Enterprise software program large Pink Hat is now being extorted by the ShinyHunters gang, with samples of stolen buyer engagement experiences (CERs) leaked on their information leak web site.
Information of the Pink Hat information breach broke final week when a hacking group often known as the Crimson Collective claimed to have stolen practically 570GB of compressed information throughout 28,000 inside growth repositories.
This information allegedly contains roughly 800 Buyer Engagement Reviews (CERs), which might comprise delicate details about a buyer’s community, infrastructure, and platforms.
The risk actors claimed to have tried to extort Pink Hat into paying a ransom to stop the general public disclosure of the information, however obtained no response.
Pink Hat later confirmed to BleepingComputer that the breach affected its GitLab occasion, which was used solely for Pink Hat Consulting on consulting engagements.
Quickly after the breach was disclosed, risk actors often known as Scattered Lapsus$ Hunters sought to make contact with Crimson Collective.
Yesterday, Crimson Collective introduced that it had partnered with Scattered Lapsus$ Hunters to make the most of the newly launched ShinyHunters information leak web site to proceed their extortion makes an attempt towards Pink Hat.
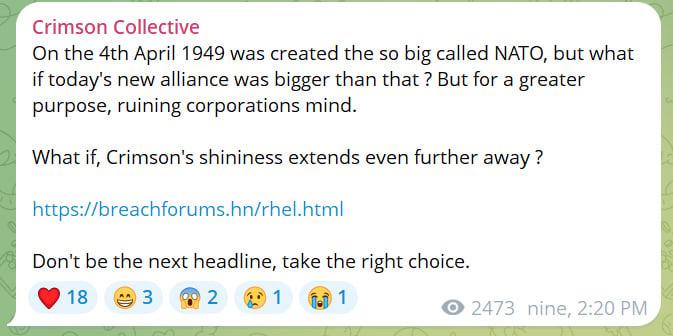
“On the 4th April 1949 was created the so huge referred to as NATO, however what if at present’s new alliance was larger than that ? However for a larger function, ruining companies thoughts,” reads a submit to the hacking group’s Telegram channel.
“What if, Crimson’s shininess extends even additional away ?”
Supply: BleepingComputer
“Concerning the present announcement concerning us, we’re going to collaborate with ShinyHunter’s for the long run assaults and releases,” the Crimson Collective risk actors advised BleepingComputer.
In coordination with the announcement, a Pink Hat entry has now appeared on a brand new ShinyHunters information leak extortion web site, warning the corporate that information can be publicly leaked on October tenth if a ransom demand was not negotiated with ShinyHunters.
As well as, the risk actors launched samples of the stolen CERs, together with these for Walmart, HSBC, Financial institution of Canada, Atos Group, American Categorical, Division of Defence, and Société Française du Radiotéléphone.
BleepingComputer contacted Pink Hat about this growth however didn’t obtain a response.
The ShinyHunters Extortion-as-a-Service
For months, BleepingComputer has speculated that ShinyHunters was performing as an extortion-as-a-service (EaaS), the place they work with risk actors to extort an organization in alternate for a share of the extortion demand, much like how ransomware-as-a-service gangs function.
This principle was primarily based on the quite a few assaults carried out by varied risk actors, all of which had been extorted underneath the ShinyHunters identify, together with these focusing on Oracle Cloud and PowerSchool.
Conversations with ShinyHunters additional supported this principle, because the group has beforehand claimed to not be behind a specific breach however fairly simply performing as a dealer of the stolen information.
Moreover, there have been quite a few arrests of people related to the identify “ShinyHunters” over time, together with these linked to the Snowflake information theft assaults, breaches at PowerSchool, and the operation of the Breached v2 hacking discussion board.
Nonetheless, even after these arrests, new assaults happen with firms receiving extortion emails stating, “We’re ShinyHunters”.
At present, ShinyHunters advised BleepingComputer that they’ve been privately working as an EaaS, the place they take a income share from any extortion funds generated for different risk actors’ assaults.
“Everybody i’ve labored with up to now have taken 70 or 75% and I obtain a 25-30%,” claimed the risk actor.
With the launch of the ShinyHunters information leak web site, it seems that the risk actor is now publicly working the extortion service.
Along with Pink Hat, ShinyHunters can also be extorting SP International on behalf of one other risk actor that claimed to breach the corporate in February 2025.
BleepingComputer had contacted SP International on the time in regards to the alleged breach, however was advised that the claims had been false and that the corporate was not breached.
Nonetheless, the risk actors have now launched samples of information on the information leak web site, claiming they had been stolen throughout the assault, and have additionally set an October tenth deadline.
After contacting SP International once more at present concerning its inclusion on the information leak web site, they determined to not touch upon the claims.
“We do not touch upon such claims. We word that as a US listed firm, we’re required to publicly disclose materials cybersecurity incidents,” SP International advised BleepingComputer.


