Varonis Risk Labs is shining a highlight on a decade-old vulnerability that opens the door to URL spoofing.
By exploiting how browsers deal with Proper-to-Left (RTL) and Left-to-Proper (LTR) scripts, attackers can craft URLs that seem reliable however truly lead some place else, subsequently this methodology, often called BiDi Swap, will be usually abused in phishing assaults.
Previous Unicode assaults and spoofing
Earlier than BiDi Swap, a number of Unicode-based tips have been used to idiot each customers and browsers into displaying misleading textual content or URLs. Two standout examples are:
- Punycode Homograph Assaults: Internationalized Area Names (IDNs) let web sites use non-Latin characters (e.g., Russian “а,” Cyrillic “с,” or Greek “ο”) that look almost an identical to well-known Latin letters. This will create spoofed domains like “аpple.com” or “рayрal.com” with solely minor character variations. Browsers convert these for constant dealing with (e.g., “xn--something”), however attackers usually sneak in visually an identical characters, tricking individuals into believing they’re on a legit web site.
- RTL Override Exploits: Some attackers embed particular Unicode characters (e.g., U+202E) that flip textual content path mid-string. This will disguise URL paths, make file extensions look innocent, or reorder textual content to cover malicious file endings like: “blafdp.exe” -> “blaexe.pdf”
Whereas these management characters are essential for dealing with right-to-left languages correctly, they’ll additionally masks harmful content material or rearrange the structure, so a web site or file title seems protected at a fast look.
These previous assaults set the stage for BiDi Swap by revealing how tiny nuances in textual content dealing with can have massive safety penalties and the way ongoing vigilance is required to stop these spoofing tips.
LTR, RTL and BiDi who?
In the case of textual content path, many languages, like English or Spanish, circulate left to proper (LTR), whereas others, reminiscent of Arabic or Hebrew, go proper to left (RTL). This combine is usually a problem for computer systems, which have to hold every part aligned so textual content doesn’t grow to be a scrambled mess.
That’s the place the Bidirectional (Bidi) Algorithm steps in.
A part of the Unicode Normal, Bidi helps computer systems accurately show LTR and RTL scripts in the identical textual content.
Nevertheless, whereas the Bidi Algorithm normally handles domains decently, it struggles with subdomains and URL parameters. This hole means combined LTR–RTL URLs won’t show as meant, creating an open door for mischief.
Our crew analyzed knowledge from 1,000 real-world IT environments and located that no group was breach-proof.
In truth, 99% of organizations have uncovered delicate knowledge that may simply be surfaced by AI.
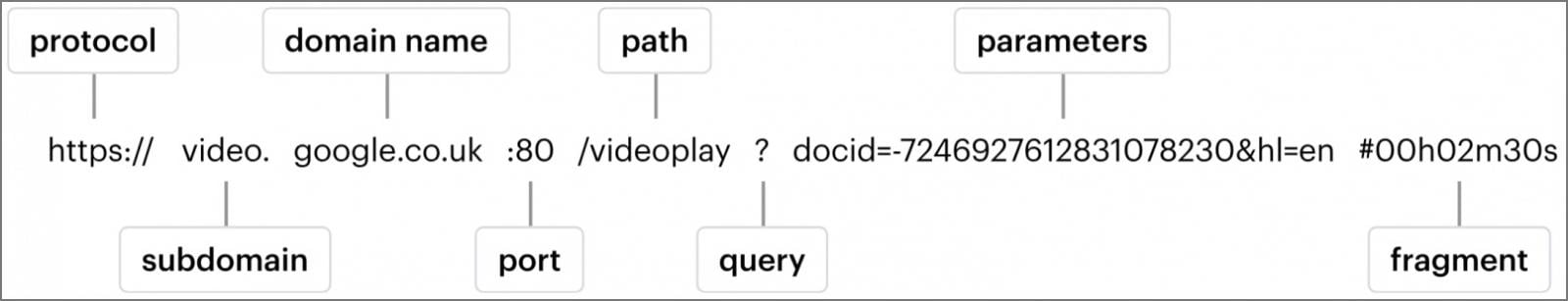
URL construction
Right here’s a fast refresher on what a URL is and the way it’s structured: A URL (Uniform Useful resource Locator) is a standardized option to level to assets on the net, and it usually comprises a number of key elements:
- Protocol (Scheme): This defines how the useful resource is accessed, for instance “http://” or “https://.”
- Subdomain: An elective half earlier than the principle area (e.g., “www.” in “www.instance.com”), which might set up content material inside bigger websites
- Area: The core a part of the tackle (e.g., “instance”)
- Prime-Degree Area (TLD): The ending of the area title (e.g., “.com,” “.org,” “.internet”) that usually signifies the aim or geographical location
- Path: The listing or file construction that seems after the area (e.g., “/weblog/posts”)
- Question String/Parameters: Key-value pairs used to cross additional data to the server, normally beginning with a query mark (e.g., “?id=123”)
Bidi swap
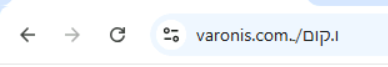
Let’s begin with one thing easy: a daily right-to-left (RTL) host (area + TLD) would possibly appear to be this (Sure, we acquired a one-letter host):
Now, let’s add a protocol and blend in each RTL and LTR parameters:
Discover how inserting parameters on the fitting rapidly turns into complicated. Subsequent, let’s strive including an English parameter that appears like one other area title:
That also doesn’t yield the anticipated conduct. Now, let’s see what occurs once we attempt to mimic a subdomain:
Combining an LTR subdomain with some RTL parameters:
Extra payloads
Strive it your self: Change the varonis subdomain to any area you want and watch the magic occur!
Disclaimer: This web site is offered as-is and is meant solely for instructional and informational functions. It demonstrates a proof-of-concept associated to browser conduct and potential misuse. The consumer assumes full accountability for any use of the code or methods offered herein, together with any penalties which will come up. The authors and maintainers of this web site don’t endorse or encourage misuse, and no legal responsibility is accepted for any actions taken based mostly on this content material.
Browser mitigations
Chrome
Bidi Swap has been a identified difficulty in Chrome for over a decade. Whereas Chrome’s “Navigation suggestion for lookalike URLs” function gives partial safety, our testing reveals it solely flags sure domains (e.g., “google.com”), letting many others fly underneath the radar.
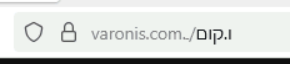
Firefox
Firefox has additionally acknowledged this as a longstanding difficulty. Nevertheless, moderately than counting on recommendations for lookalike URLs, Firefox takes a distinct UI strategy. By highlighting key elements of the area within the tackle bar, Firefox makes it simpler for customers to identify potential spoofs or suspicious hyperlinks.
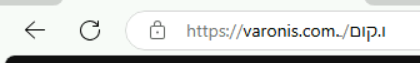
Edge
We knowledgeable Microsoft and so they marked the problem as resolved, however the URL illustration appears to stay unchanged.
ARC
Arc is not developed, however right here is an instance of a browser that did it proper:
Conclusion and proposals
To fight BiDi Swap, observe these suggestions:
- Consciousness is vital: All the time confirm suspicious URLs — particularly those who combine scripts or present sudden patterns
- Push for enchancment: Browser builders ought to refine current protections like area highlighting and lookalike detection to shut these safety gaps
- Educate customers and groups: Encourage everybody to hover over hyperlinks, affirm SSL certificates, and test area consistency. A couple of additional seconds can thwart a significant safety threat.
Uncover extra from the Varonis Risk Labs crew on our weblog.
Finish-to-end strategy to cease breaches
By providing Varonis Interceptor’s unmatched risk detection with the Varonis Knowledge Safety Platform and MDDR service, we’re rushing up our means to cease knowledge breach makes an attempt earlier within the assault chain.
Varonis integrates straight with e-mail companies like Microsoft Alternate On-line to categorise inbound and outbound visitors containing delicate data, remediate posture points on uncovered mailboxes, and monitor anomalous e-mail visitors for insider dangers utilizing industry-leading conduct analytics.
The addition of Varonis Interceptor represents a major development in end-to-end e-mail and browser safety. By harnessing the facility of multimodal AI, it extra successfully identifies and mitigates phishing threats than present options out there. Varonis Interceptor permits companies to confidently shield their inboxes and, subsequently, the delicate knowledge of their digital property.
Wish to see what Interceptor can do quicker? Request a demo at this time.
Sponsored and written by Varonis.

