Over 1,200 internet-exposed SAP NetWeaver cases are susceptible to an actively exploited most severity unauthenticated file add vulnerability that enables attackers to hijack servers.
SAP NetWeaver is an software server and growth platform that runs and connects SAP and non-SAP functions throughout completely different applied sciences.
Final week, SAP disclosed an unauthenticated file add vulnerability, tracked as CVE-2025-31324, in SAP NetWeaver Visible Composer, particularly the Metadata Uploader element.
The flaw permits distant attackers to add arbitrary executable information on uncovered cases with out authenticating, attaining code execution and full system compromise.
A number of cybersecurity companies, together with ReliaQuest, watchTowr, and Onapsis, confirmed the flaw is actively exploited in assaults, with menace actors using it to drop net shells on susceptible servers.
A SAP spokesperson advised BleepingComputer that they had been conscious of those makes an attempt and launched a workaround on April 8, 2024, adopted by a safety replace that addressed CVE-2025-31324 on April 25.
SAP advised BleepingComputer that they don’t seem to be conscious of any instances the place these assaults impacted buyer information or techniques.
Broadly exploited in assaults
Researchers have now confirmed that many susceptible SAP Netweaver servers are uncovered on the web, making them prime targets for assaults.
The Shadowserver Basis discovered the 427 uncovered servers, warning of the huge uncovered assault floor and the possibly extreme repercussions of exploitation.
Many of the susceptible techniques (149) are in america, adopted by India (50), Australia (37), China (31), Germany (30), the Netherlands (13), Brazil (10), and France (10).
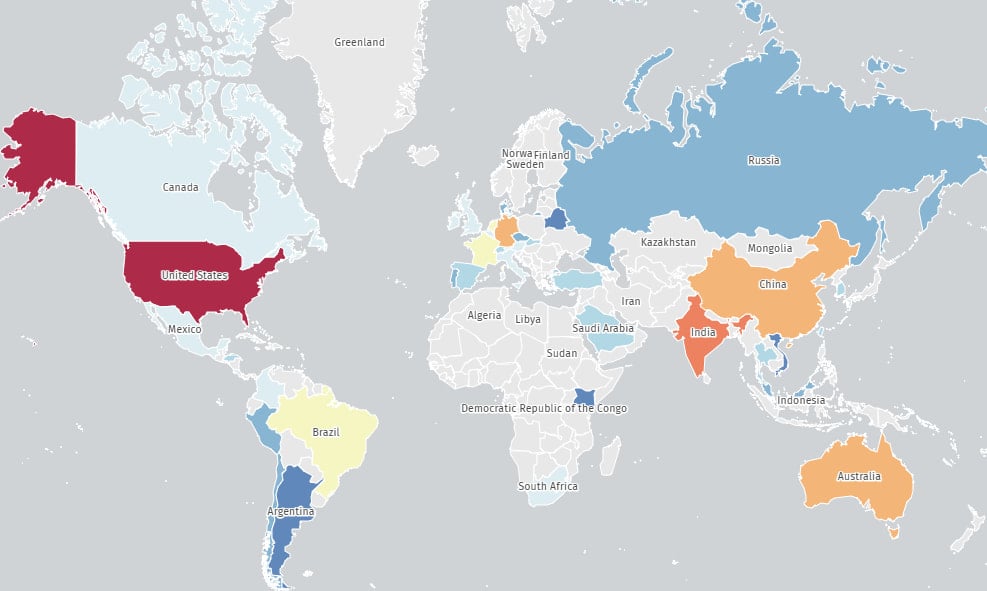
Supply: The Shadowserver Basis
Nonetheless, cyber protection search engine Onyphe paints a extra dire image, telling BleepingComputer that there are 1,284 susceptible servers uncovered on-line, with 474 already having been compromised with webshells.
“One thing like 20 Fortune 500/World 500 corporations are susceptible, and a lot of them are compromised,” Onyphe CTO Patrice Auffret advised BleepingComputer.
Researchers reported that the menace actors are using webshells with names like, “cache.jsp” and “helper.jsp.” Howver, Nextron Analysis says they’re additionally utilizing random names, making it harder to seek out susceptible Netweaver cases.
Whereas the variety of servers will not be huge, the danger remains to be vital, given that enormous enterprises and multinational firms generally use SAP NetWeaver.
To deal with the danger, it is suggested that the most recent safety replace be utilized by following the seller’s directions in this bulletin.
If unable to use the replace, the under mitigations are really useful:
- Limit entry to the /developmentserver/metadatauploader endpoint.
- If Visible Composer will not be in use, think about turning it off completely.
- Ahead logs to SIEM and scan for unauthorized information within the servlet path.
RedRays has additionally launched a scanner device for CVE-2025-31324 that may assist pinpoint dangers in giant environments.
BleepingComputer contacted SAP with additional questions concerning the lively exploitation and can replace the story with any response.

