthusiastic about mixing multi-tenant SaaS ideas with Cloud providers to innovate scalable options for the digital enterprise, and has a number of weblog posts, and workshops to his credit score.

