Oracle is warning a few important E-Enterprise Suite zero-day vulnerability tracked as CVE-2025-61882 that enables attackers to carry out unauthenticated distant code execution, with the flaw actively exploited in Clop knowledge theft assaults.
The flaw is inside the Oracle Concurrent Processing product of Oracle E-Enterprise Suite (part: BI Writer Integration) and has a CVSS base rating of 9.8, as a result of its lack of authentication and ease of exploitation.
“This Safety Alert addresses vulnerability CVE-2025-61882 in Oracle E-Enterprise Suite,” reads a brand new Oracle advisory.
“This vulnerability is remotely exploitable with out authentication, i.e., it could be exploited over a community with out the necessity for a username and password. If efficiently exploited, this vulnerability might lead to distant code execution.”
Oracle has confirmed that the zero-day vulnerability impacts Oracle E-Enterprise Suite, variations 12.2.3-12.2.14, and has launched an emergency replace to handle the flaw. The corporate notes that clients should first set up the October 2023 Crucial Patch Replace earlier than they will set up the brand new safety updates.
Zero-day exploited in Clop knowledge theft assaults
Whereas Oracle has not explicitly acknowledged that this can be a zero-day vulnerability, they did share indicators of compromise that correspond to an Oracle EBS exploit not too long ago shared by menace actors on Telegram.
Charles Carmakal, CTO, Mandiant – Google Cloud, additionally confirmed that this was the flaw exploited by the Clop ransomware gang in knowledge theft assaults that occurred in August 2025.
“Clop exploited a number of vulnerabilities in Oracle EBS which enabled them to steal giant quantities of knowledge from a number of sufferer in August 2025,” Carmakal shared in an announcement to BleepingComputer.
“A number of vulnerabilities had been exploited together with vulnerabilities that had been patched in Oracle’s July 2025 replace in addition to one which was patched this weekend (CVE-2025-61882),” continued Carmakal.
CVE-2025-61882 is a important (9.8 CVSS) vulnerability that permits unauthenticated distant code execution.
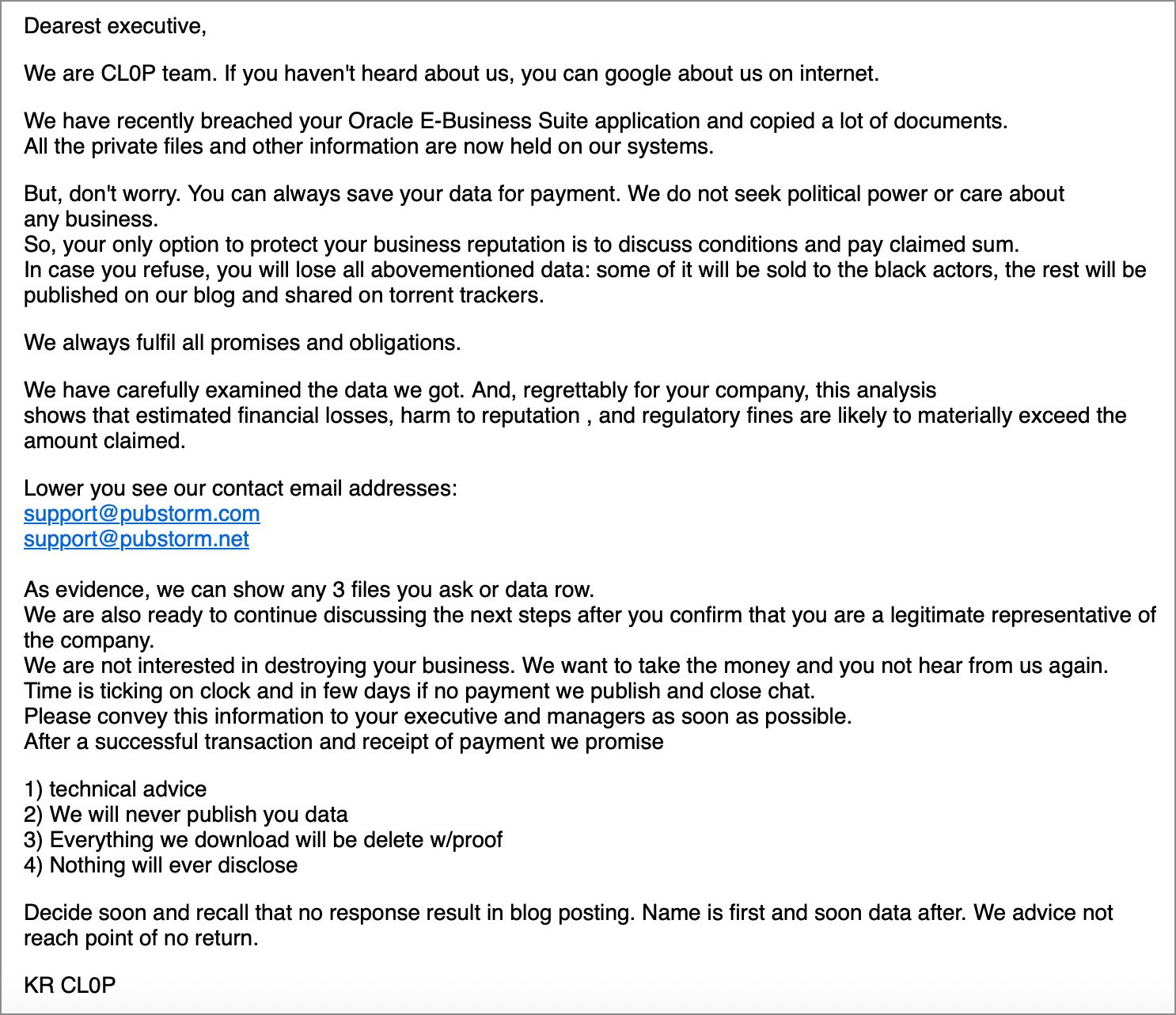
Information of Clop’s newest extortion marketing campaign first broke final week, when Mandiant and the Google Menace Intelligence Group (GTIG) reported that they had been monitoring a brand new marketing campaign during which a number of corporations obtained emails claiming to be from the menace actors.
These emails acknowledged that Clop had stolen knowledge from the corporate’s Oracle E-Enterprise Suite techniques and had been demanding a ransom to not leak the stolen knowledge.
“We’re CL0P staff. If you have not heard about us, you possibly can google about us on web,” reads the extortion electronic mail shared with BleepingComputer.
“We’ve not too long ago breached your Oracle E-Enterprise Suite software and copied a whole lot of paperwork. All of the non-public information and different data at the moment are held on our techniques.”
Supply: Google
The Clop extortion gang has an extended historical past of exploiting zero-day vulnerability in huge knowledge theft assaults, which embrace:
Clop later confirmed to BleepingComputer that they had been behind the extortion emails and indicated they exploited an Oracle zero-day vulnerability to steal the info.
“Quickly all will develop into apparent that Oracle bugged up their core product and as soon as once more, the process is on clop to avoid wasting the day,” Clop informed BleepingComputer, indicating a brand new flaw was exploited.
Nevertheless, Oracle initially linked the Clop extortion marketing campaign to vulnerabilities that had been patched in July 2025 reasonably than the brand new zero-day that we now know was used within the assaults.
Oracle has now shared indicators of compromise for the zero-day exploitation, which embrace two IP addresses seen exploiting servers, a command to open a distant shell, and the exploit archive and related information.
Exploit leaked by Scattered Lapsus$ Hunters
Whereas Clop is behind the info theft assaults and exploitation of the Oracle zero-day, information of the zero-day first got here from a unique group of menace actors who’ve been making their very own headlines these days with their widespread knowledge theft assaults on Salesforce clients.
On Friday, these actors, calling themselves “Scattered Lapsus$ Hunters” as they declare to include menace actors from Scattered Spider, Lapsus$, and ShinyHunters, leaked two information on Telegram that they mentioned had been associated to the Clop assaults.
One file named “GIFT_FROM_CL0P.7z” incorporates Oracle supply code that seems to be associated to “assist.oracle.com” based mostly on the file names.
Nevertheless, the menace actors additionally launched an “ORACLE_EBS_NDAY_EXPLOIT_POC_SCATTERED_LAPSUS_RETARD_CL0P_HUNTERS.zip” archive, which they insinuated by the filename was the Oracle E-Enterprise exploit utilized by Clop.
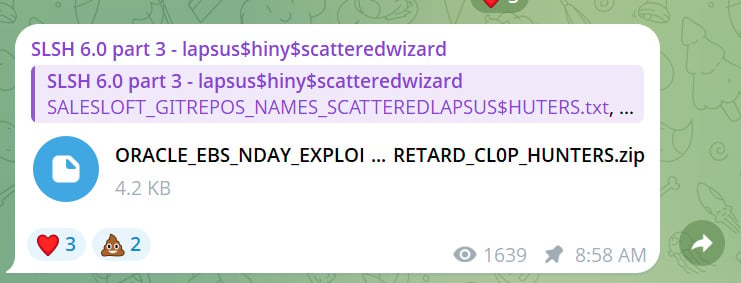
BleepingComputer has confirmed this is identical file listed in Oracle’s indicators of compromise.
This archives incorporates a readme.md instruction file and two Python scripts named exp.py and server.py. These Python scripts are used to take advantage of a weak Oracle E-Enterprise Suite occasion and both execute an arbitrary command or open a reverse shell again to the menace actor’s servers.
Because the IOCs shared by Oracle listing the title of the exploit archive shared by Scattered Lapsus$ Hunters, it’s now confirmed that that is the exploit utilized by the Clop ransomware gang.
Nevertheless, it does elevate questions on how the Scattered Lapsus$ Hunters menace actors gained entry to the exploit and whether or not they’re working with Clop in some capability.
BleepingComputer contacted representatives from each ShinyHunters and Clop to ask questions on this relationship, however has not obtained a response presently.


