A state-sponsored risk group has compromised dozens of networks of presidency and important infrastructure entities in 37 international locations in global-scale operations dubbed ‘Shadow Campaigns’.
Between November and December final yr, the actor additionally engaged in reconnaissance exercise focusing on authorities entities related to 155 international locations.
In line with Palo Alto Networks’ Unit 42 division, the group has been energetic since a minimum of January 2024, and there’s excessive confidence that it operates from Asia. Till definitive attribution is feasible, the researchers observe the actor as TGR-STA-1030/UNC6619.
‘Shadow Campaigns’ exercise focuses totally on authorities ministries, legislation enforcement, border management, finance, commerce, vitality, mining, immigration, and diplomatic companies.
Unit 42 researchers confirmed that the assaults efficiently compromised a minimum of 70 authorities and important infrastructure organizations throughout 37 international locations.
This contains organizations engaged in commerce coverage, geopolitical points, and elections within the Americas; ministries and parliaments throughout a number of European states; the Treasury Division in Australia; and authorities and important infrastructure in Taiwan.

Supply: Unit 42
The record of nations with focused or compromised organizations is intensive and centered on sure areas with explicit timing that seems to have been pushed by particular occasions.
The researchers say that through the U.S. authorities shutdown in October 2025, the risk actor confirmed elevated curiosity in scanning entities throughout North, Central and South America (Brazil, Canada, Dominican Republic, Guatemala, Honduras, Jamaica, Mexico, Panama, and Trinidad and Tobago).
Important reconnaissance exercise was found towards “a minimum of 200 IP addresses internet hosting Authorities of Honduras infrastructure” simply 30 days earlier than the nationwide election, as each candidates indicated willingness to revive diplomatic ties with Taiwan.
Unit 42 assesses that the risk group compromised the next entities:
- Brazil’s Ministry of Mines and Vitality
- the community of a Bolivian entity related to mining
- two of Mexico’s ministries
- a authorities infrastructure in Panama
- an IP tackle that geolocates to a Venezolana de Industria Tecnológica facility
- compromised authorities entities in Cyprus, Czechia, Germany, Greece, Italy, Poland, Portugal, and Serbia
- an Indonesian airline
- a number of Malaysian authorities departments and ministries
- a Mongolian legislation enforcement entity
- a significant provider in Taiwan’s energy tools trade
- a Thai authorities division (seemingly for financial and worldwide commerce info)
- vital infrastructure entities within the Democratic Republic of the Congo, Djibouti, Ethiopia, Namibia, Niger, Nigeria, and Zambia
Unit 42 additionally believes that TGR-STA-1030/UNC6619 additionally tried to attach over SSH to infrastructure related to Australia’s Treasury Division, Afghanistan’s Ministry of Finance, and Nepal’s Workplace of the Prime Minister and Council of Ministers.
Other than these compromises, the researchers discovered proof indicating reconnaissance exercise and breach makes an attempt focusing on organizations in different international locations.
They are saying that the actor scanned infrastructure related to the Czech authorities (Military, Police, Parliament, Ministries of Inside, Finance, Overseas Affairs, and the president’s web site).
The risk group additionally tried to connect with the European Union infrastructure by focusing on greater than 600 IP internet hosting *.europa.eu domains. In July 2025, the group centered on Germany and initiated connections to greater than 490 IP addresses that hosted authorities methods.
Shadow Campaigns assault chain
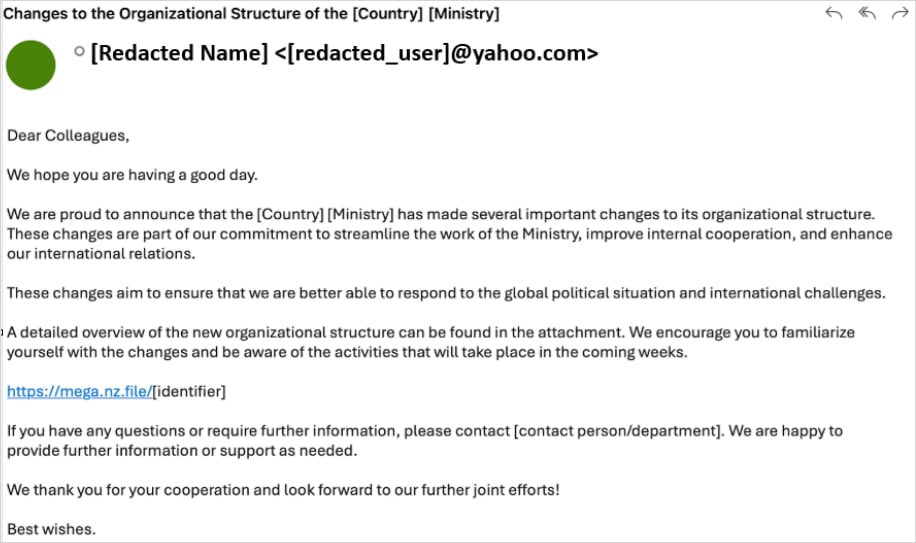
Early operations relied on extremely tailor-made phishing emails despatched to authorities officers, with lures generally referencing inside ministry reorganization efforts.
The emails embedded hyperlinks to malicious archives with localized naming hosted on the Mega.nz storage service. The compressed recordsdata contained a malware loader known as Diaoyu and a zero-byte PNG file named pic1.png.
Supply: Unit 42
Unit 42 researcher discovered that the Diaoyu loader would fetch Cobalt Strike payloads and the VShell framework for command-and-control (C2) underneath sure situations that equate to evaluation evasion checks.
“Past the {hardware} requirement of a horizontal display screen decision higher than or equal to 1440, the pattern performs an environmental dependency test for a selected file (pic1.png) in its execution listing,” the researchers say.
They clarify that the zero-byte picture acts as a file-based integrity test. In its absence, the malware terminates earlier than inspecting the compromised host.
To evade detection, the loader appears for working processes from the next safety merchandise: Kaspersky, Avira, Bitdefender, Sentinel One, and Norton (Symantec).
Other than phishing, TGR-STA-1030/UNC6619 additionally exploited a minimum of 15 recognized vulnerabilities to attain preliminary entry. Unit 42 discovered that the risk actor leveraged safety points in SAP Answer Supervisor, Microsoft Alternate Server, D-Hyperlink, and Microsoft Home windows.
New Linux rootkit
TGR-STA-1030/UNC6619’s toolkit used for Shadow Campaigns exercise is intensive and contains webshells equivalent to Behinder, Godzilla, and Neo-reGeorg, in addition to community tunneling instruments equivalent to GO Easy Tunnel (GOST), Quick Reverse Proxy Server (FRPS), and IOX.
Nonetheless, researchers additionally found a customized Linux kernel eBPF rootkit known as ‘ShadowGuard’ that they consider to be distinctive to the TGR-STA-1030/UNC6619 risk actor.
“eBPF backdoors are notoriously troublesome to detect as a result of they function totally throughout the extremely trusted kernel area,” the researchers clarify.
“This permits them to govern core system capabilities and audit logs earlier than safety instruments or system monitoring functions can see the true information.”
ShadowGuard conceals malicious course of info on the kernel degree, hides as much as 32 PIDs from commonplace Linux monitoring instruments utilizing syscall interception. It might probably additionally cover from guide inspection recordsdata and directories named swsecret.
Moreover, the malware incorporates a mechanism that lets its operator outline processes that ought to stay seen.
The infrastructure utilized in Shadow Campaigns depends on victim-facing servers with respectable VPS suppliers within the U.S., Singapore, and the UK, in addition to relay servers for visitors obfuscation, and residential proxies or Tor for proxying.
The researchers seen using C2 domains that would seem acquainted to the goal, equivalent to using .gouv top-level extension for French-speaking international locations or the dog3rj[.]tech area in assaults within the European area.
“It’s doable that the area identify may very well be a reference to ‘DOGE Jr,’ which has a number of meanings in a Western context, such because the U.S. Division of Authorities Effectivity or the identify of a cryptocurrency,” the researchers clarify.
In line with Unit 42, TGR-STA-1030/UNC6619 represents an operationally mature espionage actor who prioritizes strategic, financial, and political intelligence and has already impacted dozens of governments worldwide.
Unit 42’s report contains indicators of compromise (IoCs) on the backside of the report to assist defenders detect and block these assaults.



