Claims administration and threat administration firm Sedgwick has confirmed that its federal contractor subsidiary, Sedgwick Authorities Options, was the sufferer of a safety breach.
Sedgwick additionally employs over 33,000 individuals and serves 10,000 purchasers throughout 80 nations, together with 59% of the Fortune 500, and its subsidiary serves over 20+ authorities company purchasers.
The checklist of federal companies utilizing Sedgwick Authorities Options’s providers contains the Cybersecurity and Infrastructure Safety Company (CISA), the Division of Commerce, the USA Citizenship and Immigration Providers (USCIS), the USA Coast Guard, the Division of Homeland Safety (DHS), the U.S. Division of Labor, the Customs and Border Safety (CBP), and the U.S. Coast Guard.
A Sedgwick spokesperson instructed BleepingComputer that the corporate is presently investigating a safety breach that impacted its subsidiary, including that the dad or mum firm’s community was not affected.
Sedgwick has additionally notified regulation enforcement and has employed exterior cybersecurity consultants to research the impression of the breach.
“Sedgwick is addressing a safety incident at one in every of its subsidiaries, Sedgwick Authorities Options. Following the detection of the incident, we initiated our incident response protocols and engaged exterior cybersecurity consultants by way of exterior counsel to help with our investigation of the affected remoted file switch system,” the spokesperson mentioned.
“Importantly, Sedgwick Authorities Options is segmented from the remainder of our enterprise, and no wider Sedgwick methods or knowledge had been affected. Additional, there is no such thing as a proof of entry to claims administration servers nor any impression on Sedgwick Authorities Options capability to proceed serving its purchasers. Now we have notified regulation enforcement and stay in touch with our purchasers as we conduct our investigation.”
Whereas the corporate did not attribute the assault to a particular menace group, the assertion confirms the TridentLocker ransomware group’s claims that they breached the corporate.
The menace actors say they’ve stolen 3.39 GB of paperwork and, since taking accountability for the assault, they’ve additionally printed a few of the allegedly stolen knowledge on their Tor knowledge leak web site.
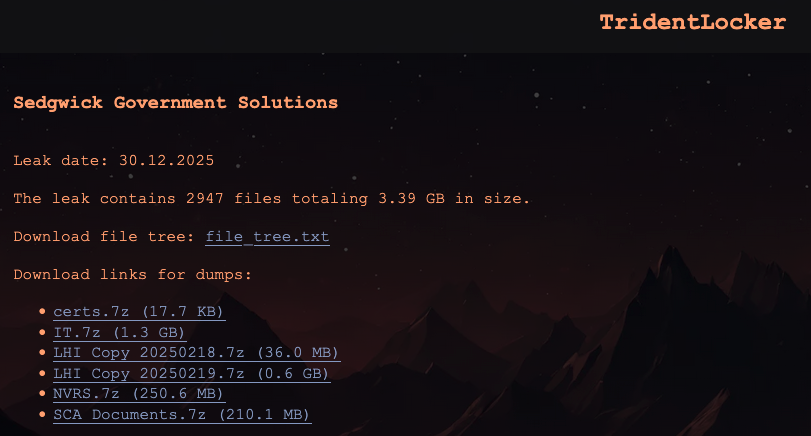
TridentLocker ransomware first surfaced in November and is presently itemizing a dozen victims on its leak website, together with Bpost (Belgian Submit Group), the corporate that delivers mail in Belgium and one of many largest civilian employers within the nation.
Bpost confirmed its community was breached on December third however mentioned its operations weren’t affected by the TridentLocker ransomware assault.



