Intellexa’s Predator adware can conceal iOS recording indicators whereas secretly streaming digital camera and microphone feeds to its operators.
The malware doesn’t exploit any iOS vulnerability however leverages beforehand obtained kernel-level entry to hijack system indicators that might in any other case expose its surveillance operation.
Apple launched recording indicators on the standing bar in iOS 14 to alert customers when the digital camera or microphone is in use, displaying a inexperienced or an orange dot, respectively.
US-sanctioned surveillance agency Intellexa developed the Predator industrial adware and delivered it in assaults that exploited Apple and Chrome zero-day flaws and thru 0-click an infection mechanisms.
Whereas its skill to suppress digital camera and microphone exercise indicators is well-known, it was unclear how the mechanism labored.

Supply: Jamf
How Predator hides recording
Researchers at cellular gadget administration firm Jamf analyzed Predator samples and documented the method of hiding the privacy-related indicators.
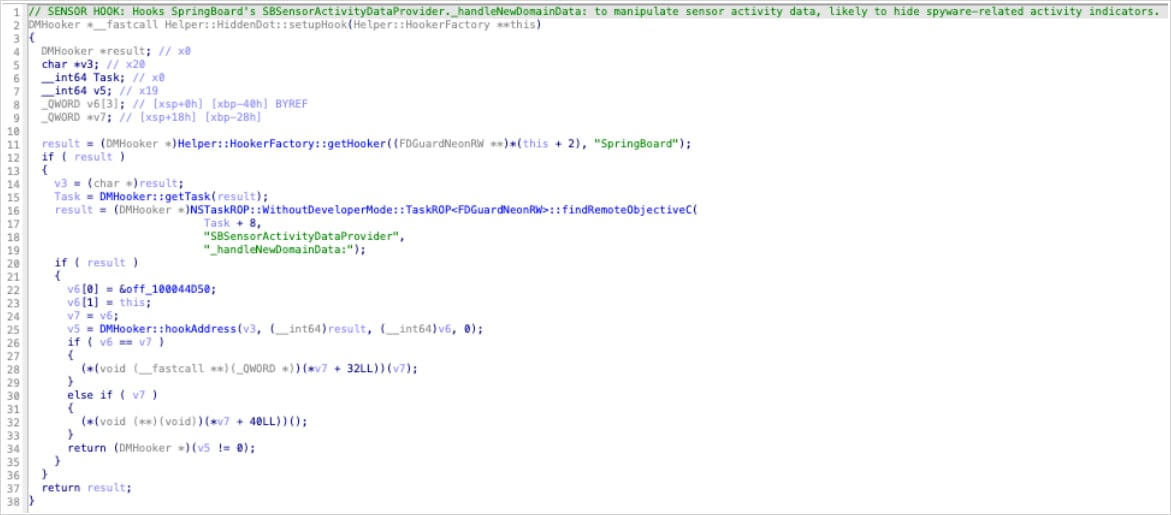
In accordance with Jamf, Predator hides all recording indicators on iOS 14 through the use of a single hook perform (‘HiddenDot::setupHook()’) inside SpringBoard, invoking the tactic every time sensor exercise modifications (upon digital camera or microphone activation).
By intercepting it, Predator prevents sensor exercise updates from ever reaching the UI layer, so the inexperienced or pink dot by no means lights up.
“The goal methodology _handleNewDomainData: known as by iOS every time sensor exercise modifications – digital camera activates, microphone prompts, and many others.,” Jamf researchers clarify.
“By hooking this single methodology, Predator intercepts ALL sensor standing updates earlier than they attain the indicator show system.”
Supply: Jamf
The hook works by nullifying the article answerable for sensor updates (SBSensorActivityDataProvider in SpringBoard). In Goal-C, calls to a null object are silently ignored, so SpringBoard by no means processes the digital camera or microphone activation, and no indicator seems.
As a result of SBSensorActivityDataProvider aggregates all sensor exercise, this single hook disables each the digital camera and the microphone indicators.
The researchers additionally discovered “lifeless code” that tried to hook ‘SBRecordingIndicatorManager’ instantly. Nevertheless, it doesn’t execute, and is probably going an earlier improvement path that was deserted in favor of the higher method that intercepts sensor information upstream.
Within the case of VoIP recordings, which Predator additionally helps, the module accountable lacks an indicator-suppression mechanism, so it depends on the HiddenDot perform for stealth.
Jamf additional explains that digital camera entry is enabled by way of a separate module that locates inside digital camera capabilities utilizing ARM64 instruction sample matching and Pointer Authentication Code (PAC) redirection to bypass digital camera permission checks.
With out indicators lighting up on the standing bar, the adware exercise stays utterly hidden to the common person.
Jamf notes that technical evaluation reveals the indicators of the malicious processes, corresponding to surprising reminiscence mappings or exception ports in SpringBoard and mediaserverd, breakpoint-based hooks, and audio information written by mediaserverd to uncommon paths.
BleepingComputer has contacted Apple with a request for a touch upon Jamf’s findings, however the firm by no means responded.
Trendy IT infrastructure strikes sooner than handbook workflows can deal with.
On this new Tines information, learn the way your staff can cut back hidden handbook delays, enhance reliability by way of automated response, and construct and scale clever workflows on prime of instruments you already use.



