VirusTotal has found a phishing marketing campaign hidden in SVG information that create convincing portals impersonating Colombia’s judicial system that ship malware.
VirusTotal detected this marketing campaign after it added help for SVGs to its AI Code Perception platform.
VirusTotal’s AI Code Perception characteristic analyzes uploaded file samples utilizing machine studying to generate summaries of suspicious or malicious conduct discovered within the information.
After including help for SVGs, VirusTotal discovered an SVG file that had zero detections by antivirus scans, however whose AI-powered Code Perception characteristic detected utilizing JavaScript to show HTML, impersonating a portal for Colombia’s authorities judiciary system.
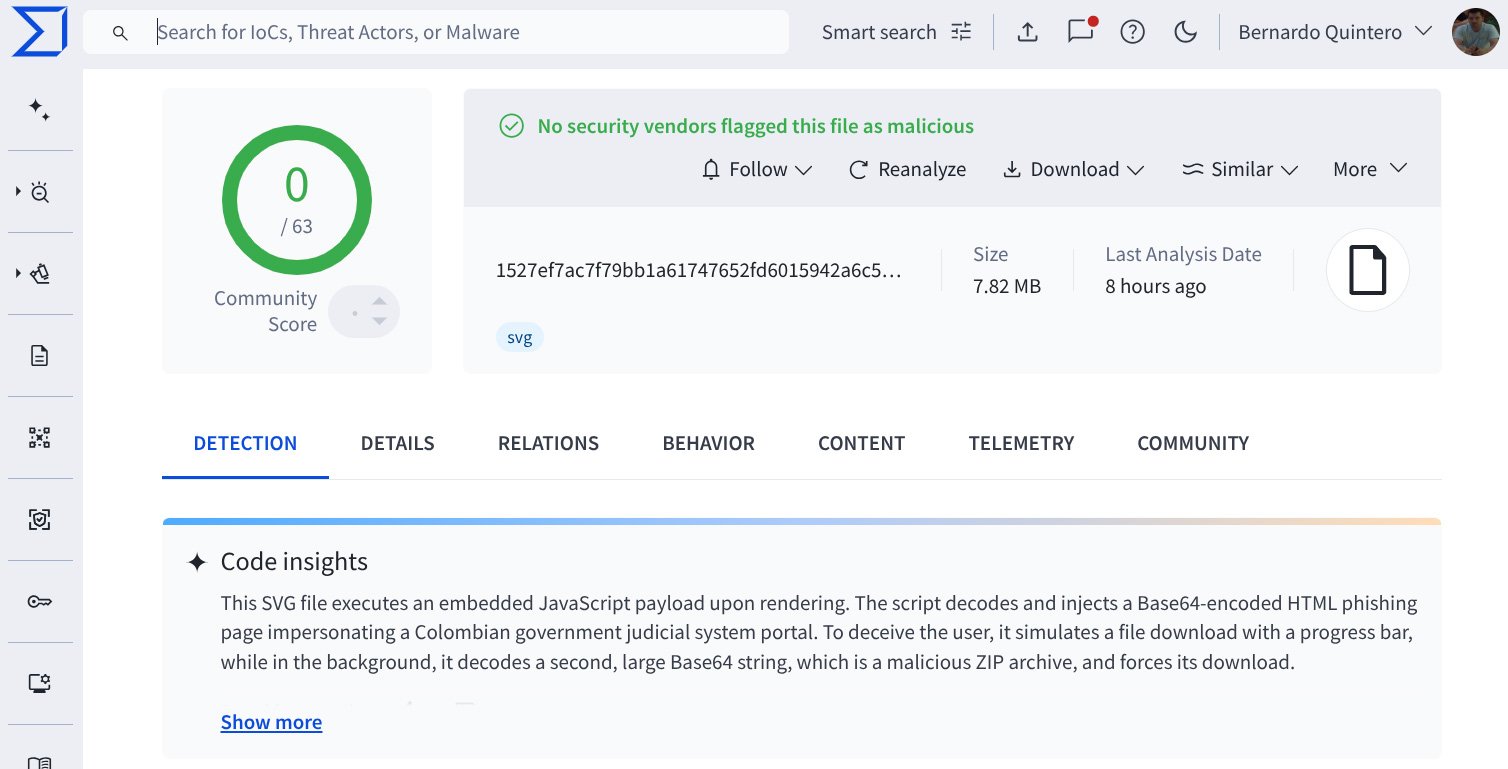
Supply: VirusTotal
SVG, or Scalable Vector Graphics, is used to generate photographs of traces, shapes, and textual content via textual mathematical formulation within the file.
Nevertheless, risk actors have begun more and more utilizing SVG information in assaults, as they will also be used to show HTML utilizing the
Within the marketing campaign found by Virustotal, SVG picture information are used to render pretend portals that show a phony obtain progress bar, in the end prompting the consumer to obtain a password-protected zip archive [VirusTotal]. The password for this file is displayed within the pretend portal web page.
“As proven within the screenshots under, the pretend portal is rendered precisely as described, simulating an official authorities doc obtain course of,” explains VirusTotal.
“The phishing web site contains case numbers, safety tokens, and visible cues to construct belief, all of it crafted inside an SVG file.”
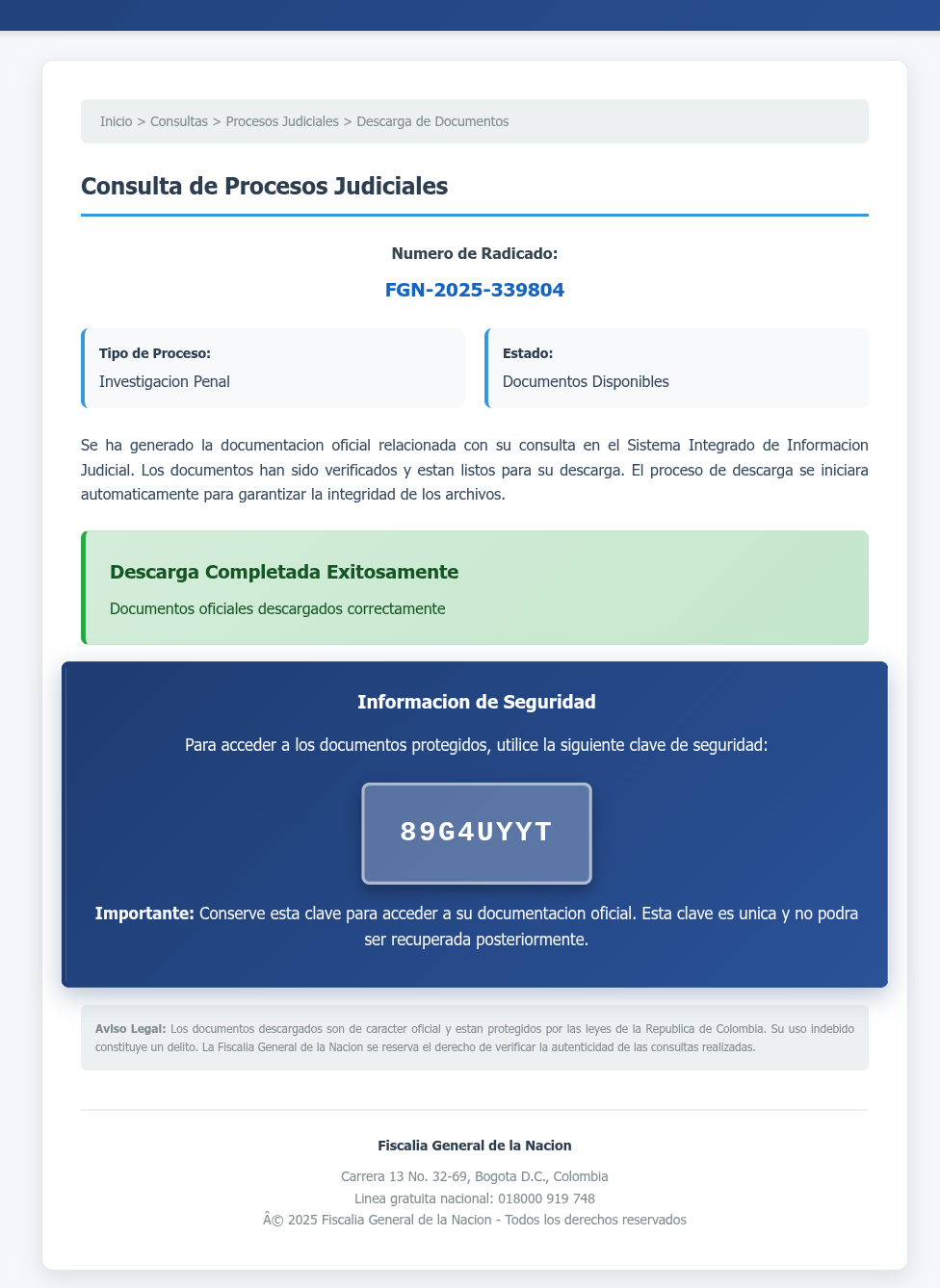
Supply: VirusTotal
BleepingComputer discovered that the extracted file comprises 4 information: a reliable executable from the Comodo Dragon net browser, renamed to be an official judicial doc, a malicious DLL [VirusTotal], and what seems to be two encrypted information.
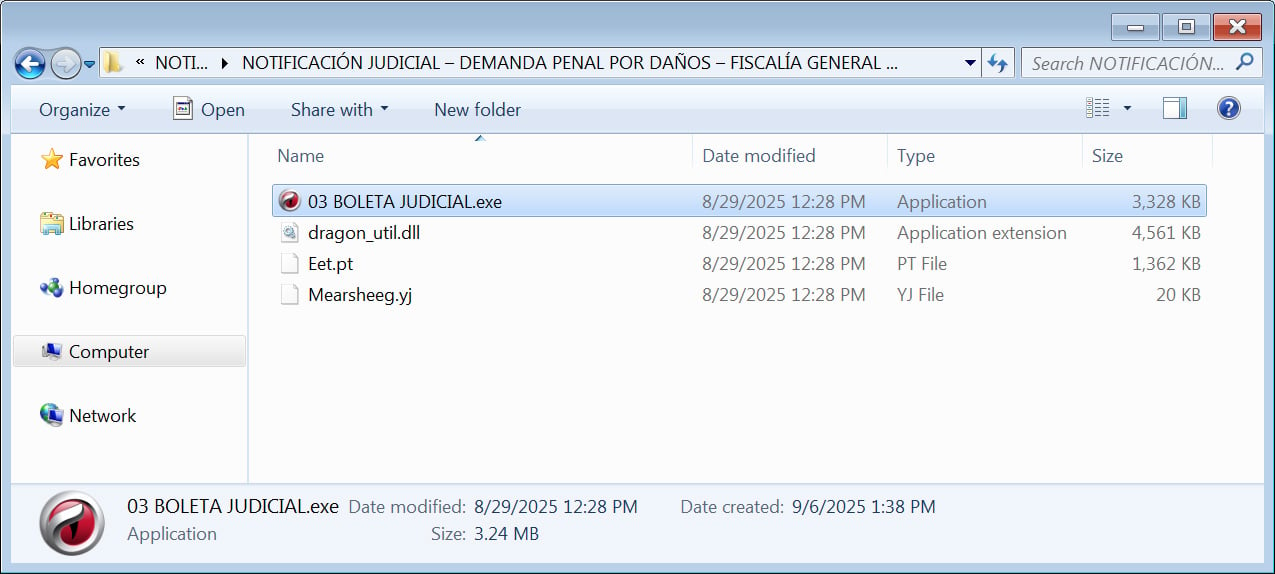
Supply: BleepingComputer
If the consumer opens the executable, the malicious DLL shall be sideloaded to put in additional malware on the system.
After detecting this preliminary SVG, VirusTotal recognized 523 beforehand uploaded SVG information that had been a part of the identical marketing campaign however had evaded detection by safety software program.
The addition of SVG help to AI Code Insights was essential in exposing this specific marketing campaign, as VirusTotal famous that using AI makes it simpler to establish new malicious campaigns.
“That is the place Code Perception helps most: giving context, saving time, and serving to give attention to what actually issues. It is not magic, and it will not exchange knowledgeable evaluation, nevertheless it’s yet one more software to chop via the noise and get to the purpose sooner,” concludes VirusTotal.


