Amazon SageMaker Unified Studio now gives two area configurations: Amazon SageMaker Unified Studio Id Middle(IDC)-based domains with complete governance options, and Amazon SageMaker Unified Studio IAM-based domains with enhanced developer productiveness instruments.
On this put up, we display how you should utilize each of those area configurations of Amazon SageMaker Unified Studio utilizing AWS Id and Entry Administration (IAM) position reuse and attribute-based entry management.
How authentication works in every configuration
Amazon SageMaker Unified Studio IDC-based domains authenticate customers by way of AWS Id and Entry Administration (IAM) Id Middle with Single Signal-On, preserving particular person consumer identities all through their classes. These domains excel in governance with identity-based authorization, fine-grained entry controls between customers, and complete catalog administration that includes formal Writer/Subscriber (Pub/Sub) information sharing workflows with approval processes—supreme for enterprise environments requiring robust identification administration, compliance monitoring, and identity-based audit trails.
Amazon SageMaker Unified Studio IAM-based domains authenticate by way of federated AWS Id and Entry Administration (IAM) roles the place all customers accessing a undertaking share the identical position permissions. These domains prioritize developer productiveness with trendy instruments together with new serverless Notebooks, Athena Spark integration, the improved interface with vertical navigation, and built-in AI help, designed for improvement groups that want streamlined entry and superior analytics capabilities.
This answer facilitates organizations which might be already utilizing IDC-based domains to protect their present governance frameworks established in IDC-based domains whereas unlocking trendy improvement capabilities for his or her groups by way of IAM-based domains. If you happen to favor to make use of the newly launched IAM-based domains, you may proceed to do as nicely. The selection will depend on your organization’s wants.
Please word that on the time of penning this weblog, IAM-based domains don’t assist Trusted identification propagation. This answer makes use of the undertaking execution position to configure information entry.
The problem
Think about a information steward (Sam) makes use of the IDC-based area to outline information entry insurance policies, handle the info catalog, and approve subscription requests to confirm compliance and correct information governance.
However, a information engineer (Sarah), needs to make use of IDC-based area for governance options reminiscent of SageMaker catalog and IAM-based area for the brand new serverless Pocket book to construct information pipelines, carry out superior analytics, and speed up improvement cycles. Sarah will request entry to the info by way of IDC-based area, and as soon as entry is authorized by Sam, Sarah can entry this information in serverless pocket book obtainable in IAM-based area.
Answer overview
The combination leverages IAM position reuse, AWS Lake Formation Attribute-Based mostly Entry Management (ABAC) and Amazon SageMaker Catalog pub-sub mannequin to routinely carry permissions from the IDC-based area to the brand new IAM-based area. When correctly configured, information subscriptions managed by way of the IDC-based area’s Pub/Sub mannequin develop into instantly accessible in IAM-based area tasks, offering a unified information entry expertise.
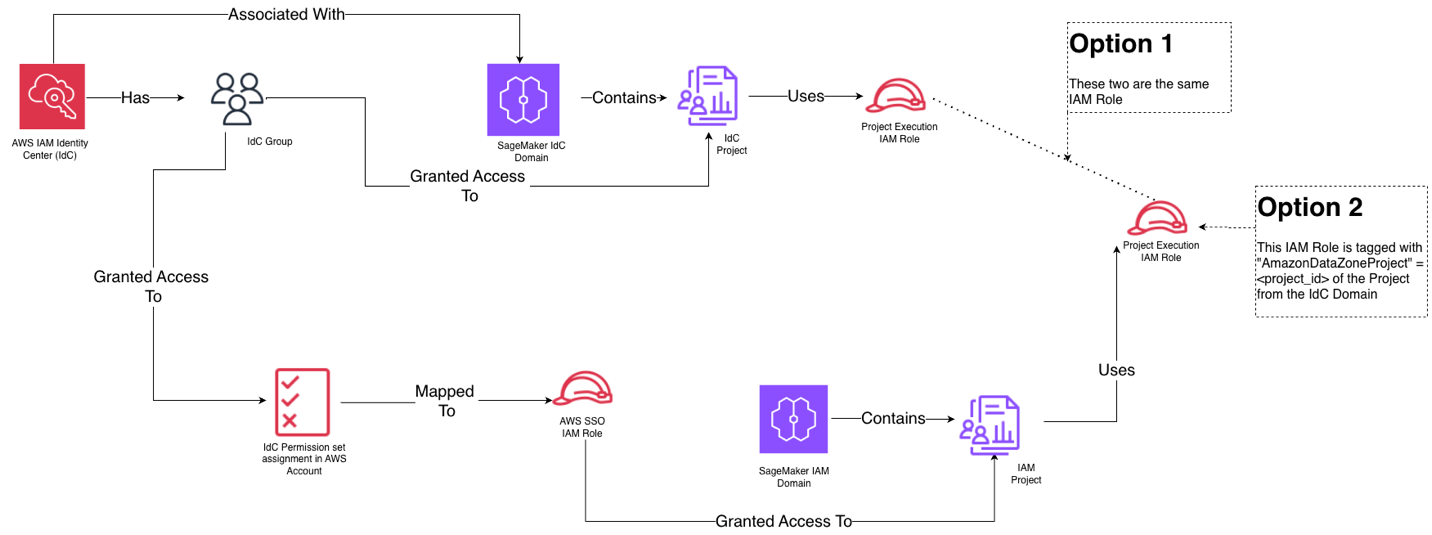
The answer we are going to implement within the put up entails creating an IAM-based area undertaking that’s just like your IDC client undertaking (eg identical group members, use case) , configuring execution roles, and enabling position reuse. This method maintains the acquainted subscription workflow whereas extending advantages to the IAM-based area.The next diagram exhibits the high-level structure of how this method works.
The answer structure consists of:
- Current IDC-based area: Incorporates producer and client tasks with established information sharing by way of Pub/Sub mannequin
- IAM-based area: New tasks with federated and execution roles configured for contemporary improvement instruments
- IAM Id Middle: Manages federated entry and permission units
- Attribute-Based mostly Entry Management: Tags on execution roles allow automated permission inheritance
The answer gives 2 choices: Possibility 1: IDC-Based mostly Area undertaking position reuse gives the only integration path by straight reusing the prevailing client undertaking IAM position out of your IDC-based area because the execution position within the IAM-based area. The first advantages embrace simplified setup requiring solely coverage adjustments (lined later within the weblog), lowered administrative overhead with one much less position to handle and decrease danger of misconfiguration because you’re leveraging confirmed, present roles. Select Possibility 1 while you need the quickest implementation path, your group prefers minimal position proliferation, you’ve well-established IDC-based area roles that have already got information entry permissions, or your group has restricted IAM experience and desires to keep away from advanced tagging configurations.
Possibility 2: Creating a brand new execution position for the IAM-based area undertaking and use attribute-based entry management (ABAC) by way of tagging with the IDC-based area undertaking ID. The important thing advantages embrace enhanced auditability with two distinct roles (one for IDC-based area, one for IAM-based area), clear separation exhibiting which area generated every request in CloudTrail logs, larger flexibility to customise permissions particular to IAM-based area wants with out affecting IDC-based area operations, and higher safety isolation between the 2 area varieties. The `AmazonDatazoneProject` tag permits attribute based mostly entry management, whereas sustaining distinct position identities. Select Possibility 2 when: your group requires detailed audit trails distinguishing between area varieties, compliance insurance policies mandate separation of considerations between governance and improvement environments, you wish to observe and attribute prices individually for every area, or it’s essential present proof exhibiting which area (governance vs. improvement) accessed particular information sources for compliance reporting.
Right here is the high-level view of how the identification and area entities map to one another for each choices:
Stipulations
To comply with together with this put up, you need to have:
For this demonstration, we use a simplified setup with a gross sales producer undertaking and a advertising client undertaking that subscribes to those tables.
Understanding the present IDC-based area setup
Our place to begin features a well-established Amazon SageMaker Unified Studio IDC-based area construction:
Gross sales Producer Undertaking
- Incorporates a database with pipeline and gross sales tables
- Managed by Sam, the info steward who creates and publishes information belongings
- Has its personal undertaking IAM position
Advertising Client Undertaking
- Managed by Sarah, the info engineer who subscribes to revealed information by way of IDC area undertaking
- Has its personal undertaking IAM position
- Efficiently queries subscribed information by way of the IDC-based area interface
Every undertaking has an related IAM position that governs entry to information belongings, and the Pub/Sub mannequin manages subscription workflows and permissions.
Organising federated position by way of permission units
Federated roles by way of permission units are used to authenticate and supply customers with console entry to IAM-based domains by way of AWS IAM Id Middle, the place all customers inside a undertaking share the identical position permissions. While you assign a permission set, IAM Id Middle creates corresponding IAM Id Middle-controlled IAM position in AWS account, and attaches the insurance policies specified within the permission set to that position.
IAM-based SMUS domains allow streamlined entry to trendy improvement instruments (serverless Notebooks, Athena Spark, AI help) whereas sustaining governance, routinely propagating permissions throughout domains with out requiring duplicate entry approvals, and simplifying group member onboarding.You need to use any IAM position to entry IAM-based area. For this put up, we are going to use federated position choice utilizing AWS IAM Id Middle (IDC).
Grant entry to Information engineer group for IAM-based domains in Id Middle
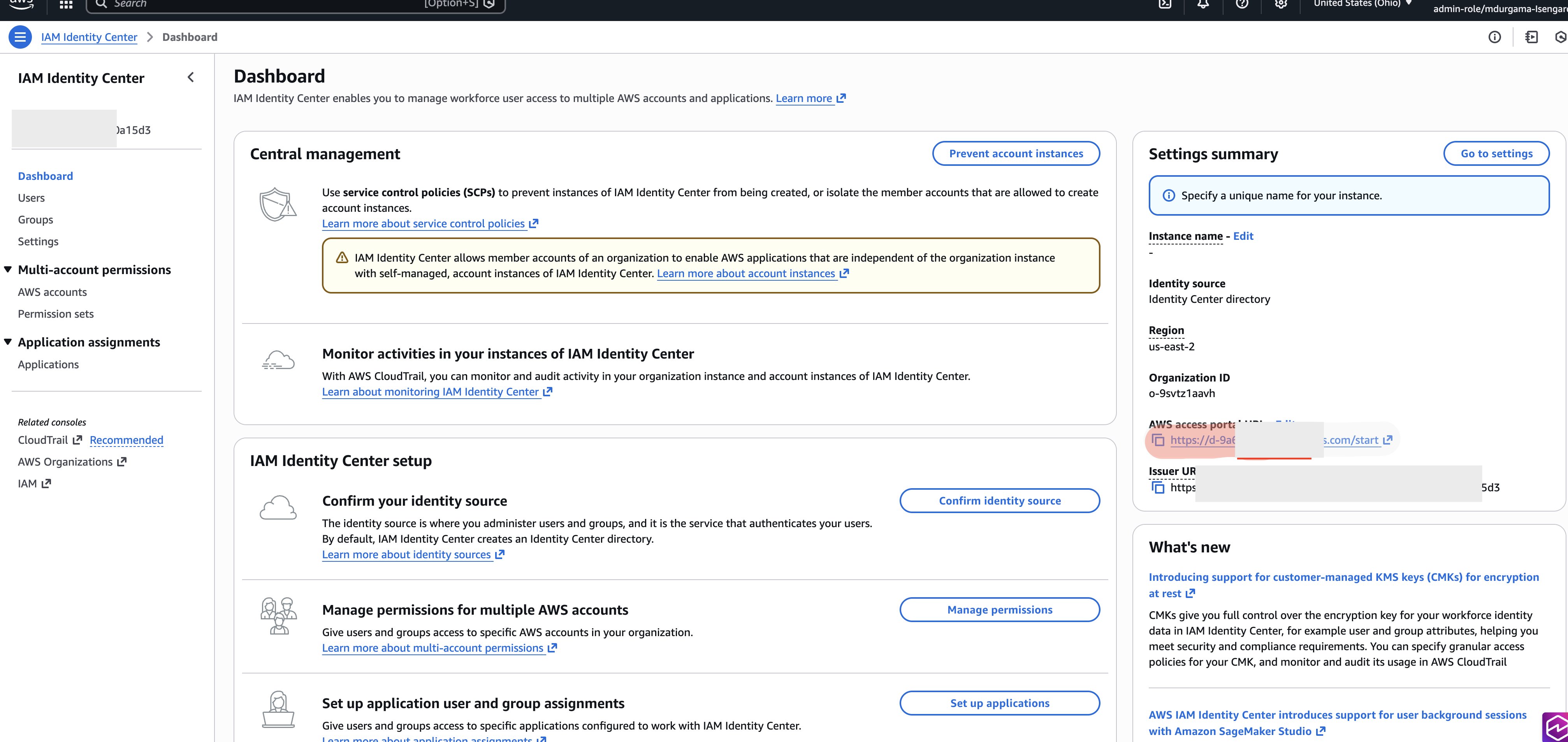
1) Arrange federated position in AWS IAM Id Middle
Navigate to IAM Id Middle (IDC) within the AWS Administration Console, then full the next steps:
- Go to permission set part in IDC. Create a brand new permission set known as
Advertising-federated-roleand choose Connect Coverage.
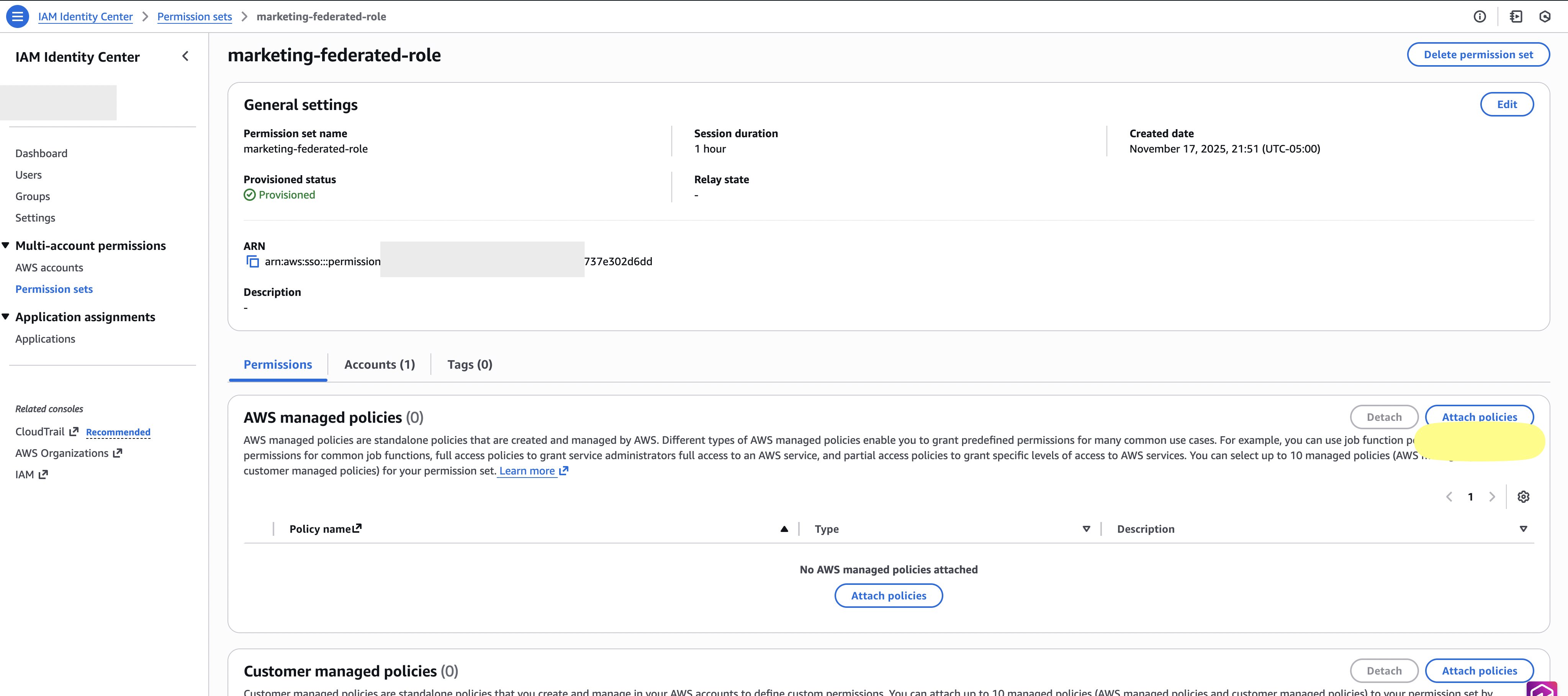
- Seek for SageMakerStudioUserIAMConsolePolicy within the present coverage identify from checklist and choose
SageMakerStudioUserIAMConsolePolicyfrom the checklist. Notice that the managed coverageSageMakerStudioUserIAMConsolePolicyhave to be hooked up or have the identical permissions added by way of one other coverage to have the ability to entry tasks in a SageMaker IAM area.
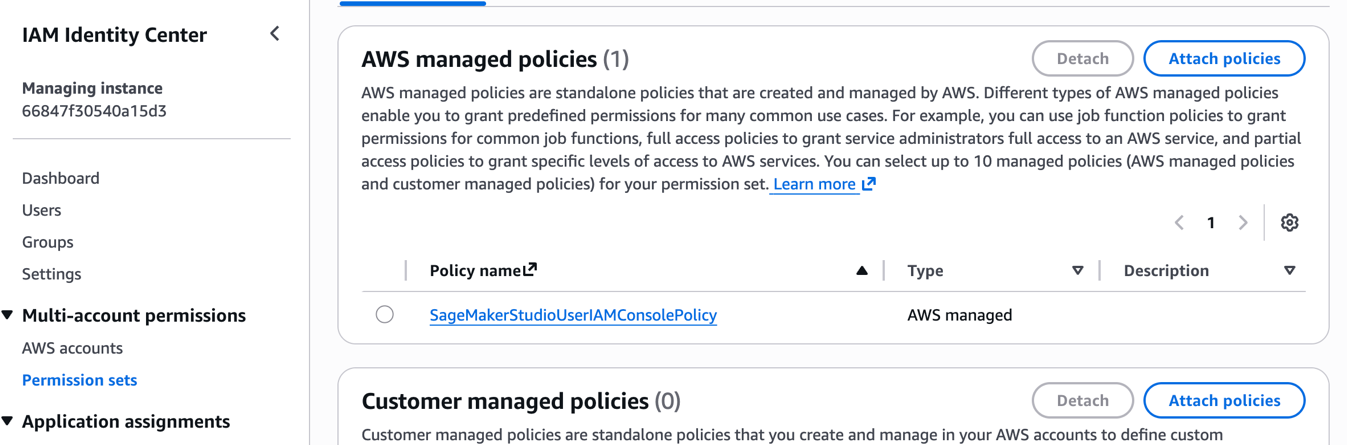
- Go to the AWS account part of IDC.
- Assign the created permission set to your AWS account.
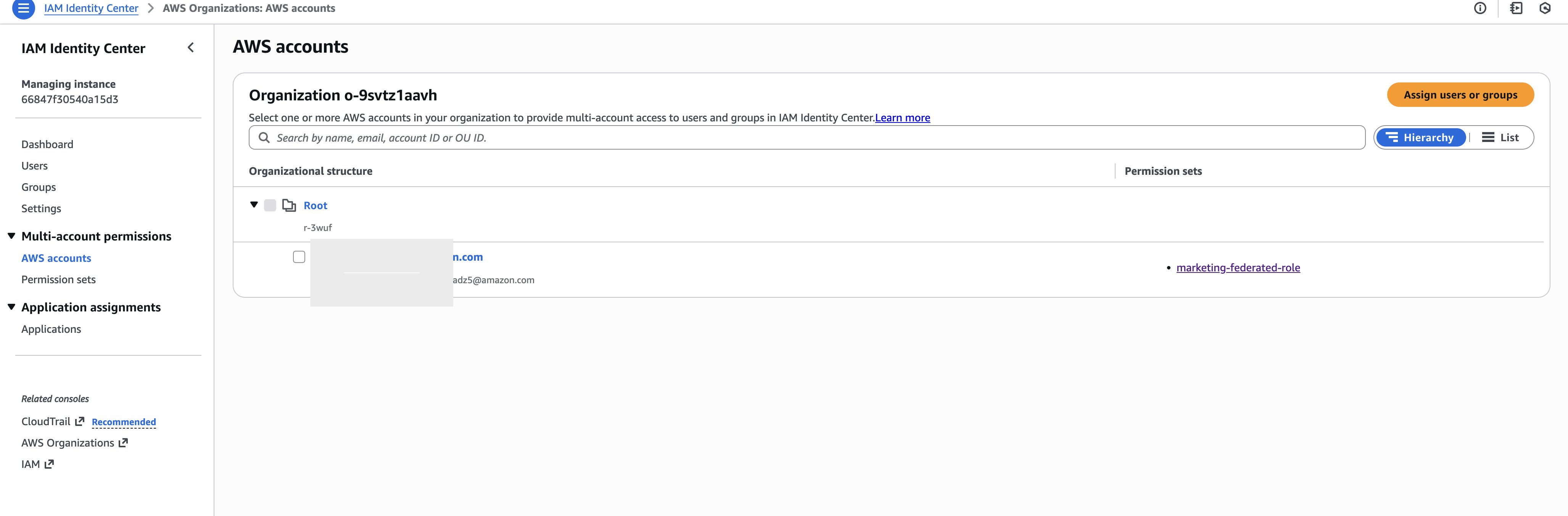
- For this put up we assigned the permission set to advertising group, As a greatest observe, you need to setup and grant entry to teams moderately than particular person customers.
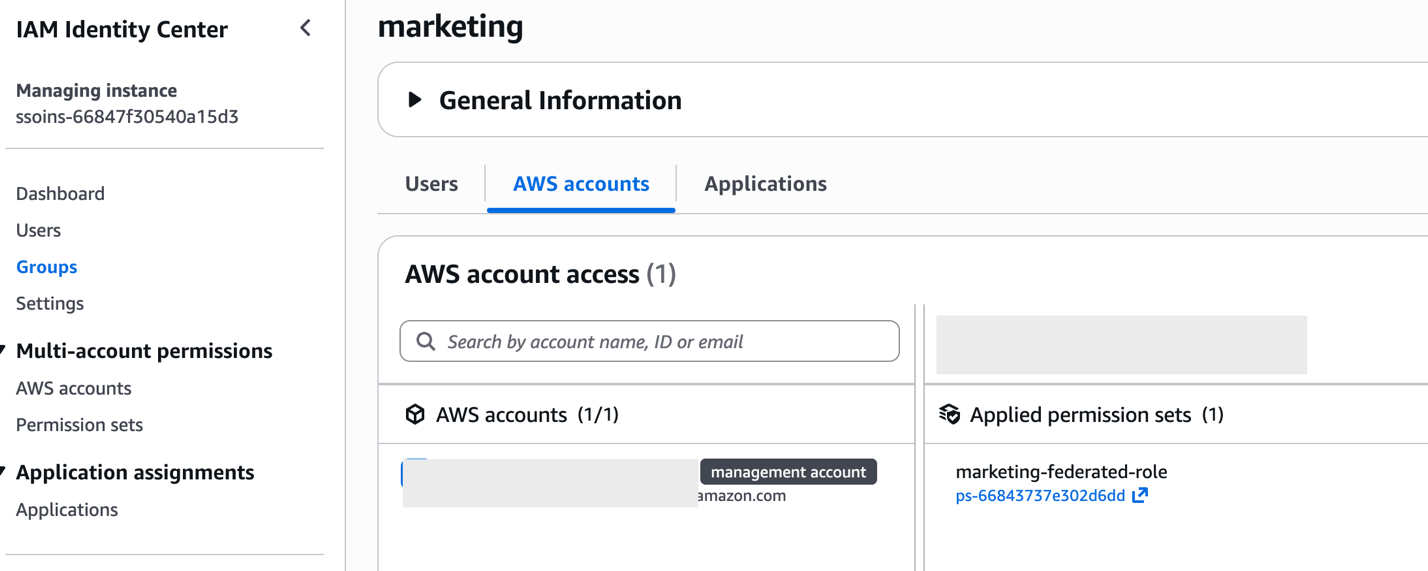
- Add Sarah to advertising group.
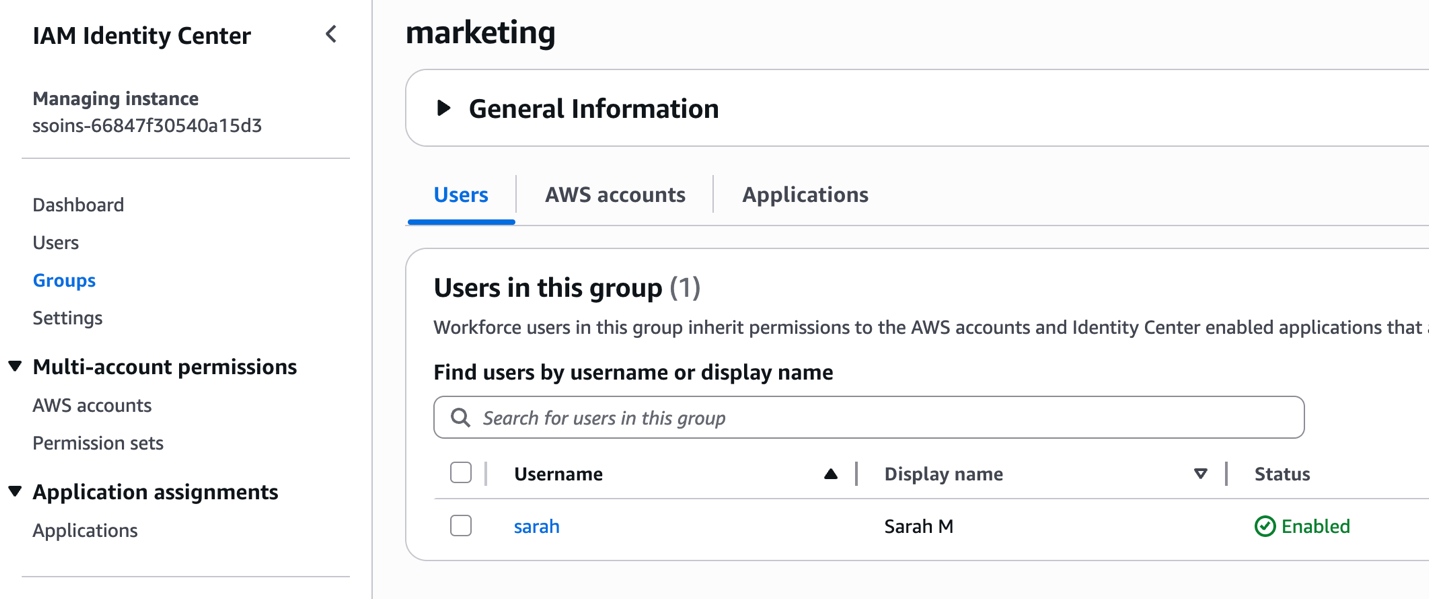
This creates a federated position that Sarah can use to entry the IAM-based area. The federated position seems as an IAM position inside your account and serves because the entry level for console entry.
Organising IAM-based area execution position
There are 2 choices to setup execution position for IAM-based area undertaking. The execution position has a one-to-one mapping with the federated position.
Possibility 1 – IDC-based area Undertaking Function reuse
As a substitute of making a brand new execution position and tagging it, you may configure the IAM-based area undertaking to straight reuse the patron undertaking IAM position from the IDC-based area because the execution position. This feature solely wants coverage adjustments to the patron undertaking IAM position. To seek out the IDC-based area client undertaking IAM position:
- Navigate to the Amazon SageMaker Unified Studio IDC-based area portal.
- Open the Advertising Client Undertaking.
- Copy the undertaking position ARN from the undertaking overview web page.
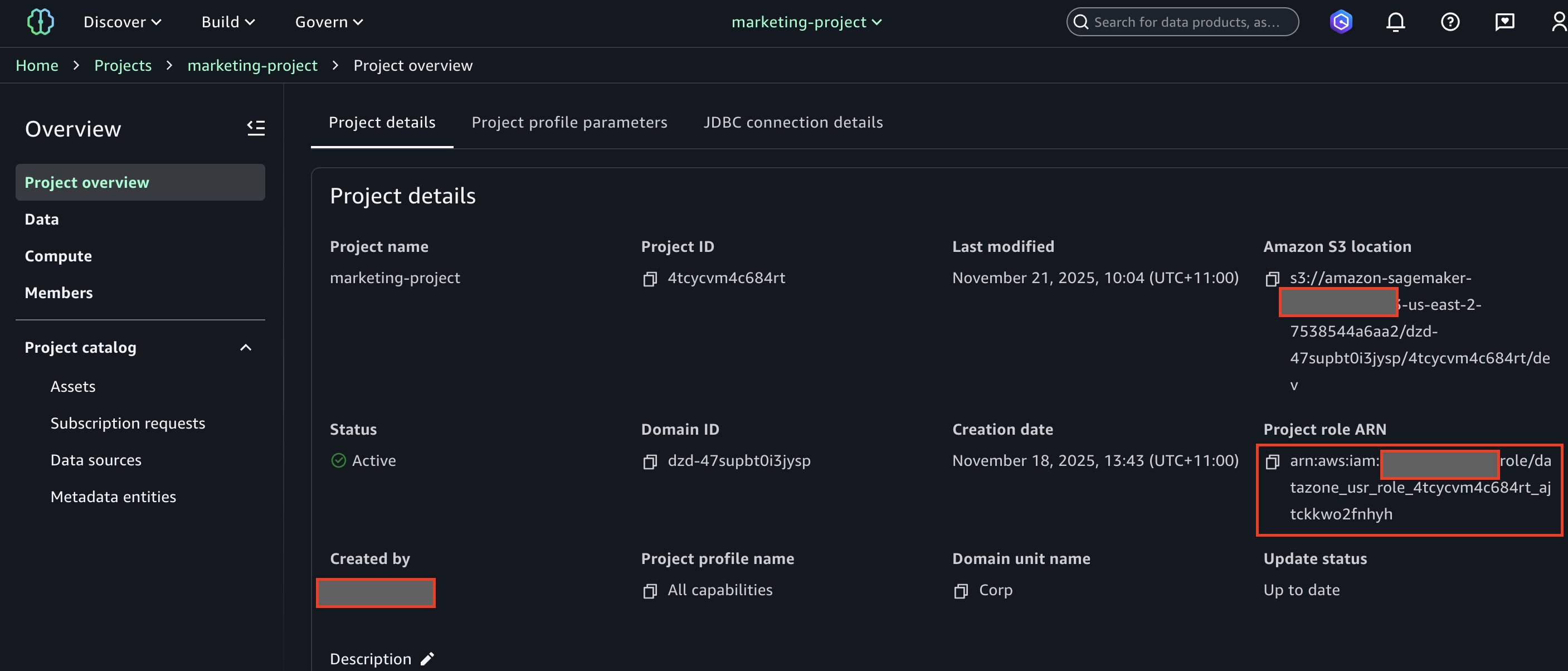
- You have to to switch this execution position’s coverage with detailed directions supplied later within the weblog.
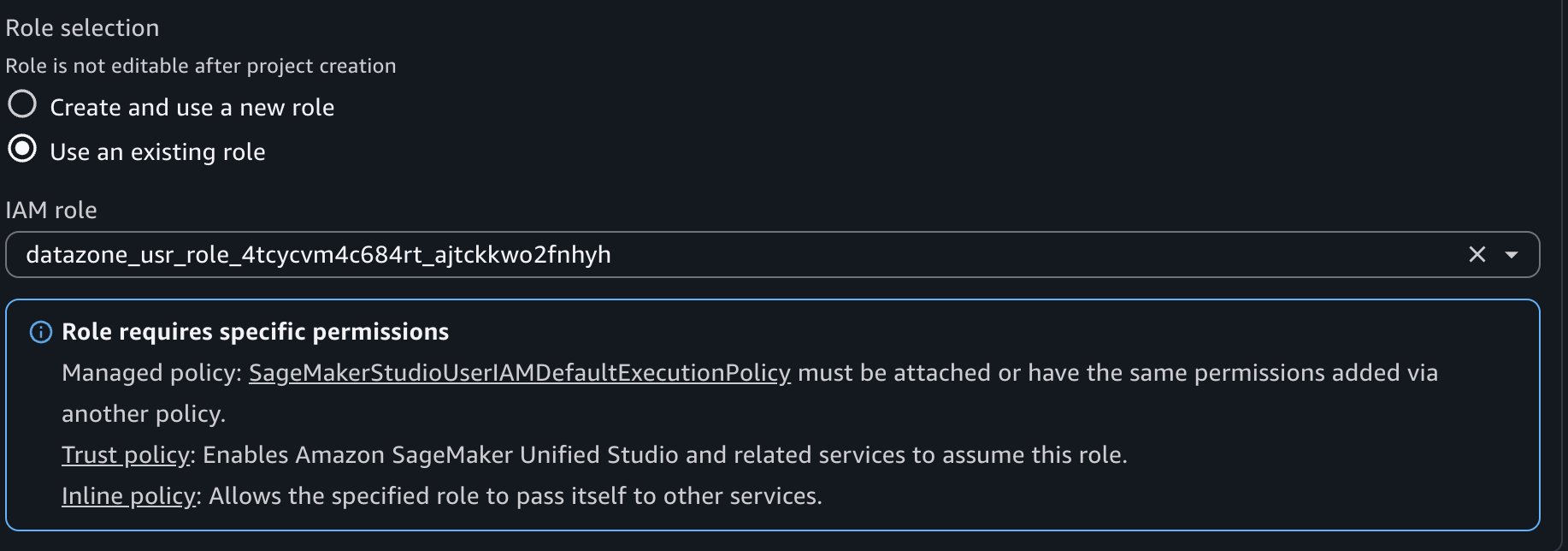
Organising IAM-based area undertaking for choice 1
To create an IAM-based area undertaking that may combine together with your present IDC-based area permissions, full the next steps:
- Log in to the AWS Console utilizing IAM-based area administrator.
- Navigate to Amazon SageMaker web page inside console.
- Select Open.
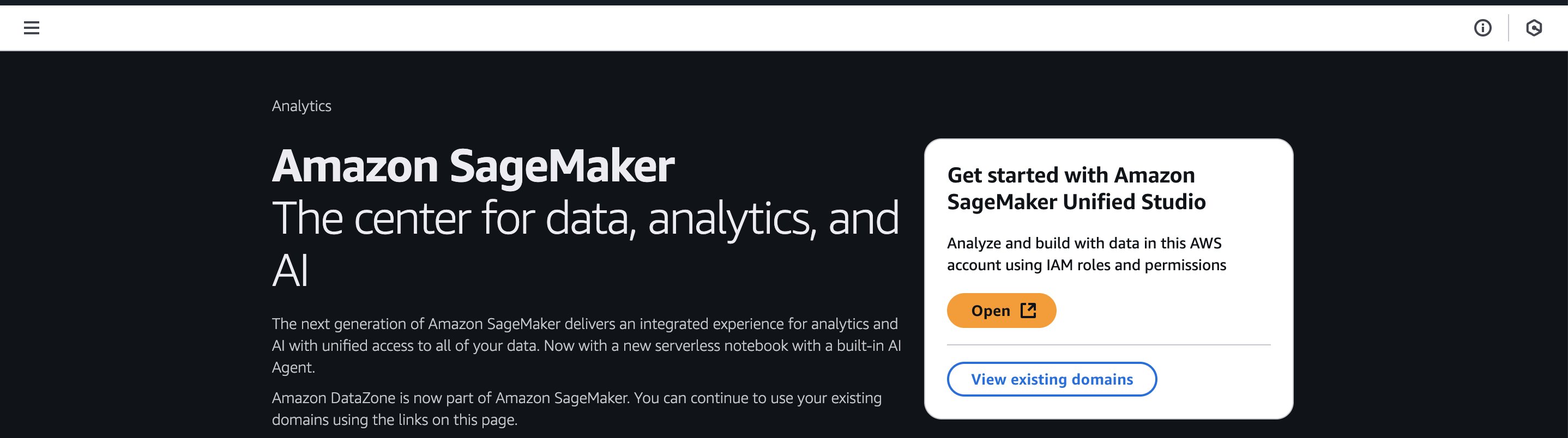
- As soon as logged in to IAM-based area as admin, select Handle tasks.
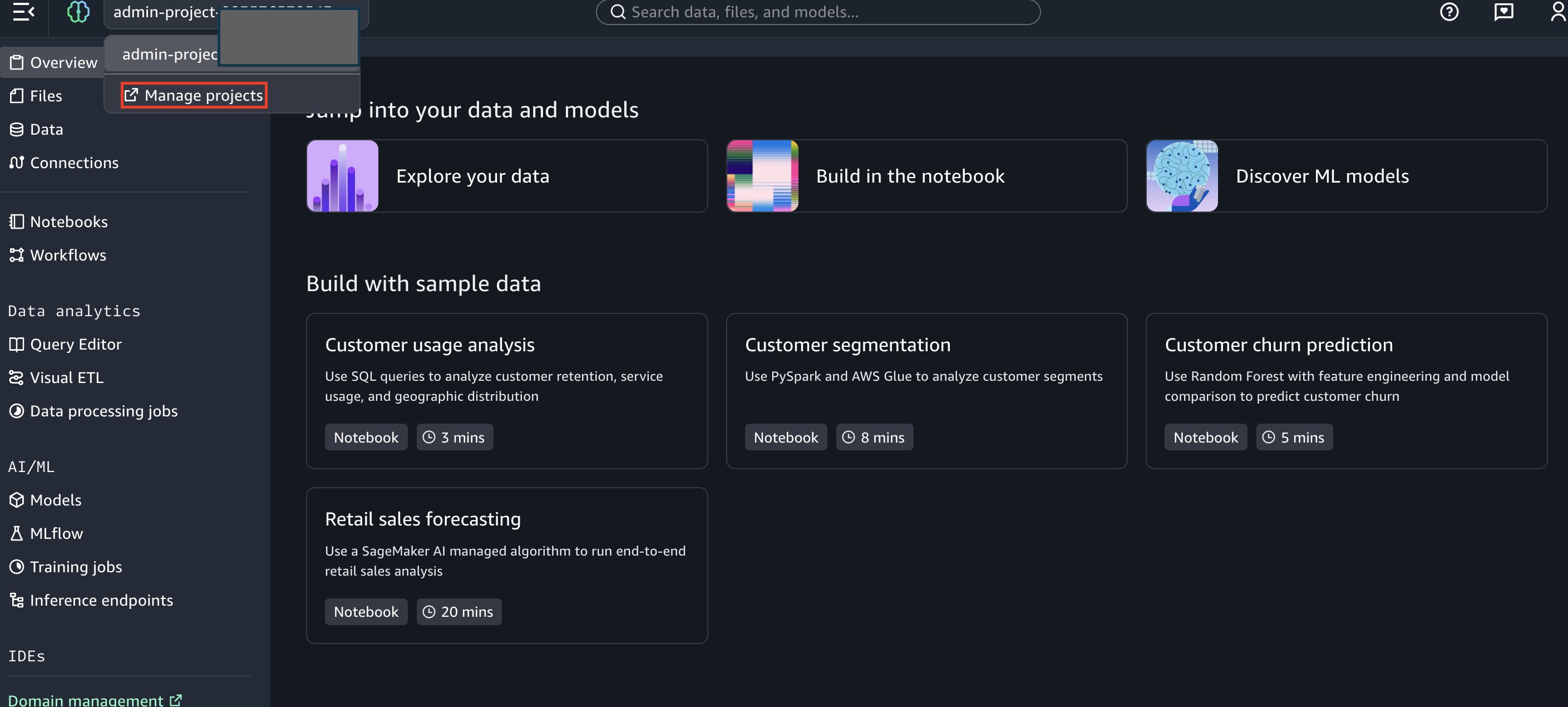
- Subsequent, click on on Create Undertaking.
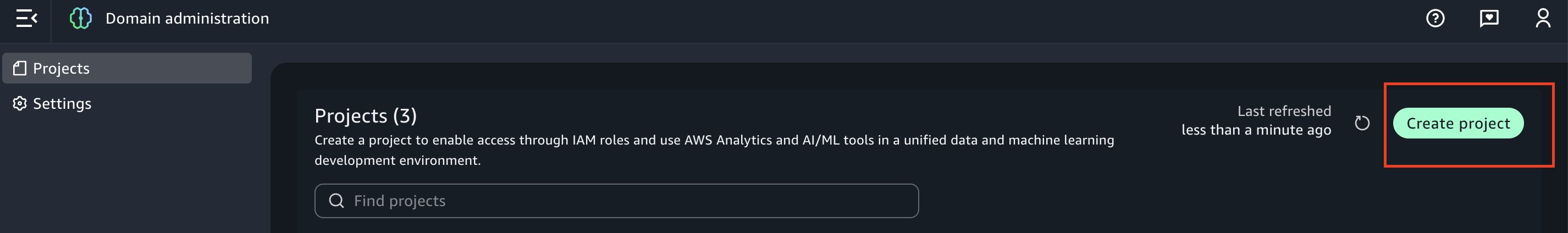
- Enter undertaking identify as “Advertising Client Undertaking”.
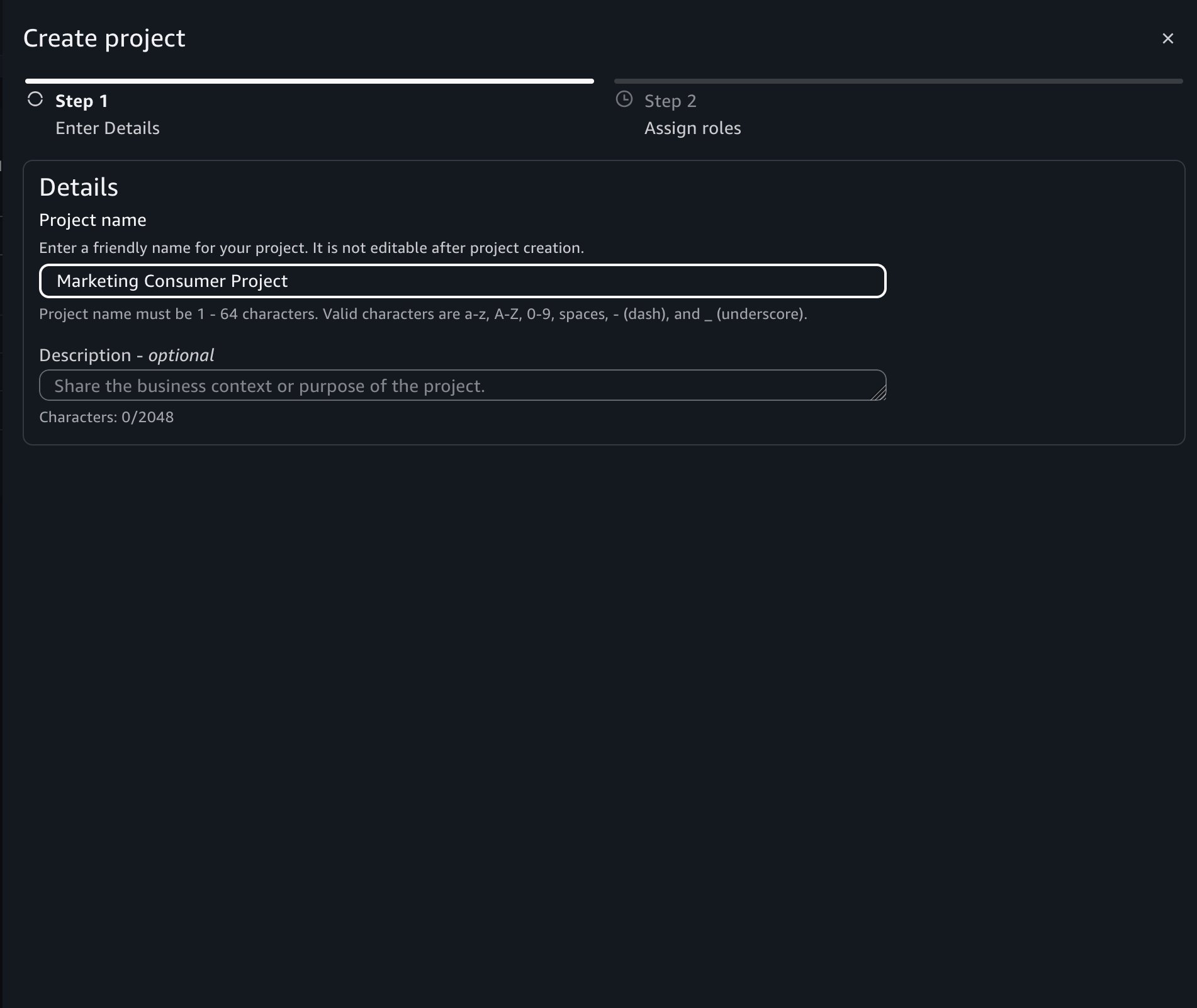
- Throughout undertaking creation, choose the next essential roles after which select Create Undertaking:
- Undertaking IAM Function: The advertising federated position created in IAM Id Middle above. That is the position within the member account that has a job identify with suffix
AWSReservedSSO. - Undertaking Function: – Select undertaking position for information engineer, copied from choice 1.
- Make coverage adjustments to this undertaking position as per the instruction on the SMUS UI web page.
Possibility 2 – Convey your personal execution position.
To create an IAM-based area undertaking that may combine together with your present IDC-based area permissions., you will need to tag the execution position for permission propagation. Amazon SageMaker Catalog and AWS Lake Formation use attribute-based entry management, which suggests permissions may be inherited based mostly on useful resource tags. For this feature, you have to client undertaking ID.To seek out the IDC-based area client undertaking ID:
- Navigate to the Amazon SageMaker Unified Studio IDC-based area portal.
- Open the Advertising Client Undertaking.
- Copy the undertaking ID from the undertaking particulars.
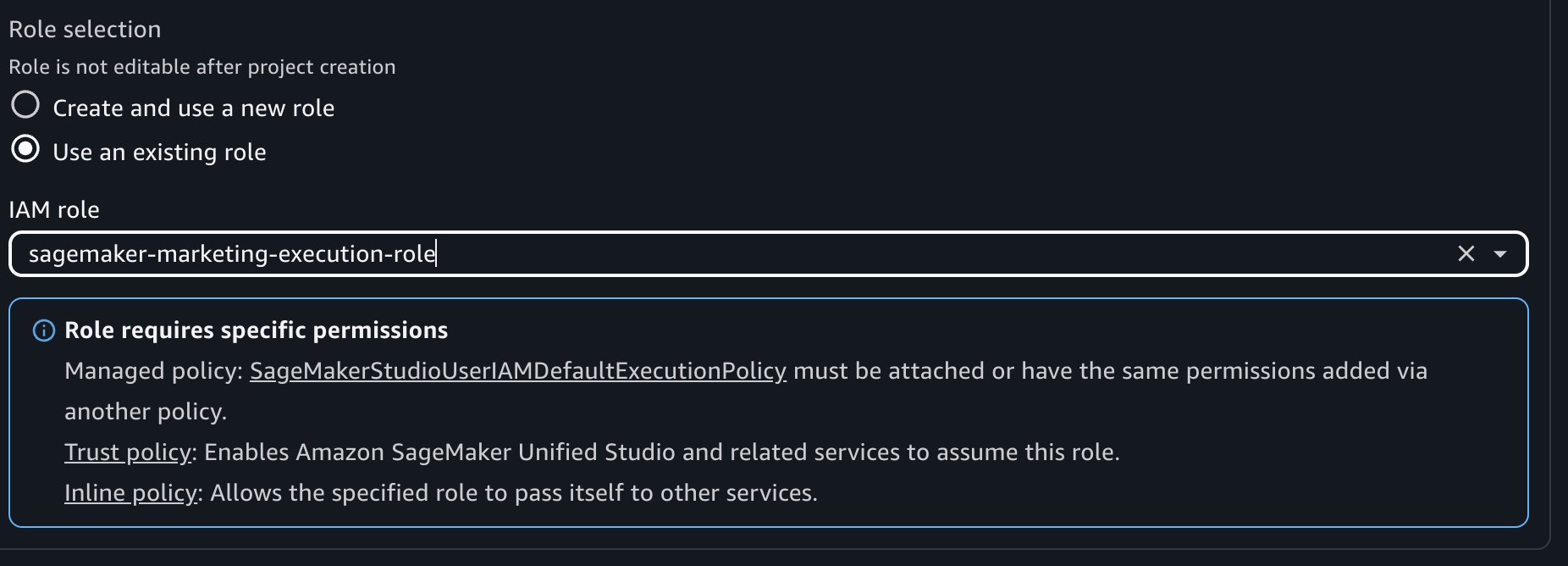
Organising IAM-based area undertaking for choice 2
Full the next steps:
- Create one other undertaking with identify “Advertising Client Undertaking 2” within the IAM-based area whereas logged in as admin.
- Throughout undertaking creation, choose the next roles:
- Federated Function: The advertising federated position created in IAM Id Middle above.
- Execution Function: – Select execution position from choice 2.
- Make coverage adjustments to this execution position as per the instruction.
- Subsequent, navigate to the IAM console and find the execution position created in your IAM-based area client undertaking.
- Add the next tag, this step depends on ABAC insurance policies with
projectIdfor subscriptions.
- Key:
AmazonDatazoneProject - Worth: The undertaking ID out of your Amazon SageMaker Unified Studio IDC-based area client undertaking
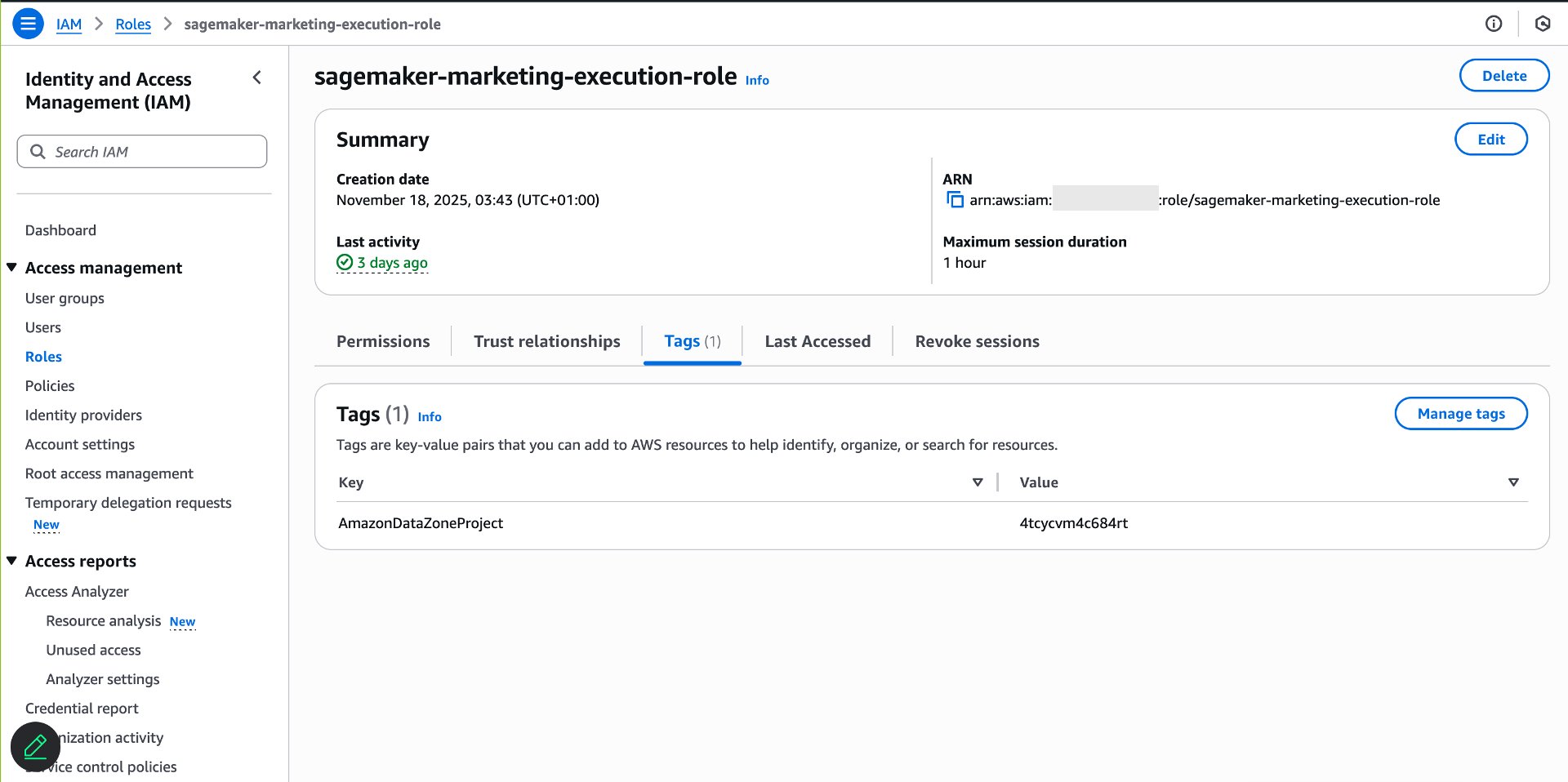
This tag configuration leads to information entry grant from IDC-based area client undertaking to the IAM-based area undertaking execution position.
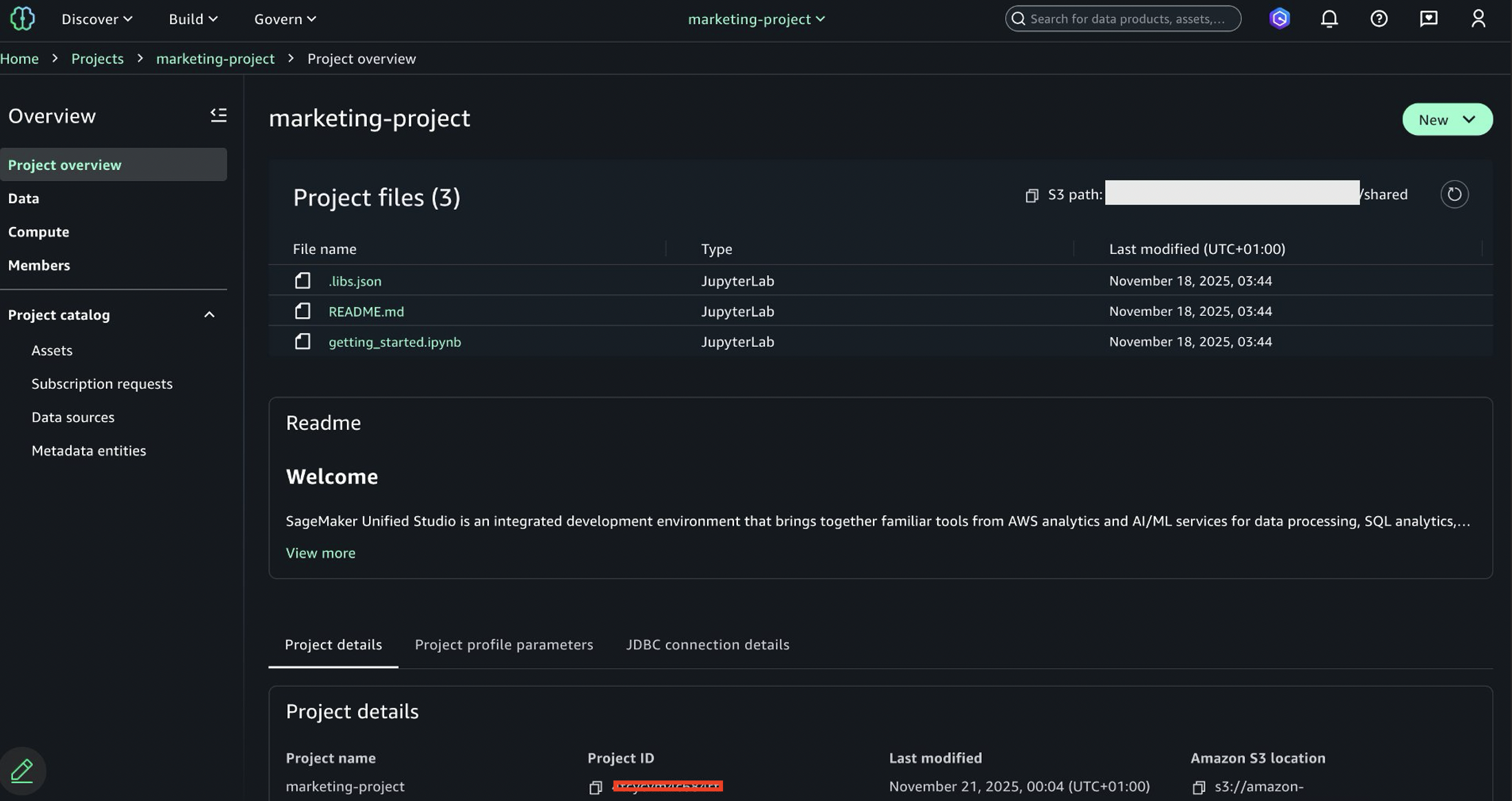
Confirm information entry within the IAM-based area
After tagging the execution position, confirm that permissions are arrange appropriately.Full the next steps:
- Use the SSO URL to log into the SSO Id Middle as Sarah.
- Open the AWS console utilizing federated position created earlier in setting federated position part.
- Navigate to Amazon SageMaker.
- Select Amazon SageMaker Unified Studio IAM-based area choice (this can present up if undertaking is already created with federated position).
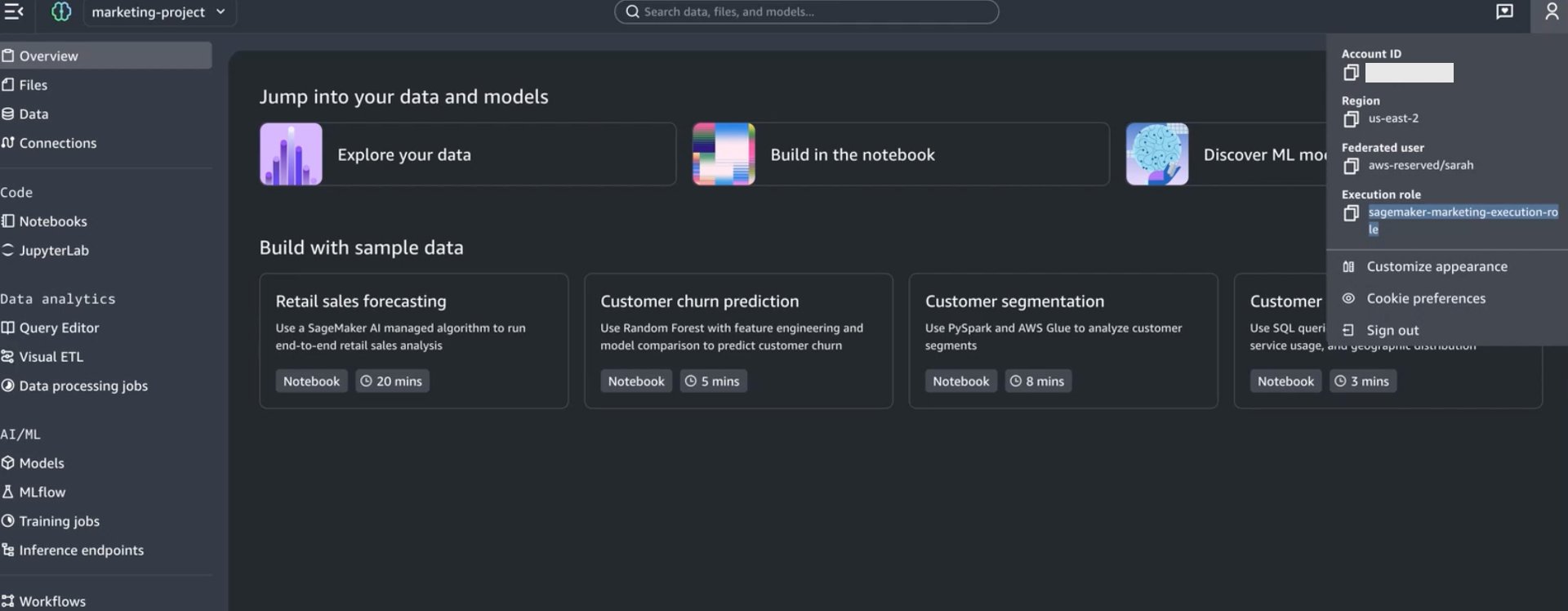
- Within the Amazon SageMaker Unified Studio IAM-based area undertaking, navigate to the Information tab. If you happen to created 2 tasks with each choice 1 and choice 2 execution position, then 2 tasks will present up and you’ll login to both to validate information entry.
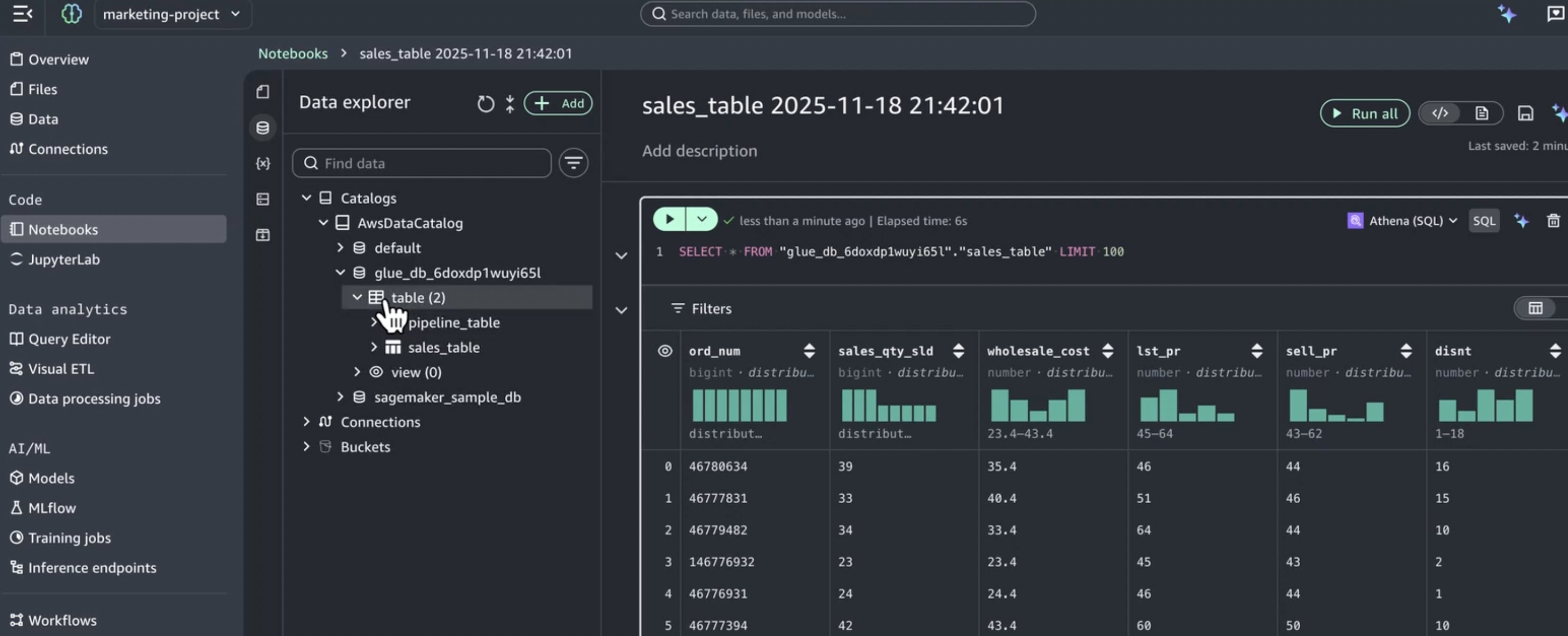
- Confirm that the patron database and subscribed tables seem.
Create and use the brand new serverless notebooks
With permissions correctly configured, now you can use IAM-based area capabilities like serverless Notebooks. Full the next steps:
- Within the Amazon SageMaker Unified Studio IAM-based area undertaking, choose a desk from the Information tab.
- Select Create pocket book.
- The Pocket book opens with Athena SQL because the default cell sort.
- Write and run queries towards your subscribed information.
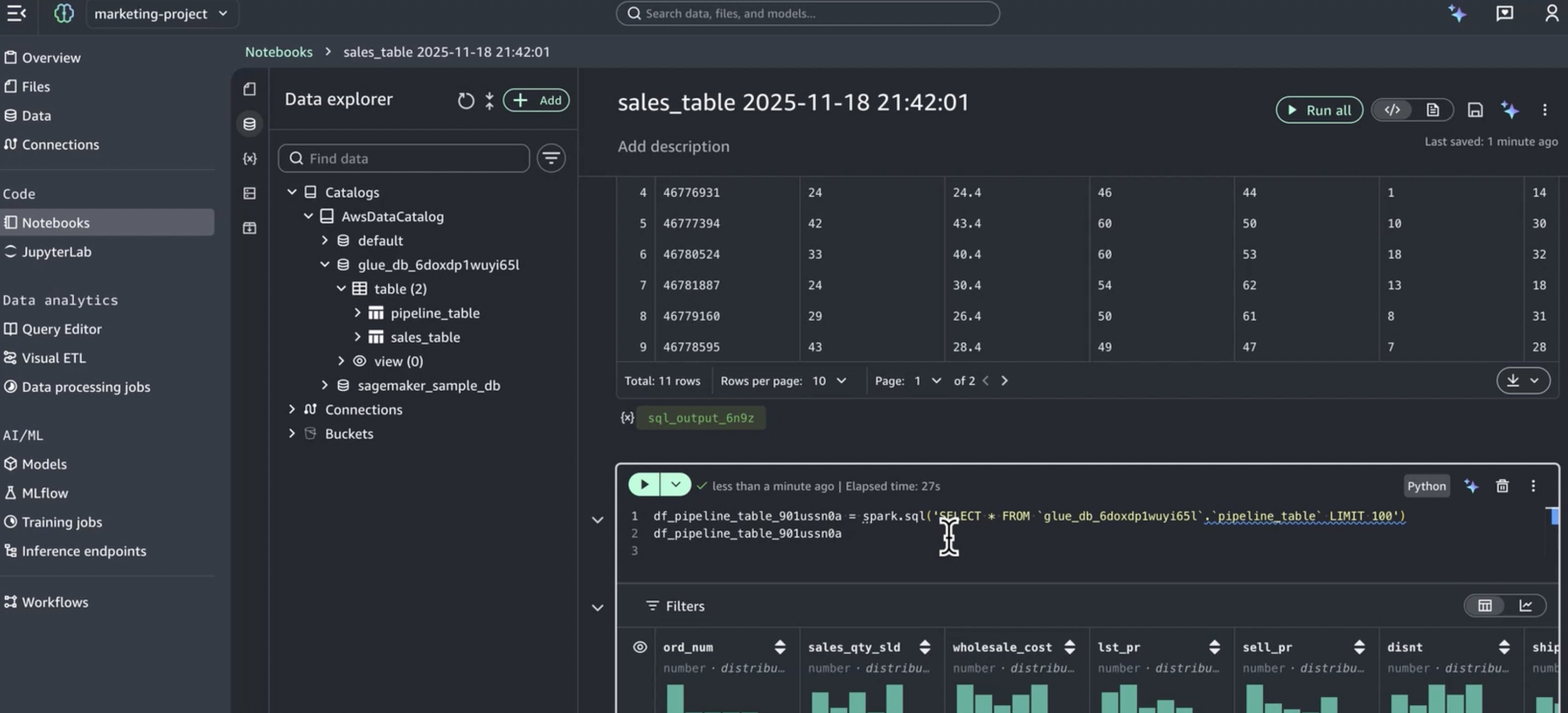
The pocket book runs with the execution position’s permissions, which now embrace entry to all information subscribed by way of the IDC-based area.
Key advantages of this integration
This integration method delivers a number of essential benefits:
Protect present investments
- Proceed utilizing IDC-based area governance and catalogs.
- Preserve established Pub/Sub workflows.
- No migration required for present information belongings.
Get trendy capabilities
- Present builders with the brand new serverless Notebooks.
- Entry Athena Spark for superior analytics.
- Supplies improved consumer expertise and navigation.
Simplified permission administration
- Single subscription workflow manages entry throughout each domains.
- Constant information entry by way of position reuse and attribute-based entry management.
- No duplicate entry requests or approvals wanted.
Unified information expertise
- Builders entry all subscribed information from one interface.
- Constant information catalog throughout domains.
- Simplified onboarding for brand spanking new group members.
Cleanup
Full the next steps to delete the sources you created:
- Delete the serverless Notebooks created within the IAM-based area tasks.
- Delete the IAM-based area tasks (Advertising Client Undertaking and Advertising Client Undertaking 2).
- Take away the permission set project from advertising group in IAM Id Middle.
- Delete the Advertising-federated-role permission set in IAM Id Middle.
- Take away the tags (AmazonDatazoneProject) from the execution position (if utilizing Possibility 2).
- Delete the execution position created for the IAM-based area (if utilizing Possibility 2 and never reusing the IDC-based area undertaking position).
- Revert any coverage adjustments made to the IDC-based area client undertaking IAM position (if utilizing Possibility 1).
- If you don’t want the IAM-based area anymore, delete it.
- If you happen to created any check information subscriptions within the IDC-based area, take away them.
Conclusion
On this put up, we demonstrated learn how to entry Amazon SageMaker Unified Studio IDC-based area with the brand new IAM-based area utilizing position reuse and attribute-based entry management. This setup gives information engineers the most effective of each worlds: entry to specialised trendy improvement instruments—together with the brand new serverless Notebooks, Athena Spark integration, and built-in AI help , whereas sustaining correct governance that features complete catalog administration and strong safety controls established within the IDC-based area.Now you can confidently undertake Amazon SageMaker Unified Studio IAM-based area capabilities realizing their established information governance, subscription workflows, and entry controls stay intact and proceed to perform as anticipated.
Able to get began with Amazon SageMaker Unified Studio and unlock the facility of built-in governance and trendy improvement instruments in your group? Go to the Amazon SageMaker Unified Studio documentation to be taught extra and start your implementation in the present day.
Concerning the authors

